PHP_WEBSHELL.AGNV
HEUR:Backdoor.PHP.PhpShell.eg(Kaspersky); Backdoor.PHP.Webshell.EB(BitDefender)
Windows


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This backdoor may be hosted on a website and run when a user accesses the said website.
It executes commands from a remote malicious user, effectively compromising the affected system.
It retrieves specific information from the affected system.
TECHNICAL DETAILS
Arrival Details
This backdoor may be hosted on a website and run when a user accesses the said website.
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Execute cmd commands
- Terminate process
- File/folder related commands:
- View file
- Edit file
- Rename file
- Download file
- Upload file
- Copy File
- Paste file
- Search file
- Delete file
- Create file
- Change file mode
- Change file owner
- Change file accessed and modified time
- Extract file (.tar, .tar.gz, .zip)
- Compress file (.tar, tar.gz, .zip)
Information Theft
This backdoor retrieves the following information from the affected system:
- IP address
- Server IP address
- Time in server
- Computer name
- Operating System
- Machine type
- Drives available
- Drive free space
- Drive total space
- Versions of the following:
- PHP
- Python
- Perl
- Ruby
- Node
- Nodejs
- GNU Compiler Collection
- Java
- Javac
- PHP General Info
- PHP Configuration
- PHP Modules
- PHP Environment
- PHP Variables
- If the following servers are turned on:
- MYSQL
- MSSQL
- PostGreSQL
- Oracle
- SQLite
- SQLite3
- Open Database Connectivity
- PHP Data Objects
- It gets the following information if the Operating System is not Windows:
- System File Configuration
- CPU
- Memory
- Partition
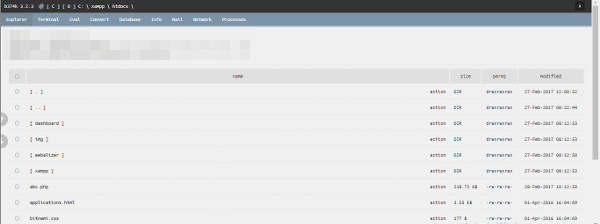
- Complete file directory for all available disk drives(from A: to Z:) including:
- File name
- Size
- File permissions
- Date modified
- List of active processes including:
- Image name
- Process ID
- Session name
- Session number
- Memory usage
- Status
- User name
- CPU time
- Window title
Other Details
This backdoor does the following:
- Send mail
- Listen to a specified IP address and port
- Connect to a specified IP address and port
- Create packet
- Execute code as either of the following (if installed):
- PHP
- Python
- Perl
- Ruby
- Node
- NodeJS
- GNU Compiler Collection
- Java
- Executable
- Access the following databases (if installed):
- MYSQL
- MSSQL
- PostGreSQL
- Oracle
- SQLite
- SQLite3
- Open Database Connectivity
- PHP Data Objects
- Convert input to the following:
- md5
- sha1
- base64 encode
- base64 decode string to hex
- ascii char
- reversed
- lowercase
- uppercase
- urlencode
- urldecode
- rawurlencode
- rawurldecode
- htmlentities
- md2
- md4
- sha224
- sha256
- sha384
- sha512
- ripemd128
- ripemd160
- ripemd256
- ripemd320
- whirlpool
- tiger128,3
- tiger160,3
- tiger192,3
- tiger128,4
- tiger160,4
- tiger192,4
- snefru
- snefru256
- gost
- gost-crypto
- adler32
- crc32
- crc32b
- fnv132
- fnv1a32
- fnv164
- fnv1a64
- joaat
- haval128,3
- haval160,3
- haval192,3
- haval224,3
- haval256,3
- haval128,4
- haval160,4
- haval192,4
- haval224,4
- haval256,4
- haval128,5
- haval160,5
- haval192,5
- haval224,5
- haval256,5
NOTES:
This malware does nothing if user agent contains the any of the following strings:
- bot
- spider
- crawler
- slurp
- teoma
- archive
- track
- snoopy
- java
- lwp
- wget
- curl
- client
- python
- libwww
Upon execution, this backdoor shows the following:
Once the correct password is entered, it directs the user to the GUI below:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as PHP_WEBSHELL.AGNV. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


