LogJam: New Discovery Reveals Old Flaw
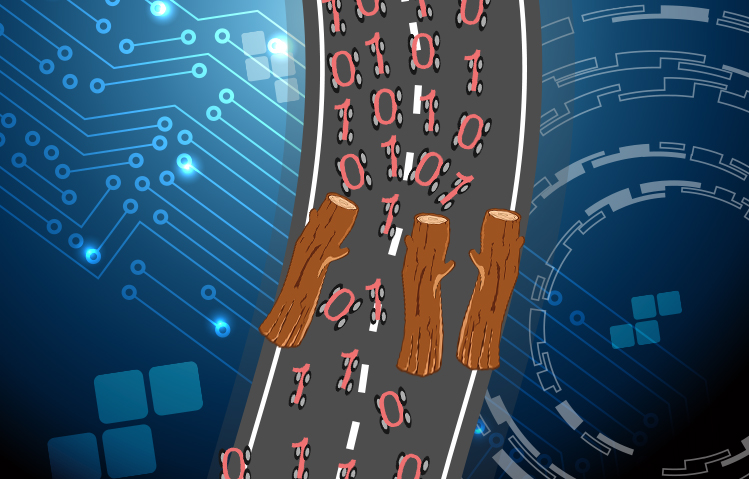 A new encryption flaw has been found that puts a significant number of Internet users' data at risk. Dubbed as LogJam, the flaw affects websites, mail servers, and other frequently-used Internet services by allowing an attacker to weaken what is believed to be a secure encrypted connection between a user and a server.
A new encryption flaw has been found that puts a significant number of Internet users' data at risk. Dubbed as LogJam, the flaw affects websites, mail servers, and other frequently-used Internet services by allowing an attacker to weaken what is believed to be a secure encrypted connection between a user and a server.
In essence, this weakness could be used to empower a cybercriminal with the right resources to mount a man-in-the-middle attack to sniff on and modify communications that are known to be “secure”. To Matthew Green, cryptographer and professor at John Hopkins University, along with a group of researchers, this flaw harks back to the 1990s as an indirect offshoot of a US-government mandate to limit the levels of encryption of products exported abroad, to allow them to easily spy on enemies.
Decades after the policy was lifted, the gates remain unsealed. According to the site put up by the researchers, 8.4 percent of the top 1 million domains, as well as a significant number of existing email servers that support SMTP with StartTLS, POP3S, and IMAPS, have been identified as vulnerable to this weakness.
LogJam’s activities are reminiscent of the FREAK vulnerability discovered in March. FREAK forces a secure connection to utilize weaker encryption that makes it easy for cybercriminals to pounce on sensitive information.
Green and his fellow researchers have determined that the problem in a weakness found on the Diffie-Hellman key exchange. Websites and email servers make use of SSL (Secure Sockets Layer) or TLS (Transport Layer Security) protocols to create a secure connection among users. The Diffie-Hellman key exchange is primarily responsible for the communication and exchange of encryption keys that are used to secure a connection.
The LogJam attack makes it easy to lower TLS connections to the level of those that use 512-bit “export-grade” encryption. In turn, cybercriminals can dupe a server into accepting weaker encryption, thinking it is secure enough. This then gives them the chance to intercept the data that passes through the connection.
As of this writing, researchers have indicated that major browsers by Mozilla, Google, Microsoft, and Apple, among others, are working on fixes to address this vulnerability. This issue brings to the fore the importance of keeping systems up to date not just for end users but for software developers as well. IT administrators using servers that are known to use any of the services and protocols at risk are advised to disable support for all export cipher suites to thwart attempts for compromise, and prevent using Diffie-Hellman key exchange lower than 2048-bits to steer clear of possible interception. Internet users are likewise advised to make sure that browsers are up to date, and to check for updates frequently.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Messages récents
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
- The Industrialization of Botnets: Automation and Scale as a New Threat Infrastructure

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: DragonForce
Ransomware Spotlight: DragonForce Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One