ELF_XORDDOS.AP
DoS:Linux/Xorddos.A (Microsoft); HEUR:Trojan-DDoS.Linux.Agent.g (Kaspersky); Linux.Xorddos!gen1 (Symantec); Linux/DDoS.XOR (AVG); ELF:Xorddos-M [Trj] (Avast);
Unix, Linux


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware launched distributed denial of service (DDoS) attacks to a number of gaming- and education-related websites. Its communication with its servers are encrypted via XOR, hence the name.
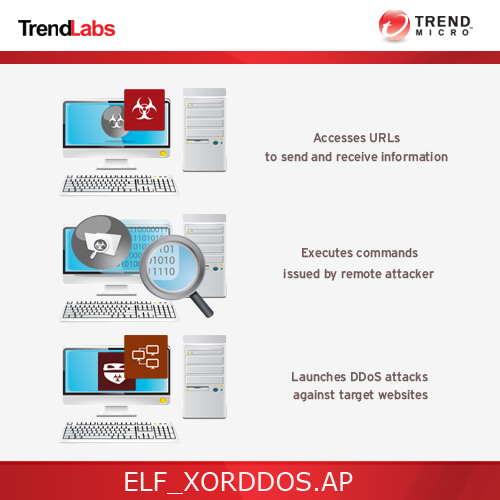
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system. It connects to a website to send and receive information.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This backdoor drops the following copies of itself into the affected system:
- /var/run/udev.pid
- /lib/libgcc4.so
Autostart Technique
This backdoor drops the following files:
- /etc/cron.hourly/udev.sh (Cron is a time-based job scheduler in Unix-like computer operating systems)
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Start Denial of Service
- Stop Denial of Service
- Update malware
- Download and execute file
- Terminate Process
- Request MD5 Hash of running malware
It connects to the following websites to send and receive information:
- gh.{BLOCKED}a1.org:2833
- www.{BLOCKED}ngfacai.com:2833
- {BLOCKED}.{BLOCKED}.31.154:2833
- {BLOCKED}.{BLOCKED}.9.229
- {BLOCKED}.{BLOCKED}.9.228
Download Routine
This backdoor connects to the following URL(s) to download its configuration file:
- http://info1.{BLOCKED}c.com/b/u.php?id=01
NOTES:
This backdoor drops a shell script in /etc/init.d folder which setups the autostart mechanism of the malware.
This backdoor creates five shortcut links which points to the script in /etc/init.d:
- /etc/rc1.d/S90{random value}
- /etc/rc2.d/S90{random value}
- /etc/rc3.d/S90{random value}
- /etc/rc4.d/S90{random value}
- /etc/rc5.d/S90{random value}
This malware is capable of doing the following flooding attack:
- TCP Flood
- UDP Flood
- SYN Flood
- DNS Flood
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as ELF_XORDDOS.AP. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


