RANSOM_HPCERBER.SM6
Ransom:Win32/Cerber!rfn (Microsoft); Win32/Filecoder.Cerber.B (ESET); Ransom.Cerber!g10 (Symantec); Ransom.Cerber (Malwarebytes);
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
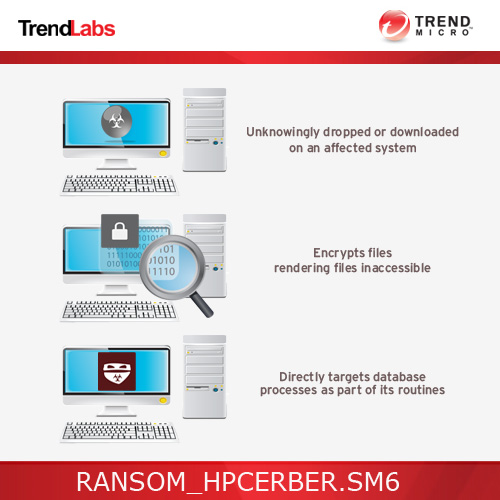
This malware is a variant of malware family CERBER discovered late November 2016, and has been found to be sporting routines that seek out database processes in the affected system. This is believed to enhance its ability to target and infect machines used by businesses.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan may be downloaded by other malware/grayware/spyware from remote sites.
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This Trojan may be downloaded by other malware/grayware/spyware from remote sites.
Installation
This Trojan drops the following files:
- {folders containing encrypted files}\README.hta
- %User Temp%\{random file name}.bmp
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Other System Modifications
This Trojan adds the following registry entries:
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %User Temp%\{random file name}.bmp
Process Termination
This Trojan terminates the following processes if found running in the affected system's memory:
- msftesql.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlservr.exe
- sqlwriter.exe
- oracle.exe
- ocssd.exe
- dbsnmp.exe
- synctime.exe
- mydesktopqos.exe
- agntsvc.exeisqlplussvc.exe
- xfssvccon.exe
- mydesktopservice.exe
- ocautoupds.exe
- agntsvc.exeagntsvc.exe
- agntsvc.exeencsvc.exe
- firefoxconfig.exe
- tbirdconfig.exe
- ocomm.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- dbeng50.exe
- sqbcoreservice.exe
Information Theft
This Trojan gathers the following data:
- MD5_KEY
- PARTNER_ID
- OS
- IS_X64
- IS_ADMIN
- COUNT_FILES
- STOP_REASON
Other Details
This Trojan encrypts files with the following extensions:
- .accdb
- .mdb
- .mdf
- .dbf
- .vpd
- .sdf
- .sqlitedb
- .sqlite3
- .sqlite
- .sql
- .sdb
- .doc
- .docx
- .odt
- .xls
- .xlsx
- .ods
- .ppt
- .pptx
- .odp
- .pst
- .dbx
- .wab
- .tbk
- .pps
- .ppsx
- .jpg
- .tif
- .pub
- .one
- .rtf
- .csv
- .docm
- .xlsm
- .pptm
- .ppsm
- .xlsb
- .dot
- .dotx
- .dotm
- .xlt
- .xltx
- .xltm
- .pot
- .potx
- .potm
- .xps
- .wps
- .xla
- .xlam
- .erbsql
- .sqlite-shm
- .sqlite-wal
- .litesql
- .ndf
- .ost
- .pab
- .oab
- .contact
- .jnt
- .mapimail
- .msg
- .prf
- .rar
- .txt
- .xml
- .zip
- .1cd
- .3ds
- .3g2
- .3gp
- .7z
- .7zip
- .aoi
- .asf
- .asp
- .aspx
- .asx
- .avi
- .bak
- .cer
- .cfg
- .class
- .config
- .css
- .dds
- .dwg
- .dxf
- .flf
- .flv
- .html
- .idx
- .js
- .key
- .kwm
- .laccdb
- .ldf
- .lit
- .m3u
- .mbx
- .md
- .mid
- .mlb
- .mov
- .mp3
- .mp4
- .mpg
- .obj
- .pages
- .php
- .psd
- .pwm
- .rm
- .safe
- .sav
- .save
- .srt
- .swf
- .thm
- .vob
- .wav
- .wma
- .wmv
- .3dm
- .aac
- .ai
- .arw
- .c
- .cdr
- .cls
- .cpi
- .cpp
- .cs
- .db3
- .drw
- .dxb
- .eps
- .fla
- .flac
- .fxg
- .java
- .m
- .m4v
- .max
- .pcd
- .pct
- .pl
- .ppam
- .ps
- .pspimage
- .r3d
- .rw2
- .sldm
- .sldx
- .svg
- .tga
- .xlm
- .xlr
- .xlw
- .act
- .adp
- .al
- .bkp
- .blend
- .cdf
- .cdx
- .cgm
- .cr2
- .crt
- .dac
- .dcr
- .ddd
- .design
- .dtd
- .fdb
- .fff
- .fpx
- .h
- .iif
- .indd
- .jpeg
- .mos
- .nd
- .nsd
- .nsf
- .nsg
- .nsh
- .odc
- .oil
- .pas
- .pat
- .pef
- .pfx
- .ptx
- .qbb
- .qbm
- .sas7bdat
- .say
- .st4
- .st6
- .stc
- .sxc
- .sxw
- .tlg
- .wad
- .xlk
- .aiff
- .bin
- .bmp
- .cmt
- .dat
- .dit
- .edb
- .flvv
- .gif
- .groups
- .hdd
- .hpp
- .m2ts
- .m4p
- .mkv
- .mpeg
- .nvram
- .ogg
- .pdb
- .pif
- .png
- .qed
- .qcow
- .qcow2
- .rvt
- .st7
- .stm
- .vbox
- .vdi
- .vhd
- .vhdx
- .vmdk
- .vmsd
- .vmx
- .vmxf
- .3fr
- .3pr
- .ab4
- .accde
- .accdr
- .accdt
- .ach
- .acr
- .adb
- .ads
- .agdl
- .ait
- .apj
- .asm
- .awg
- .back
- .backup
- .backupdb
- .bank
- .bay
- .bdb
- .bgt
- .bik
- .bpw
- .cdr3
- .cdr4
- .cdr5
- .cdr6
- .cdrw
- .ce1
- .ce2
- .cib
- .craw
- .crw
- .csh
- .csl
- .db_journal
- .dc2
- .dcs
- .ddoc
- .ddrw
- .der
- .des
- .dgc
- .djvu
- .dng
- .drf
- .dxg
- .eml
- .erf
- .exf
- .ffd
- .fh
- .fhd
- .gray
- .grey
- .gry
- .hbk
- .ibank
- .ibd
- .ibz
- .iiq
- .incpas
- .jpe
- .kc2
- .kdbx
- .kdc
- .kpdx
- .lua
- .mdc
- .mef
- .mfw
- .mmw
- .mny
- .moneywell
- .mrw
- .myd
- .ndd
- .nef
- .nk2
- .nop
- .nrw
- .ns2
- .ns3
- .ns4
- .nwb
- .nx2
- .nxl
- .nyf
- .odb
- .odf
- .odg
- .odm
- .orf
- .otg
- .oth
- .otp
- .ots
- .ott
- .p12
- .p7b
- .p7c
- .pdd
- .mts
- .plus_muhd
- .plc
- .psafe3
- .py
- .qba
- .qbr
- .qbw
- .qbx
- .qby
- .raf
- .rat
- .raw
- .rdb
- .rwl
- .rwz
- .s3db
- .sd0
- .sda
- .sr2
- .srf
- .srw
- .st5
- .st8
- .std
- .sti
- .stw
- .stx
- .sxd
- .sxg
- .sxi
- .sxm
- .tex
- .wallet
- .wb2
- .wpd
- .x11
- .x3f
- .xis
- .ycbcra
- .yuv
- .mab
- .json
- .msf
- .jar
- .cdb
- .srb
- .abd
- .qtb
- .cfn
- .info
- .info_
- .flb
- .def
- .atb
- .tbn
- .tbb
- .tlx
- .pml
- .pmo
- .pnx
- .pnc
- .pmi
- .pmm
- .lck
- .pm!
- .pmr
- .usr
- .pnd
- .pmj
- .pm
- .lock
- .srs
- .pbf
- .omg
- .wmf
- .sh
- .war
- .ascx
- .k2p
- .apk
- .asset
- .bsa
- .d3dbsp
- .das
- .forge
- .iwi
- .lbf
- .litemod
- .ltx
- .m4a
- .re4
- .slm
- .tiff
- .upk
- .xxx
- .money
- .cash
- .private
- .cry
- .vsd
- .tax
- .gbr
- .dgn
- .stl
- .gho
- .ma
- .acc
- .db
It renames encrypted files using the following names:
- {10 Random Characters}.{4 Random}
It does the following:
- It avoids encrypting the following files:
- bootsect.bak
- iconcache.db
- ntuser.dat
- thumbs.db
- It skips to encrypt the following paths:
- :\$recycle.bin\
- :\$windows.~bt\
- :\boot\
- :\documents and settings\all users\
- :\documents and settings\default user\
- :\documents and settings\localservice\
- :\documents and settings\networkservice\
- :\program files\
- :\program files (x86)\
- :\programdata\
- :\recovery\
- :\recycler\
- :\users\all users\
- :\windows\
- :\windows.old\
- \appdata\local\
- \appdata\locallow\
- \appdata\roaming\adobe\flash player\
- \appData\roaming\apple computer\safari\
- \appdata\roaming\ati\
- \appdata\roaming\intel\
- \appdata\roaming\intel corporation\
- \appdata\roaming\google\
- \appdata\roaming\macromedia\flash player\
- \appdata\roaming\mozilla\
- \appdata\roaming\nvidia\
- \appdata\roaming\opera\
- \appdata\roaming\opera software\
- \appdata\roaming\microsoft\internet explorer\
- \appdata\roaming\microsoft\windows\
- \application data\microsoft\
- \local settings\
- \public\music\sample music\
- \public\pictures\sample pictures\
- \public\videos\sample videos\
- \tor browser\
- It deletes all shadow copies by executing the following command:
- WMIC.exe shadowcopy delete
- It sends and receives data via port 6892 using following IP range:
- {BLOCKED}.{BLOCKED}.16.0/22:6892
- It speaks the following message:
- Attention! Attention! Attention!Your documents, photos, databases and other important files have been encrypted!
It deletes the initially executed copy of itself
NOTES:
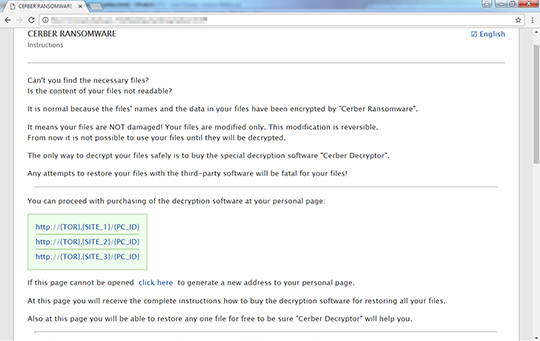
This ransomware changes the wallpaper with the following image:
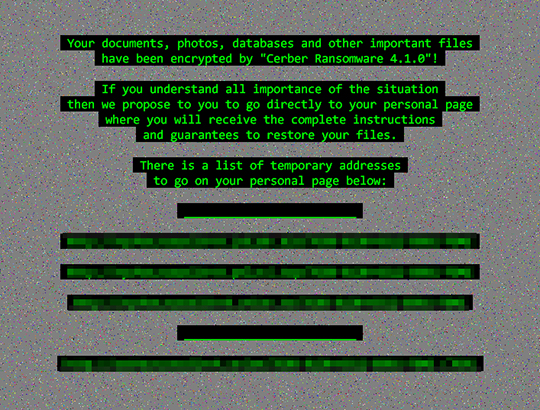
It also displays the following ransom note:
It searches for the following strings to skip the file path exception list
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Search and delete this file
- {folders containing encrypted files}\README.hta
- %User Temp%\{random file name}.bmp
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Control Panel\Desktop
- Wallpaper = "%User Temp%\{random file name}.bmp"
- Wallpaper = "%User Temp%\{random file name}.bmp"
Step 4
Scan your computer with your Trend Micro product to delete files detected as RANSOM_HPCERBER.SM6. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 5
Restore encrypted files from backup.
Did this description help? Tell us how we did.


