PUA.Win32.PAExec.AA
Windows


Threat Type: Potentially Unwanted Application
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Potentially Unwanted Application arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It does not have any backdoor routine.
It does not have any information-stealing capability.
TECHNICAL DETAILS
Arrival Details
This Potentially Unwanted Application arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Propagation
This Potentially Unwanted Application does not have any propagation routine.
Backdoor Routine
This Potentially Unwanted Application does not have any backdoor routine.
Rootkit Capabilities
This Potentially Unwanted Application does not have rootkit capabilities.
Information Theft
This Potentially Unwanted Application does not have any information-stealing capability.
Other Details
This Potentially Unwanted Application does the following:
- It is used to launch Windows programs on remote Windows computers without needing to install software on the remote computer first.
- It returns the error code it receives from the application that is launched remotely.
- If it encounters an error, the return code will be one of the following:
- -1 → Internal error
- -2 → Command line error
- -3 → Failed to launch app (locally)
- -4 → Failed to copy PAExec to remote (connection to ADMIN$ might have failed)
- -5 → Connection to server taking too long (timeout)
- -6 → PAExec service could not be installed/started on remote server
- -7 → Could not communicate with remote PAExec service
- -8 → Failed to copy app to remote server
- -9 → Failed to launch app (remotely)
- -10 → App was terminated after timeout expired
- -11 → Forcibly stopped with Ctrl-C / Ctrl-Break
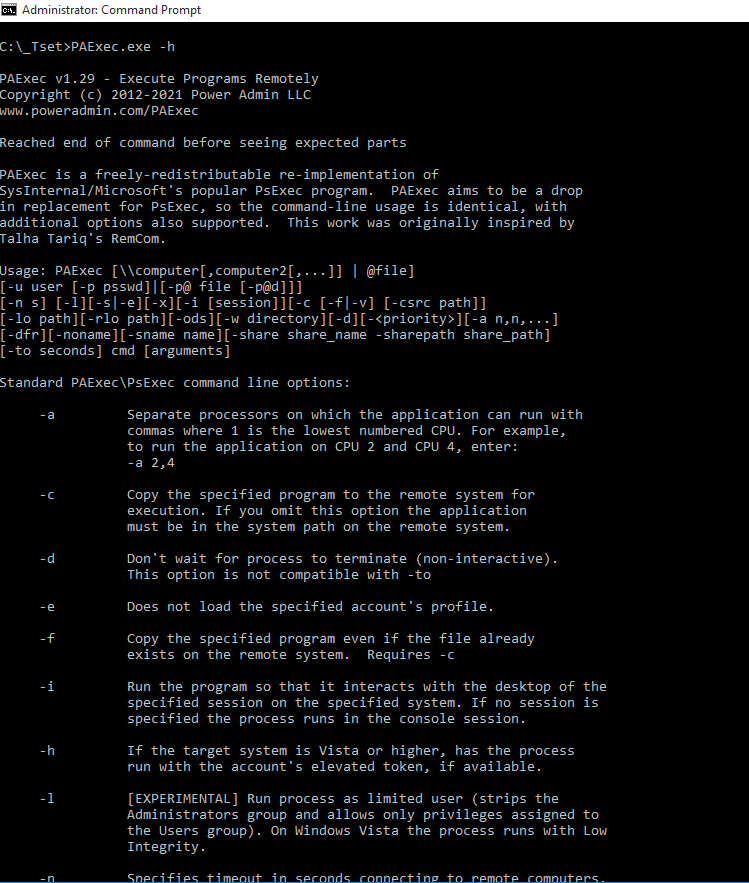
It accepts the following parameters:
- -a → Separates processors on which the application can run with commas where 1 is the lowest numbered CPU.
- Example usage: -a 2,4 (to run on CPU 2 and 4)
- -c → Copies the specified program to the remote system for execution. The application must be in the system path on the remote system if this option is omitted.
- -d → Don't wait for process to terminate (non-interactive).
- This option is not compatible with -to
- -e → Does not load the specified account's profile.
- -f → Copies the specified program even if the file already exists on the remote system.
- Requires -c
- -i → Runs the program so that it interacts with the desktop of the specified session on the specified system. If no session is specified, the process runs in the console session.
- -h → If the target system is Vista or higher, the process runs with the account's elevated token, if available.
- -l → Runs the process as limited user (strips the Administrators group and allows only privileges assigned to the Users group). On Windows Vista, the process runs with Low Integrity.
- This parameter is experimental.
- -n → Specifies timeout in seconds connecting to remote computers.
- -p → Specifies optional password for username. If this parameter is omitted, the user will be prompted to enter a hidden password.
- -s → Runs the process in the System account.
- -u → Specifies optional username for login to remote computer.
- -v → Copies the specified file only if it has a higher version number or is newer than the one on the remote system.
- Requires -c
- -w → Sets the working directory of the process (relative to remote computer).
- -x → Displays the UI on the Winlogon secure desktop
- Local System only.
- -{Priority} → Specifies -low, -belownormal, -abovenormal, -high or -realtime to run the process at a different priority.
- -background can be used to run at low memory and I/O priority on Vista.
- computer → Directs PAExec to run the application on the remote computer or computers specified.
- If this parameter is omitted, PAExec runs the application on the local system.
- If a wildcard (\\*) is specified, PAExec runs the command on all computers in the current domain.
- program → Name of application to execute.
- @file → Executes the command on each of the computers listed in the file.
- arguments → Arguments to pass.
- File paths must be absolute paths on the target system.
- -cnodel → If a file is copied to the server with -c, it is normally deleted, unless -d is specified. -cnodel indicates the file should not be deleted.
- -clist → When using -c (copy), -clist allows to specify a text file that contains a list of files to copy to the target.
- The text file should just list file names, and the files should be in the same folder as the text file.
- -clist and -csrc cannot be used together.
- -csrc → When using -c (copy), -csrc allows to specify an alternate path to copy the program from.
- Example usage: -c -csrc "C:\test path\file.exe"
- -dbg → Outputs to DebugView application.
- -dfr → Disables WOW64 File Redirection for the new process.
- -lo → Logs Output to file.
- Example usage: -lo C:\Temp\PAExec.log
- The file will be UTF-8 with a Byte Order Mark at the start.
- -p@ → Reads the first line of the given file and use that as the password. File should be saved as UTF-8 with or without Byte Order Mark.
- -p@d → Deletes the file specified by -p@ as soon as the password is read.
- -rlo → Remote Log Output: Log from remote service to file (on remote server).
- Example usage: -rlo C:\Temp\PAExec.log
- The file will be UTF-8 with a Byte Order Mark at the start.
- -to → Timeout in seconds before terminating the process.
- Example usage: -to 15
- -noname → Disables adding source server's name to the remote service name and remote PAExec executable file.
- -sname → Remote service name. This option is not compatible with -noname.
- -share → Remote share name. The parameter -sharepath must be supplied when using this functionality.
- -sharepath → Real path of specified remote share. This parameter can only be used with -share.
- -{Any Other String} → Displays the list of parameters that can be used:
NOTES:
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as PUA.Win32.PAExec.AA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.

