On June 2023, the SANS Institute published a new report, “Breaking IT/OT Silos With ICS/OT Visibility” written by Jason Christopher, SANS analyst, with the cooperation of Trend Micro. This survey explores how respondents tackle ICS/OT visibility challenges, the gaps across the IT-OT boundary, the roadblocks to expanding visibility, and the maturity comparisons from both domains. This survey had nearly 350 respondents responsible for IT and OT security across a wide variety of industrial sectors worldwide.
This article discusses the challenges integrating security operations across IT and OT, referring to the report's essence.
Background: Enterprise SOC's responsibility has been expanded to OT, but their capability is developing.
- Approximately 50% claim that their enterprise SOC includes some ICS/OT visibility level.
- Only 53% of their ICS/OT environments provided data for detection.
- Nearly 40% of respondents indicated that only IT staff would respond to the incident.
- Of the survey respondents with no ICS/OT visibility in their SOC, 67% indicated plans to expand their SOC to include these capabilities.
These findings suggest the following situation. Enterprise SOCs have broader responsibilities and are partially observant in OT but unable to detect security events in the OT domain. IT security teams are forced to respond without OT visibility in the OT incident response. But as a positive trend, most organizations that do not yet have a SOC overseeing OT are also keen to expand their enterprise SOC.
What capabilities do you think should be integrated across IT and OT organizational silos?
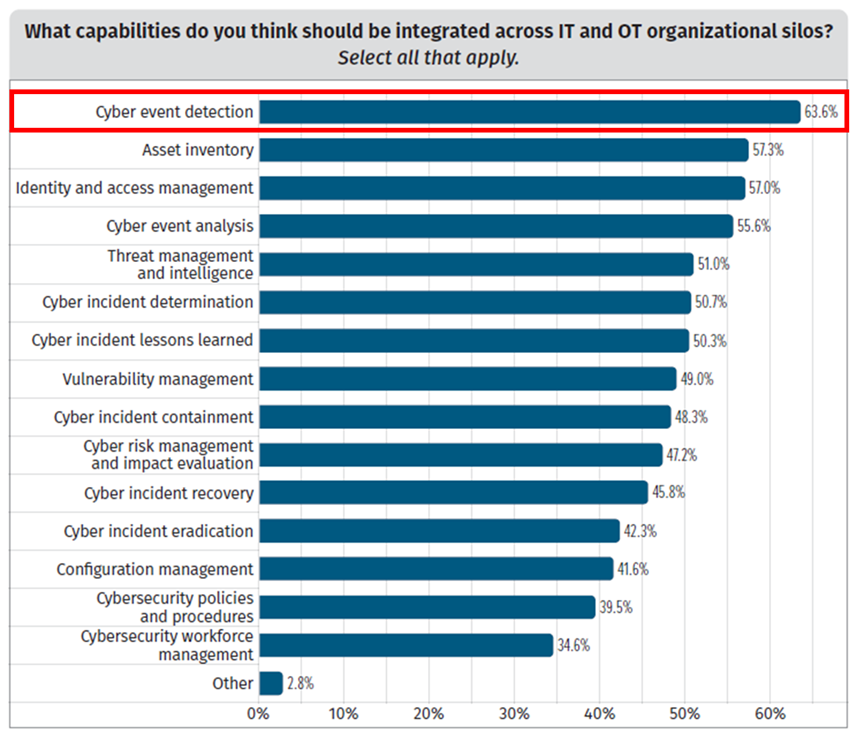
Figure1: Capabilities should be integrated across IT and OT organization silos
Cyber event detection topped the list at 63%. The following categories were asset inventory, identity access control, and event analytics. Beyond the organizational silos of IT and OT, event detection is the most important function to integrate, requiring holistic visibility.
What are the top three challenges for expanding security operations across IT and ICS/OT environments?
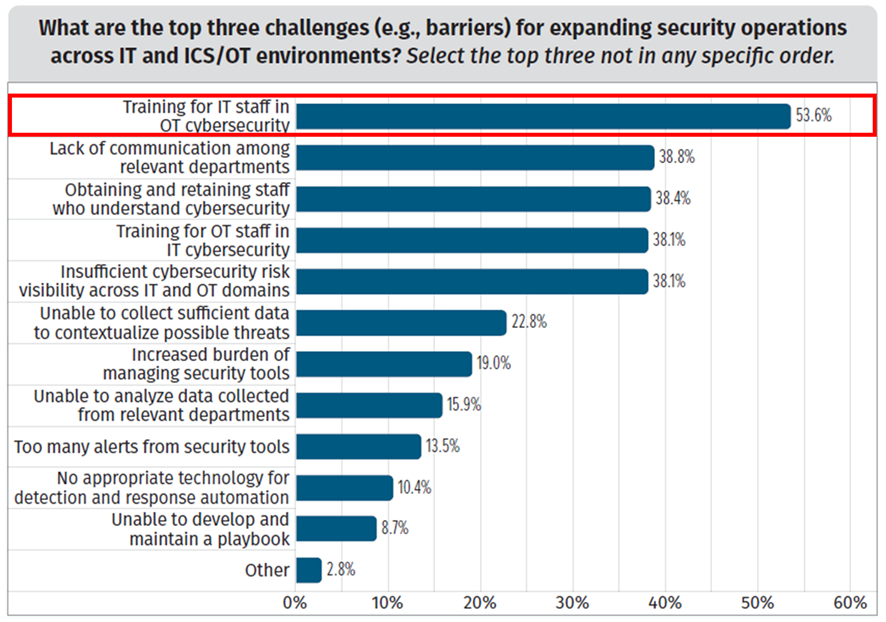
Figure2: The challenges for expanding security operations across IT and ICS/OT
The top was training for IT staff in OT Cybersecurity at 54%. IT and OT are technologies with completely different principles and require understanding the difference. When considering operations that integrate IT and OT, the frequency of attacks against IT is high, and it is also the entry point that leads to OT, so many organizations think training for IT staff tends to be more important than for OT staff.
Cyber event detection is the most important issue for enterprise SOCs to conduct comprehensive security operations, including the OT domain. There are several monitoring stages, but more than simply collecting logs is needed, and massive alerts can overwhelm the SOC team. The ability to detect cyber events across IT and OT and analyze their context helps prioritize events for action.
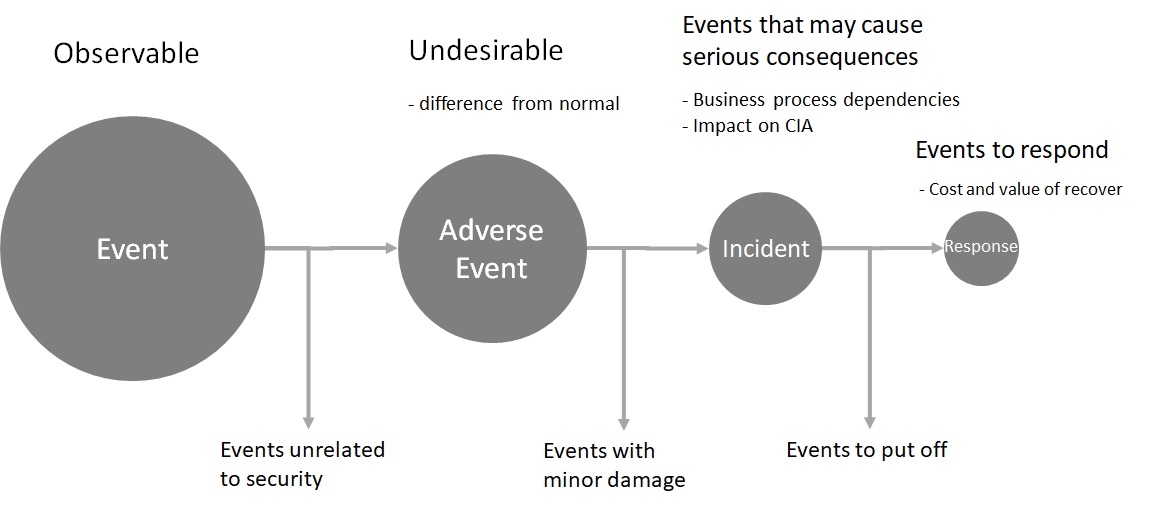
Figure3: Detection and analysis process: refer to Incident Handling Guide (NIST SP800-61r2)
Cyber event detection can be roughly divided into four steps. The first step is the ability to observe own assets and networks. In the OT domain, there are ways to implement endpoint security on the asset and monitor the nearby network. The second step is to filter observable events to know adverse events to your organization regarding protection. It is necessary to define normal conditions and detect anomalies. The third step is to identify those events that can potentially cause significant consequences to your business. This requires evaluating the importance of the business processes that rely on the asset and the CIA of information. The final step is determining whether the event should be dealt with immediately. This is a matter of decision-making. It needs to evaluate the cost-value balance of response and recovery.
Trend Micro's cybersecurity platform across IT and OT streamlines this detection and analysis process.
- Dedicated OT endpoints and network sensors detect anomalous behavior as events.
- Cyber-attacks intrude IT attack surface as an entry point, move internal network and reach OT. Combining information from IT-side sensors with data from OT's based on threat models to visualize attack context.
- Because it becomes easier to identify the cause, route, and scope of impact, management would understand the impact on the business and the resources required for response and recovery.
- These help decision-making in incident response. Concise and quick decisions maximize the efficiency of security resources and minimize damage to your business.
Learn more about our ICS/OT security solutions.
Reference:
Breaking IT/OT Silos with ICS/OT Visibility - 2023 SANS ICS/OT visibility survey

