Trojan.HTML.PHISH.QURAAOOIUE
Trojan:HTML/Phish!MSR (MICROSOFT)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It does not have any backdoor routine.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Propagation
This Trojan does not have any propagation routine.
Backdoor Routine
This Trojan does not have any backdoor routine.
Rootkit Capabilities
This Trojan does not have rootkit capabilities.
Information Theft
This Trojan gathers the following account information:
- Specific Email
- Input Password
Stolen Information
This Trojan sends the gathered information via HTTP POST to the following URL:
- https://{BLOCKED}nova.com.ge/boss/lambo.php
Other Details
This Trojan does the following:
- It disguises itself as a login page to access a document:
- It disables the following keyboard shortcuts and mouse actions when interacting with the fake login page:
- CTRL+C - used to copy text or items from the webpage
- CTRL+V - used to paste text or items on the webpage
- CTRL+A - used to select all text or items on the webpage
- CTRL+F - used to search text on the webpage
- CTRL+H - used to open the browsing history
- CTRL+E - used to access the address bar
- CTRL+S - used to save the webpage
- CTRL+U - used to view the page source
- F12 - used to view the page source
- CTRL+F6 - used to skip to contents
- CTRL+SHIFT+I - used to open the Developer Tools
- CTRL+SHIFT+J - used to open the console tab in Developer Tools
- Browser's Context Menu - usually done by clicking the right mouse button
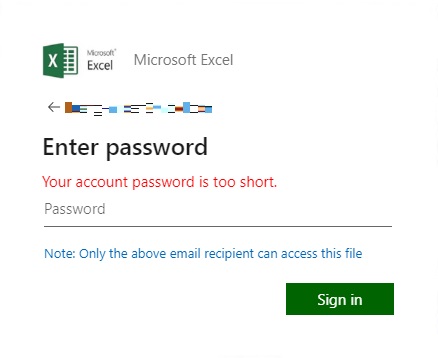
- If the input password has less than 5 characters, it displays the following message:
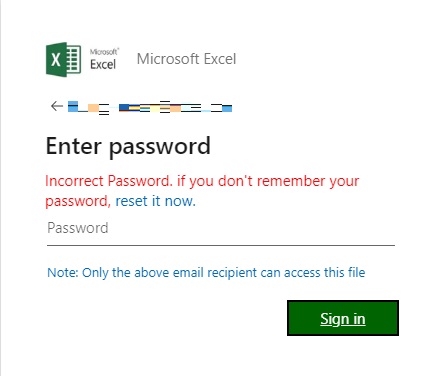
- If the input password has more than 5 characters and submitted for the first time, it sends the email and input password to the C&C Server. Then, it displays the following message to bait the victim to carefully input the correct password again:
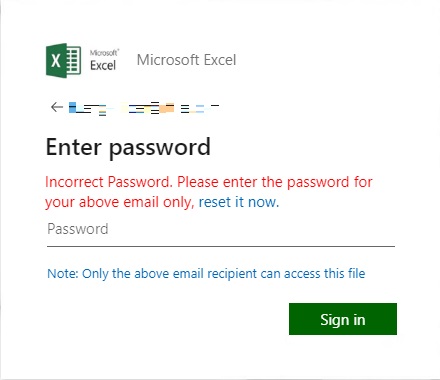
- If the input password has exactly 5 characters and submitted for the first time, or if the password has 5 or more characters and submitted the second time, it sends the email and input password to the C&C Server. Then, it displays the following message:
- If the input password has 5 or more characters and submitted for the third time, it sends the email and input password to the C&C Server and loads the following webpage:
- It initially connects to the following URL to load the fake login page:
- https://{BLOCKED}ess-zebrax0x.surge.sh/excelUILOGO.js
- It redirects the webpage to the following URL to load the error page:
- https://{BLOCKED}k.office365.com/Encryption/ErrorPage.aspx?src=3&code=11&be=SN6PR04MB4014&fe=JNAP275CA0040.ZAFP275.PROD.OUTLOOgK.COM&loc=en-US&itemID=E4E_M_e9df154a-e4b8-4486-8aec-7acceeb93fee
- It connects to the following URLs to display images inside the webpage:
- https:/{BLOCKED}o.com/9c58a897ff8731c750bc9ec6fefffc26.png
- https://{BLOCKED}o.com/78c24d6313b46234ef3d411883c0aa32.png
- https://{BLOCKED}.msftauth.net/shared/1.0/content/images/favicon_a_eupayfgghqiai7k9sol6lg2.ico
- https://{BLOCKED}.msftauth.net/shared/1.0/content/images/arrow_left_7cc096da6aa2dba3f81fcc1c8262157c.png
- https://{BLOCKED}.msftauth.net/shared/1.0/content/images/arrow_left_a9cc2824ef3517b6c4160dcf8ff7d410.svg
- https://{BLOCKED}.msftauth.net/shared/1.0/content/images/microsoft_logo_ed9c9eb0dce17d752bedea6b5acda6d9.png
- https://{BLOCKED}.msftauth.net/shared/1.0/content/images/microsoft_logo_ee5c8d9fb6248c938fd0dc19370e90bd.svg
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as Trojan.HTML.PHISH.QURAAOOIUE. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.



