Risques liés à la & confidentialité
Complete Guide to Protecting Seven Attack Vectors
The quicker a cyberattack is identified, the less it costs. Jon Clay, VP of Threat Intelligence, reviews seven key initial attack vectors and provides proactive security tips to help you reduce cyber risk across the attack surface.
Digital transformation and remote work have rapidly expanded the attack surface. As the collection of applications, websites, accounts, devices, cloud infrastructure, servers, and operational technology (OT) continue to increase, attack surface management becomes more challenging as well. Unsurprisingly, 73% of IT and business leaders polled in a Trend Micro global study said they’re concerned with the size of their digital attack surface.
Effective attack surface risk management (ASRM) starts with the proactive defense of initial attack vectors rather than reactive defense after malicious actors have already breached your network. According to IBM’s 2024 Cost of a Data Breach Report, attack vectors with longer mean times to identify and contain were among the most expensive types of breaches.
In this blog, I review the seven key initial attack vectors to help chief intelligence security officers (CISOs) and security leaders strengthen their ASRM security strategy and reduce cyber risk.
Seven initial attack vectors
Read ahead:
1. Email
The risks
Email remains one of the most common initial attack vectors for cybercriminals due to its ease of manipulation. In 2023, 73.8 billion of over 161 billion total threats blocked by Trend were email-based. The expense tied to these attacks is growing as well; according to IBM’s 2024 Cost of a Data Breach Report, phishing cost enterprises US $4.88 million annually on average.
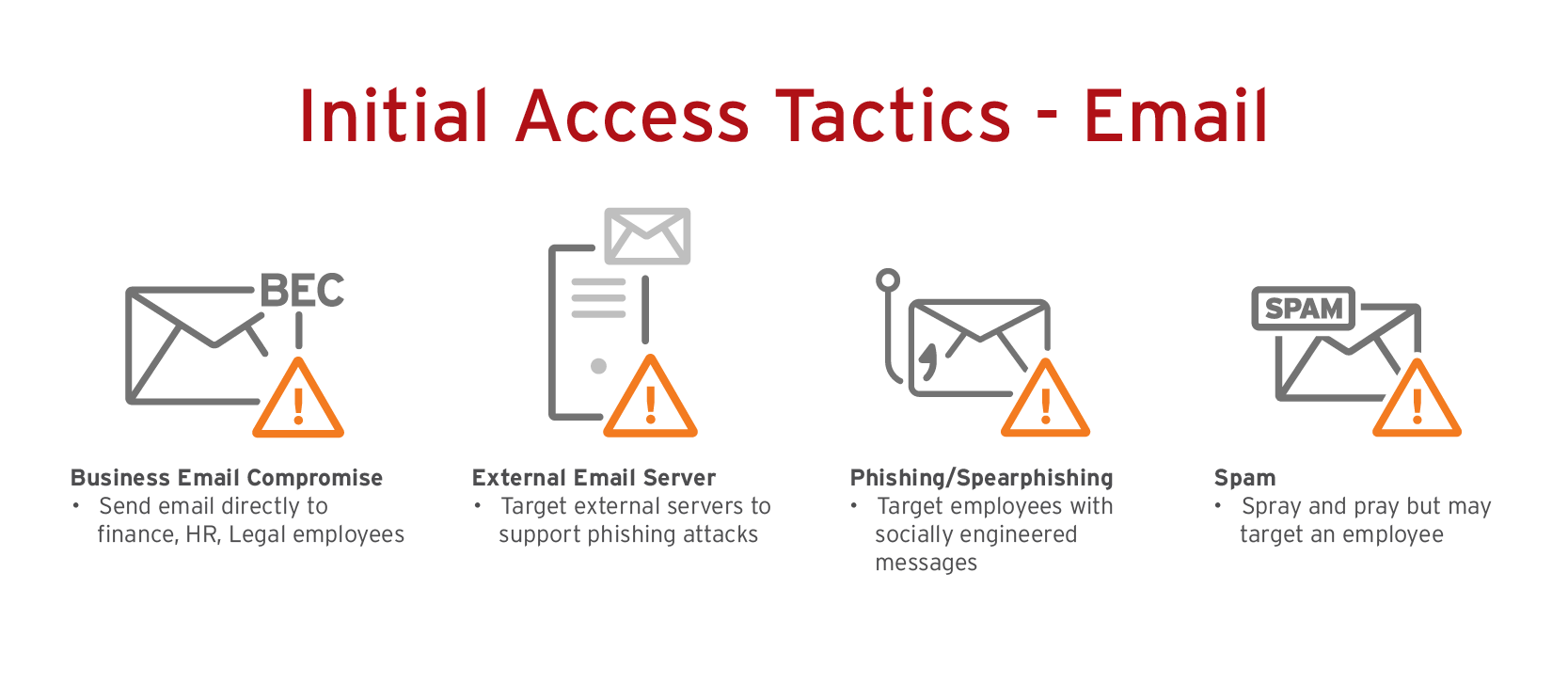
In addition, email-based attacks will get progressively harder to detect due to generative AI (GenAI) which can allow an adversary to craft phishing and business email compromise (BEC) messages in very realistic and enticing ways—and in any language. This further expands the pool of potential phishing targets.
What enterprises can do
Go beyond native email security by choosing a vendor with layered defense via the following technologies:
1. An email gateway, leveraging AI, ML, behavioral analysis, and authorship analysis;
2. Cloud application security broker (CASB) technology, analyzing inbox emails via the scanning of links, attachments, and messages between peers to prevent compromised accounts from phishing other employees;
3. A secure web gateway (SWG), providing additional protection if a malicious link is clicked by inspecting traffic inline, performing image analysis, and using ML to analyze branded elements, login forms, and other site content to recognize fake websites;
4. User education via built-in security awareness simulations and training where, ideally, the vendor will offer phishing tests based on templates extracted from recent, real phishing scams
2. Web and web applications
The risks
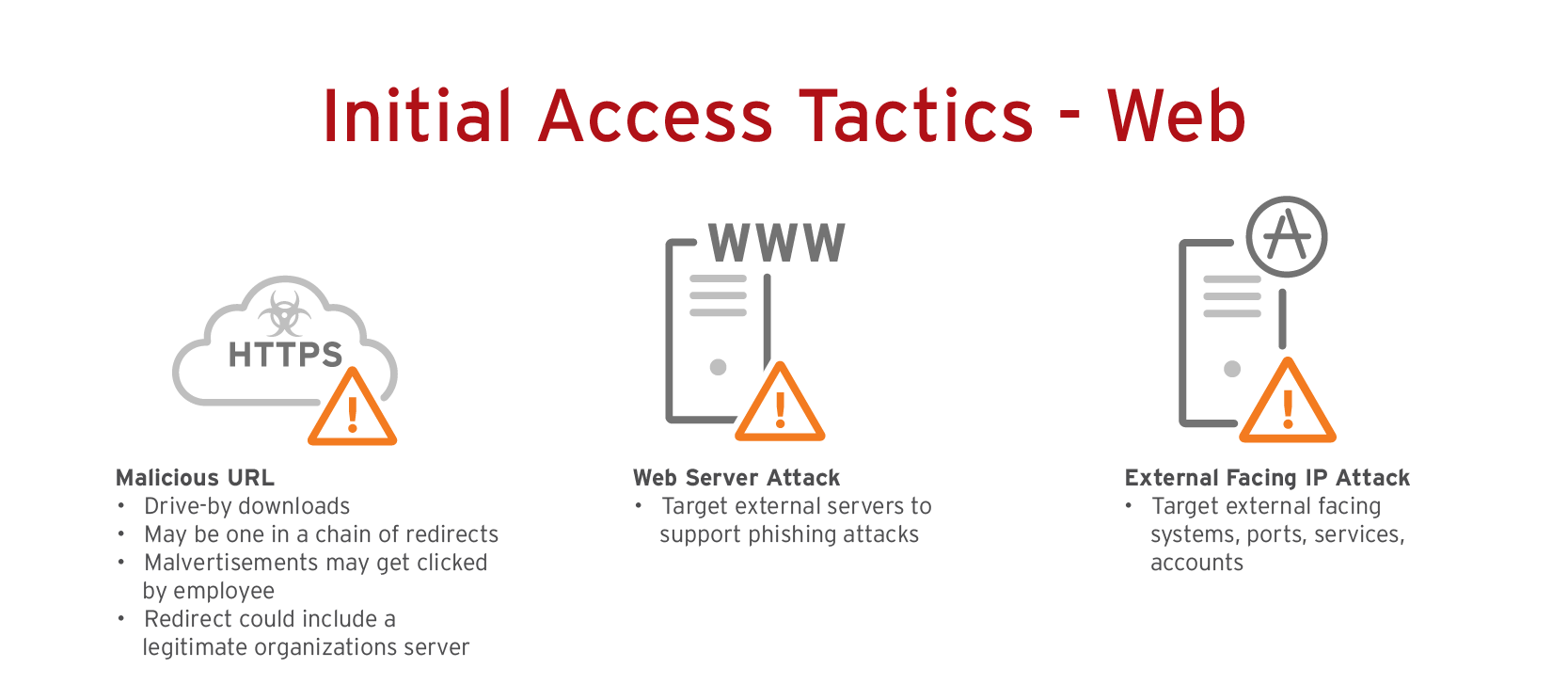
Cross-site scripting (XSS) attacks take advantage of coding flaws on websites or web applications to generate input from users. It’s no wonder why XSS remains a mainstay on the Open Web Application Security Project (OWASP) Top 10 Web Application Security Risks—a severe XSS vulnerability in Ivory Search, a WordPress search plugin, left 60,000 websites open to malicious code injection. With remote work and the shift to cloud services resulting in a boom of websites and applications, enterprises need to strengthen their defense for this initial attack vector.
What you can do
Consider taking the following three actions to help minimize your risk:
- Patch any vulnerabilities
- Scan for malicious scripts
- Disable any ports not needed on web servers
In addition, CASB can help you reduce the risks of using software-as-a-service (SaaS) apps without impacting the user experience. It counters shadow IT, secures cloud account compromises, and addresses security gaps for third-party services like Ivory Search. Furthermore, CASB complements the threat-blocking capabilities of SWG solutions and benefits from integration with the analytical power of extended detection and response (XDR).
The disparate logs of these once-discrete solutions combine to offer a more holistic view of your environment, allowing for the creation of a more thorough risk profile.
3. Vulnerabilities
The risks
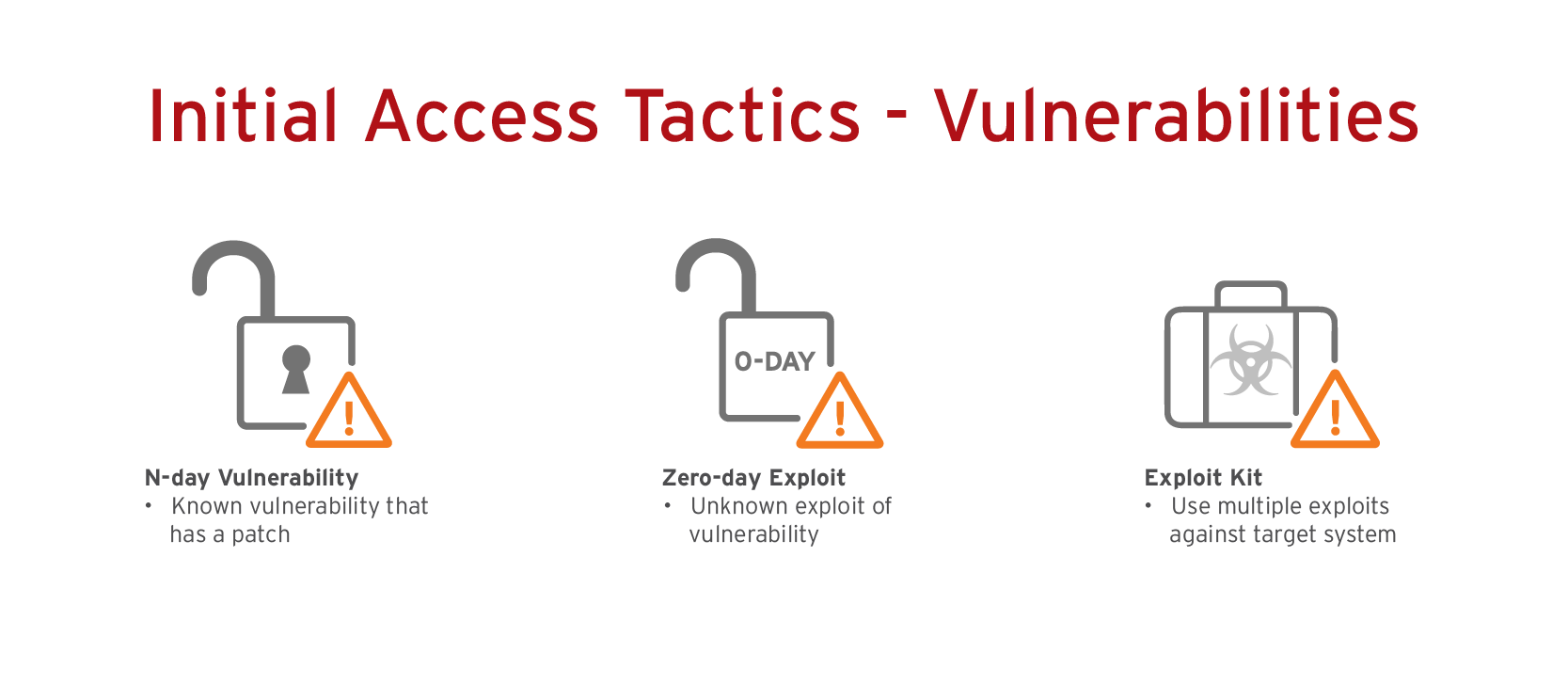
Vulnerabilities can disrupt business operations by causing system blackouts or closures. Swedish grocery chain Coop, for example, was forced to shut down 800 stores after malicious actors leveraged multiple zero-day vulnerabilities in Kaseya’s Virtual System Administrator (VSA) product to launch a ransomware attack.
In addition, zero-days, n-days, and forever-days continue to increase. Trend™ Research reported a 23% increase in the number of critical and high-severity vulnerabilities during the first half of 2022 submitted to the Trend Micro™ Zero Day Initiative™ (ZDI) bug bounty program.
What you can do
These five risk-based patch management best practices can help you create a strong defense program against vulnerability exploitation:
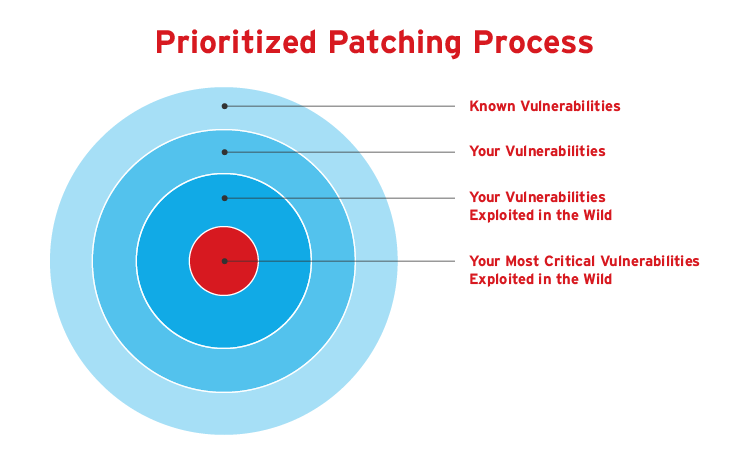
1. Identify which patches are most relevant using a prioritized patching process and checking the Cybersecurity and Infrastructure Security Agency (CISA) Known Exploited Vulnerability catalog.
2. Make a zero-day plan for when, not if by consistently monitoring networks for suspicious activity, and by staying up to date with bug bounty programs like ZDI that leverage global threat intelligence
3. Communicate with vendors about the possibility of rollbacks to previous versions of software
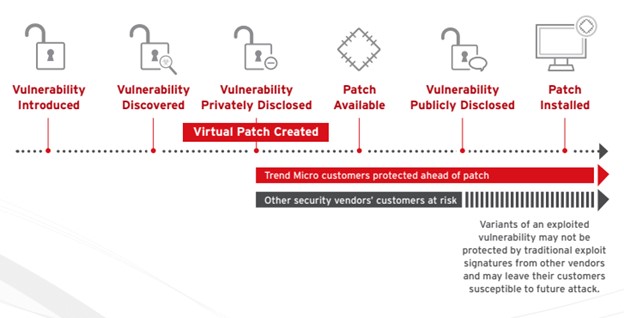
4. Utilize virtual patching to protect vulnerable systems while waiting for a vendor patch to be released
5. Share benefits with stakeholders to encourage a culture of security within the organization as well as demonstrate the ROI of cybersecurity to the board
The use of ASRM aligns with these steps in making your risk monitoring and measurement processes more streamlined, informed, and effective. Analyze a wide range of important elements including your asset criticality, vulnerabilities, security posture, threat activity, and exposure. Taking the guesswork out of what impacts your risk enables more effective decision-making, translating to a stronger risk response.
4. Devices
The risks
The shift to remote work exposed the dangers of virtual private networks (VPNs)—an initial attack vector which grants access to the entire network. While a remote worker may only access legitimate work apps, other devices in the household could spread malware through an unsecured machine connected to the VPN. And considering that 82% of data breaches involved a human element, more devices with access to an organization’s entire network effectively translates to higher cyber risk.

What you can do
63% of organizations are making the move from a VPN to zero trust network access (ZTNA) to reduce cyber risk across the attack surface as part of a broader zero trust strategy. ZTNA continuously verifies the trust of users and devices, and only grants access to the web-portal frontend, which stops a compromised device from leapfrogging their attack across the attack surface.
Furthermore, ZTNA provides the scalability needed to support evolving business operations. The specific application-to-user connection doesn’t require the bandwidth that VPNs do, enabling high-performance availability and consistent delivery without negatively impacting the user experience.
5. Island hopping
The risks
Island hopping, as the term implies, is used to pivot from an external environment into your network. Software supply chain attacks are increasing in frequency due to the success of those impacting Kaseya, Log4j, and SolarWinds. Within this initial attack vector lies many others including data distribution services (DDS), open-source code, system management tools, and purchased applications.
A Trend global survey reported that 52% of organizations have a supply chain partner that has been hit by ransomware, meaning their systems were at risk as well.

What you can do
The CISA-published Information and Communications Technology (ICT) Supply Chain Risk Management (SCRM) Essentials recommends six key steps to building effective software supply chain security:
1. Identify: Determine who needs to be involved
2. Manage: Develop your supply chain security policies and procedures based on industry standards and best practices, such as those published by the National Institute of Standards and Technology (NIST)
3. Assess: Understand your hardware, software, and services that you procure
4. Know: Map your supply chain to better understand what component you procure
5. Verify: Determine how your organization will assess the security culture of suppliers
6. Evaluate: Establish timeframes and systems for checking supply chain practices against guidelines
6. Insider
The risks
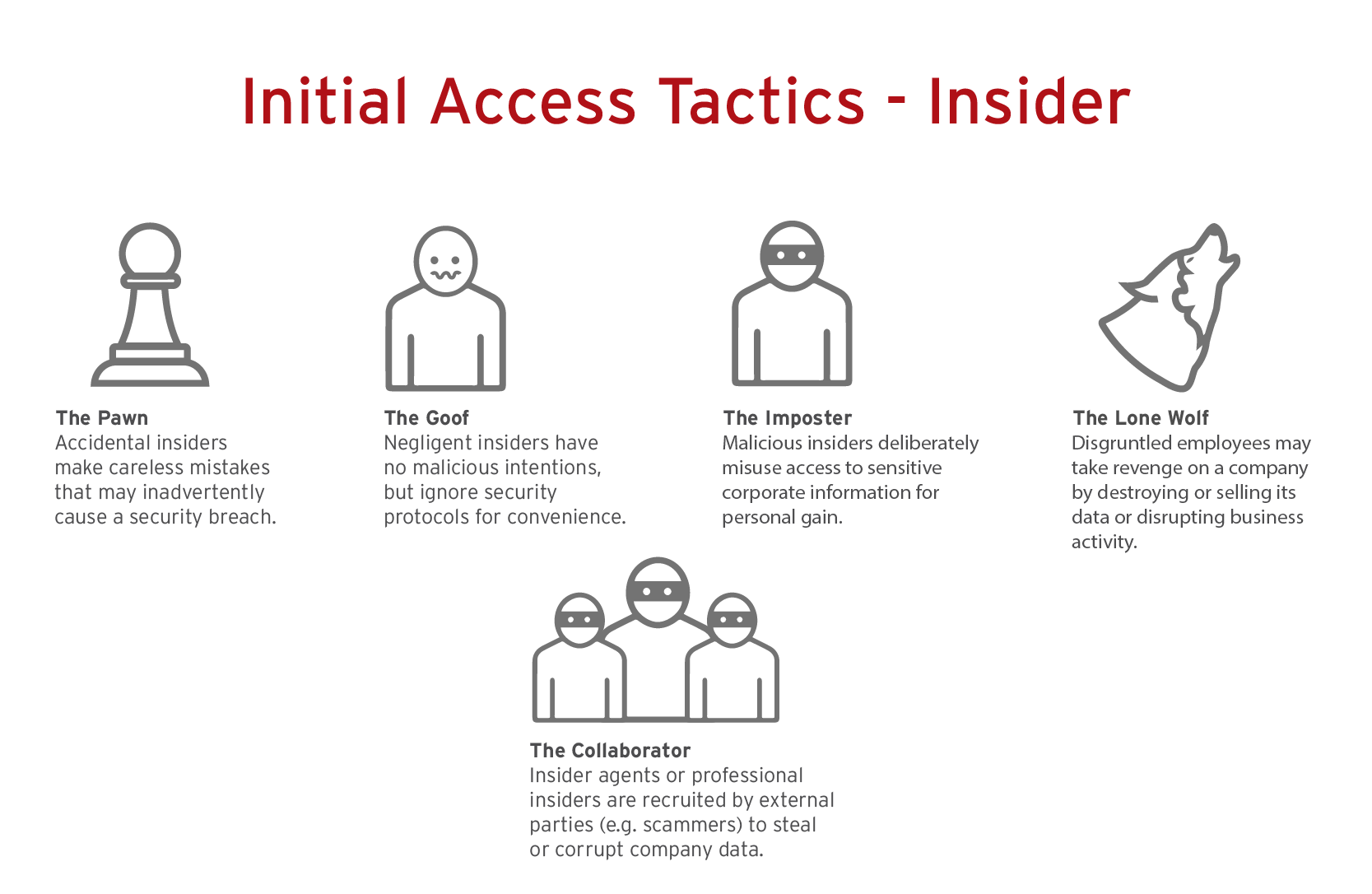
A 2022 Ponemon Institute global report found that the time to contain an insider threat increased from 77 to 85 days, causing organizations to spend the most on containment. Furthermore, incidents that took more than 90 days to contain cost an overage of US $17.19 million on an annualized basis. Whether the insider is simply accidental, negligent, or malicious, the price to pay remains high.
What you can do
Improving cyber hygiene through security awareness training can help businesses avoid the accidental or negligent insiders. To address the other types of insiders, continuous monitoring of ingress and egress traffic is essential. And if this initial attack vector is exploited, having an incident response plan in place will help contain the threat quickly to limit the spread and financial impact.
7. Cloud
The risks
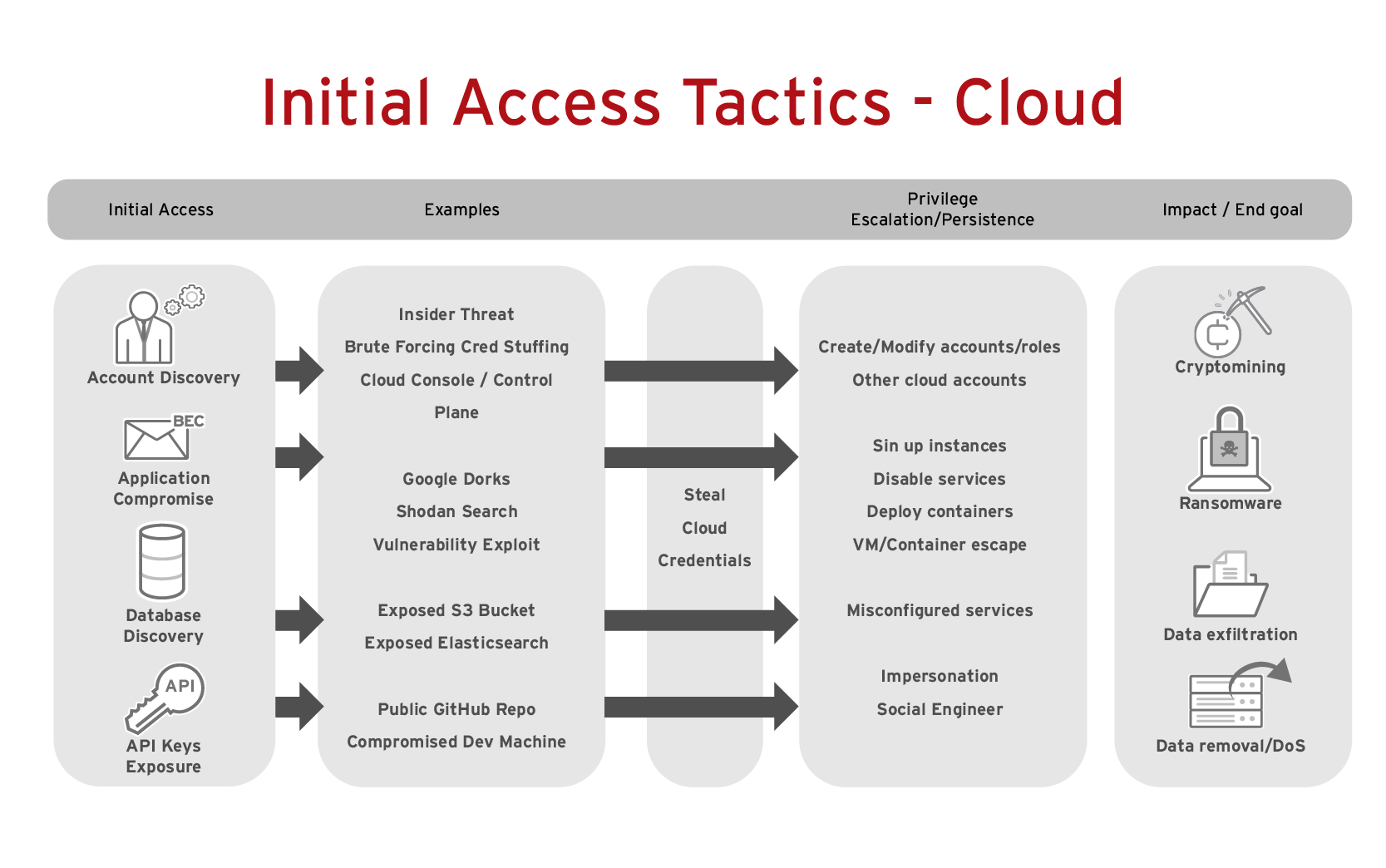
Digital transformation has accelerated cloud adoption, which presents new cybersecurity risk. In the Trend Micro 2024 Midyear Cybersecurity Threat Report, risky cloud app access was ranked number one of the top five risk events during the first half of the year. We also reported in May 2024 how misconfigured Container Advisor (cAdvisor) deployments can lead to threat actors exploiting vulnerabilities via container images, reconnaisance, and other approaches. In addition, per IBM’s 2024 Cost of a Data Breach Report, the most expensive types of breaches were solely focused on public cloud, averaging US $5.17 million—up 13.1% from 2023—while multi-environment breaches were slightly less expensive but more commonplace.
What you can do
Leveraging a cloud-native security platform that supports multi and hybrid-cloud environments is critical. Look for a platform that can automate as many things as possible, from scanning infrastructure as code (IaC), open-source code, containers, and cloud workloads to setting clear security policies and performing compliance checks.
A unified cybersecurity approach to protecting attack vectors
You might get to the end of this and be overwhelmed by the number of new security products you need. Truthfully, deploying and maintaining disparate security tools at each layer is simply unmanageable, especially with the skills gap and turnover. Consider a unified, AI-powered cybersecurity platform to reduce complexity and augment existing resources, all while ensuring security maturity.
Using a unified platform across multiple environments that supports broad third-party integrations ensures comprehensive visibility from a single dashboard. Security capabilities such as automation, continuous monitoring, and XDR are critical to ASRM. Visibility and deep data correlation enable security teams to discover, assess, and mitigate threats across the attack surface risk lifecycle.
Trend has been at the forefront of AI innovation since 2005, empowering security operations center (SOC) analysists and threat hunters alike with technologies that streamline their operations—and help bolster their risk response. Through solutions such as Trend Companion™ and the Trend Vision One™ platform, opportunities abound for organizations to leverage deeper data, harness high-quality analysis, and reveal meaningful, actionable insights.
To learn more about ASRM, check out the following resources:

