BKDR_MSPOSER.KAX
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This backdoor has received attention from independent media sources and/or other security firms. Specifically, it is the dropped file of TROJ_MSPOSER.ASM, a Trojan that takes advantage of the Epsilon data-breach incident.
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
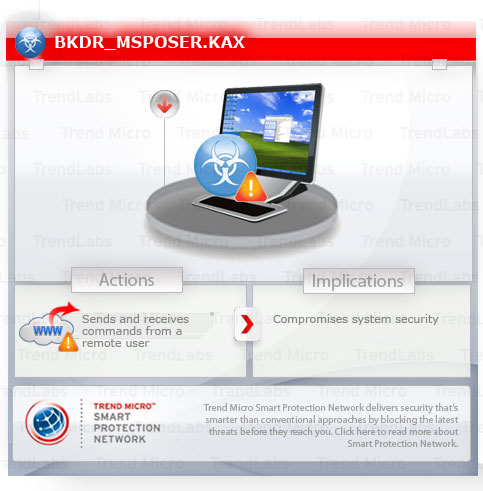
It connects to specific sites to send and receive commands from a remote user, thus compromises system security.
This backdoor may be dropped by other malware.
TECHNICAL DETAILS
194,048 bytes
EXE
Yes
19 Apr 2011
Arrival Details
This backdoor may be dropped by the following malware:
- TROJ_MSPOSER.ASM
Autostart Technique
This backdoor adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
IE = "{malware path and file name}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
IE = "{malware path and file name}"
Other System Modifications
This backdoor adds the following registry keys:
HKEY_CURRENT_USER\Software\Microsoft\
Multimedia\DrawDib
It adds the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Multimedia\DrawDib
vga.drv {resolution} = "31,31,31,31"
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
Remove = "{time}"
NOTES:
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Capture screenshots
- Capture Web camera
- Create/Remove folders
- Download/Upload files
- Enumerate network adapters
- Execute arbitrary commands
- Execute DOS command
- Execute network statistics (netstat)
- Execute WMI commands
- Get access control list information
- Get certificates
- Get IP configuration settings
- Get system information (computer name, manufacturer, model, OS, system type, memory)
- Get user name and password
- List drives
- List SQL servers
- List/Start/Kill processes
- Log keystrokes
- Manipulate files
- Manipulate system sound volume
- Open Web pages
- Read/Write/Delete registry values
- Record sounds using microphone
- Remove itself
- Send emails
- Start/Stop services
- Update itself
It connects to the following URL to send and receive commands from a remote user:
- https://{BLOCKED}1.230.85/rh/
SOLUTION
8.900
8.106.02
20 Apr 2011
8.107.00
20 Apr 2011
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Identify and terminate files detected as BKDR_MSPOSER.KAX
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Multimedia
- DrawDib
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- IE = {malware path and file name}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- IE = {malware path and file name}
- In HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer
- Remove = {time}
Step 6
Scan your computer with your Trend Micro product to delete files detected as BKDR_MSPOSER.KAX. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

