Backdoor.PHP.WEBSHELL.AC
Windows, Linux


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
44,784 bytes
PHP
No
21 Jun 2024
Collects system information, Connects to URLs/IPs, Displays windows, Steals information
Arrival Details
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Propagation
This Backdoor does not have any propagation routine.
Backdoor Routine
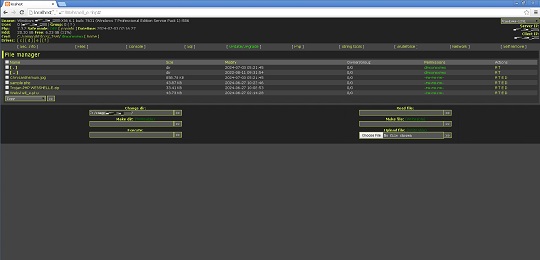
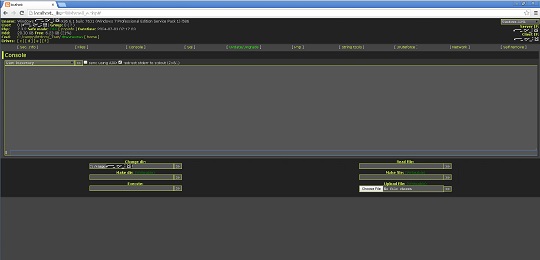
This Backdoor executes the following commands from a remote malicious user:
- Execute cmd commands
- Create directories
- Create file
- Execute files
- View file
- Edit file
- Rename file
- Upload file
- Download file
- Delete file
- Change file permission
- Change file attributes
- Change last modify time of files
- Search files
- Search hash
- Delete itself
Rootkit Capabilities
This Backdoor does not have rootkit capabilities.
Information Theft
This Backdoor gathers the following data:
- Computer name
- Operating system
- User name
- Group name
- PHP version
- Date and Time
- Computer mode (Safe Mode on or off)
- Client IP address
- Server IP address
- Current working directory
- Hard drive total space
- Hard drive free space
- Disk drives present
- Server software
- Loaded Apache modules
- Disabled PHP Functions
- cURL support
- OS version
- User accounts
- Directories of the following (For Linux):
- Open_basedir
- Safe_mode_exec_dir
- Safe_mode_include_dir
- Complete file directory for all disk drives including:
- File Name
- File size
- Last modified date
- Owners/Group
- File Permissions
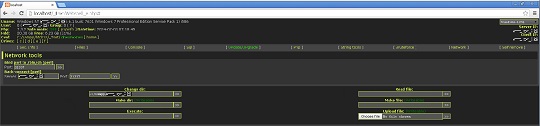
- Active connections in infected machine
- Running Windows services in infected machine
- User accounts in infected machine
- Connected computers in the infected machine
- ARP Table of the infected machine
- IP Configuration of the infected machine
Other Details
This Backdoor does the following:
- It can access SQL and PostgreSQL database (requires Host, Username, Password, and Database name )
- It connects to the following URL to acquire an update:
- http://{BLOCKED}ack.live/96382367f90798e98d30f82012963197.htm
However, as of this writing, the said site is inaccessible.
- Execute PHP code using 'eval' function
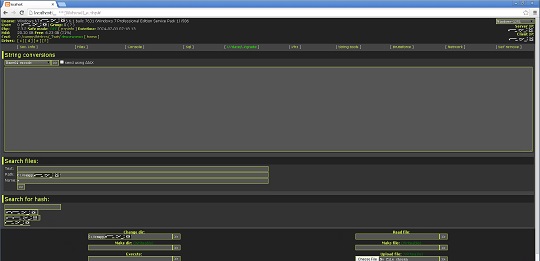
- Contains a collection of string tools:
- Base64 encoding/decoding
- URL encoding/decoding
- Full URL encoding
- Generate MD5 hash
- Generate SHA1 hash
- Generate CRYPT hash
- Generate CRC32 hash
- Generate HTML formatted special characters
- Convert ASCII to hexadecimal
- Convert hexadecimal to ASCII
- Convert hexadecimal to decimal
- Convert hexadecimal to binary
- Convert decimal to hexadecimal
- Convert decimal to binary
- Convert binary to hexadecimal
- Convert binary to decimal
- Convert lower case string to upper case string and vice versa
- Calculate string length
- Search for hash using the following URLs:
- https://hashcracking.ru/index.php
- http://md5.rednoize.com/
- http://{BLOCKED}or.me/index.php
However, as of this writing, the said sites are inacessible.
- Conduct brute force attack on FTP, MySQL, and PostgreSQL servers
- Conduct back connection for PERL and PHP threads (requires IP address and port number)
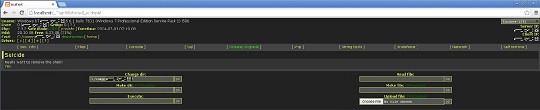
- It displays the following GUI:


It does not exploit any vulnerability.
SOLUTION
9.800
19.444.03
03 Jul 2024
19.445.00
04 Jul 2024
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as Backdoor.PHP.WEBSHELL.AC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


