BKDR_KULUOZ.PFG
a variant of Win32/Kryptik.ABNX trojan, a variant of Win32/Kryptik.ABNX trojan (Eset), W32/Kuluoz.APB!tr.dldr (Fortinet)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This malware disguises as delivery receipts for well-known postal and delivery services firms and airlines.
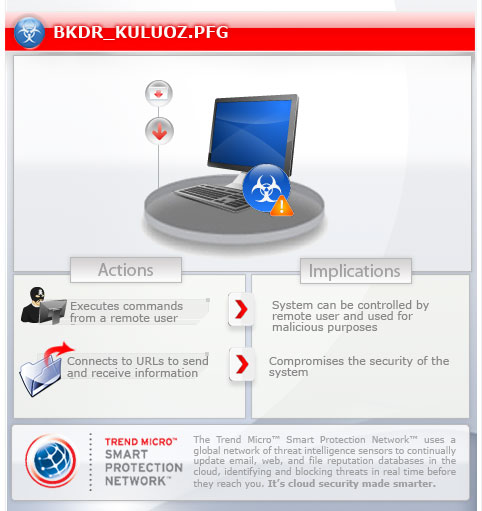
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
For the related story, you may read the blog post BKDR_KULUOZ – At a Spam Near You.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system. It connects to a website to send and receive information.
TECHNICAL DETAILS
25,600 bytes
EXE
Yes
31 Jan 2013
Connects to URLs/IPs, Compromises system security
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
This malware arrives via the following means:
- spammed email message that disguises as receipt from the following postal/delivery services and airline ticketing system:
Delta Airlines
American Airlines
Deutsche Post
FedEx
UPS
Installation
This backdoor drops the following copies of itself into the affected system:
- %Application Data%\{random}.exe
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista and 7.)
It adds the following processes:
- svchost.exe
It injects codes into the following process(es):
- created svchost.exe
Autostart Technique
This backdoor adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
{random} = "%Application Data%\{random}.exe"
Other System Modifications
This backdoor adds the following registry keys:
HKEY_CURRENT_USER\SOFTWARE\{random}
It adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\SOFTWARE\{random}
{random} = "{hex values}"
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- idl|Sleep / Idle
- run|Download and Execute Arbitrary file
- rem|Uninstall itself
- rdl|Update copy of injected code in svchost and add encrypted code to registry
- upd|Update copy of main malware
- red|Check latest malware version
It connects to the following websites to send and receive information:
- {BLOCKED}.{BLOCKED}.132.24:8080/{generated value}
- {BLOCKED}.{BLOCKED}.224.202:8080/{generated value}
- {BLOCKED}.{BLOCKED}.63.194:8080/{generated value}
- {BLOCKED}.{BLOCKED}.178.174:8080/{generated value}
- {BLOCKED}.{BLOCKED}.10.68:8080/{generated value}
- {BLOCKED}.{BLOCKED}.81.166:8080/{generated value}
- {BLOCKED}.{BLOCKED}.159.166:8080/{generated value}
- {BLOCKED}.{BLOCKED}.22.146:8080/{generated value}
- {BLOCKED}.{BLOCKED}.50.161:8080/{generated value}
- {BLOCKED}.{BLOCKED}.20.202:8080/{generated value}
SOLUTION
9.300
9.698.03
01 Feb 2013
9.701.00
01 Feb 2013
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product and note files detected as BKDR_KULUOZ.PFG
Step 3
Restart in Safe Mode
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\SOFTWARE
- {random}
- {random}
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- {random} = "%Application Data%\{random}.exe"
- {random} = "%Application Data%\{random}.exe"
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as BKDR_KULUOZ.PFG. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

