HKTL_DSTEALER.GA
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Downloaded from the Internet
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
TECHNICAL DETAILS
1,332,224 bytes
EXE
Yes
16 May 2014
Arrival Details
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
NOTES:
This hacking tool is able to generate a file used for information stealing.
It requires the following components to work properly:
- Mono.Cecil.dll
- {malware path}\STUB\FBIN.exe
- {malware path}\ STUB\Stealer.exe
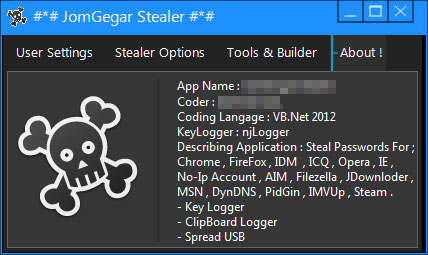
The window of this hacking tool has the following tabs:
- User Settings
- Stealer Options
- Tools and Builder
- About
In the User Settings tab, the user can configure the email address where the notifications and the gathered information of the generated file is to be delivered:
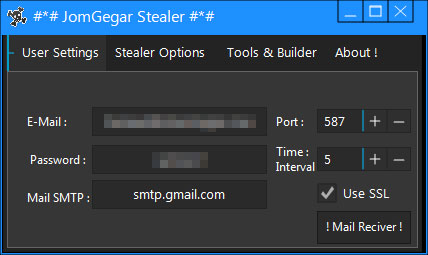
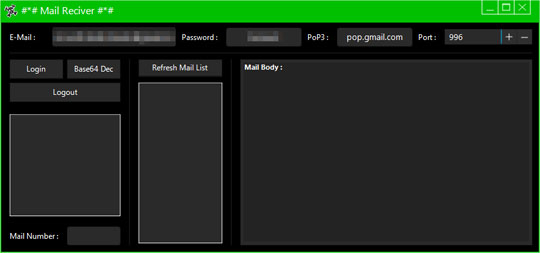
The messages received can be monitored by clicking the ! Mail Reciver ! button:
The tab Stealer Options allows the user to choose what the generated file is named and where it is dropped:
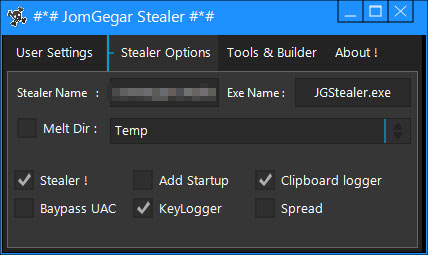
The generated file may be dropped in the following folders:
- %User Temp%
- %AppData%
- %User Profile%
The user also has the option to choose the capabilities of the generated file:
- Melt Directory
- Stealer
- BypassUAC
- Add Startup
- KeyLogger
- Clipboard logger
- Spread
The tab Tools and Builder allows the user to assign additional options for the generated file:
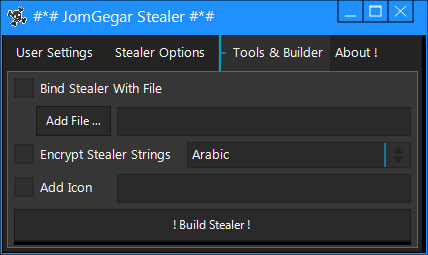
The additional options are:
- Bind Stealer with File
- Encrypt Stealer String (using Arabic,English,Chinese)
- Add Icon
Clicking the ! Build Stealer ! button generates the configured information-stealing file. It is also dropped in the folder the user has configured in the Stealer Options tab.
The About contains information about this hacking tool and its generated file:
SOLUTION
9.800
1.511.00
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Identify and terminate files detected as HKTL_DSTEALER.GA
- For Windows 98 and ME users, Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Search and delete these folders
- {malware path}\STUB\
Step 5
Scan your computer with your Trend Micro product to delete files detected as HKTL_DSTEALER.GA If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

