TSPY_ISPY.QAM
Windows


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It gathers certain information on the affected computer. It steals email account information. It steals CD keys, serial numbers, and/or the application product IDs of certain software. tolen information may be used for profit by cybercriminals who may gain access to the information. It steals sensitive information such as user names and passwords related to certain games. It logs a user's keystrokes to steal information.
It terminates itself if it detects it is being run in a virtual environment. It gathers information and reports it to its servers.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This spyware drops the following file(s)/component(s):
- %User Temp%\aut{random 4 characters}.tmp <- temporary encrypted config file, deleted afterwards
- %User Temp%\{random} <- config file, deleted afterwards
- %User Profile%\{random folder name}\dMJPa.au3 <- autoit script containing the malicious code
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It drops and executes the following files:
- %User Profile%\{random folder name}\AhbI.exe <- AutoIt3.exe to execute the malicious .au3 file
- %User Temp%\IXP000.TMP\HgLWcIgMEX.exe <- also detected as TSPY_ISPY.QAM, deleted after execution
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.. %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It adds the following processes:
- RegSvcs.exe
- vbc.exe
It creates the following folders:
- %User Temp%\IXP000.TMP <- deleted after installation routine
- %User Profile%\{random folder name}
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It creates the following folders with attributes set to System and Hidden to prevent users from discovering and removing its components:
- %User Profile%\{random folder name}
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It terminates itself if it finds the following processes in the affected system's memory:
- VboxTray.exe
- vmtoolsd.exe
- SandboxieRpcSs.exe
Autostart Technique
This spyware drops the following file(s) in the Windows Startup folder to enable its automatic execution at every system startup:
- %User Startup%\GCPdiWVeAhEZ.lnk <- points to the loader of the malicious .au3 file
(Note: %User Startup% is the current user's Startup folder, which is usually C:\Documents and Settings\{user}\Start Menu\Programs\Startup on Windows 2000 and XP, and C:\Documents and Settings\{User name}\Start Menu\Programs\Startup on Windows Vista, 7, and 8.)
Dropping Routine
This spyware drops the following files:
- %User Temp%\tmp{random 4 characters}.tmp <- contains CD and/or Product Keys gathered, deleted afterwards
- %User Temp%\{GUID} <- contains the path for RegSvcs.exe
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Information Theft
This spyware gathers the following information on the affected computer:
- Beyluxe Messenger Credentials
- Webcam Snapshots and Screen captures
It uploads the images to the following image hosting website: - http://{BLOCKED}s.im/api?upload&format=xml
It steals email account information.
It steals CD keys, serial numbers, and/or the application product IDs of certain software.
It steals sensitive information such as user names and passwords related to the following games:
- MineCraft
It gathers the following account information from any of the mentioned File Transfer Protocol (FTP) clients or file manager software:
- CoreFTP
- FileZilla
It attempts to get stored information such as user names, passwords, and hostnames from the following browsers:
- Google Chrome
- Mozilla Firefox
- Apple Safari
- Opera Browser
It logs a user's keystrokes to steal information.
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://ugonna.{BLOCKED}g.com/Panel/api
Note: contains the following data in the body:- Secret={Unique ID}&HWID={Hardware ID}&Name={Computer Name}&Country={Language}&OS={OS version}&Verion={Malware Version}&Type={Type of Information sent}&Data={Data to be sent}
- http://{BLOCKED}ay.iinfo/Products/iPsyKelogger/Server/
Note: contains the following data in the body:- gate=stub&token={value}&name={base64 encoded data}
Other Details
This spyware connects to the following URL(s) to get the affected system's IP address:
- http://www.checkip.dyndns.org/
It terminates itself if it detects it is being run in a virtual environment.
It does the following:
- Block websites (by modifying the hosts file based on the configuration)
- Download other possibly malicious files
- Drop and Execute bundled files
- It adds the following Image File Execution Options to prevent certain AV related files from executing:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\{AV related file}
Debugger = "rundll32.exe"
Where {AV related file} can be any of the following:- rstrui.exe
- AvastSvc.exe
- avconfig.exe
- AvastUI.exe
- avscan.exe
- instup.exe
- mbam.exe
- mbamgui.exe
- mbampt.exe
- mbamscheduler.exe
- mbamservice.exe
- hijackthis.exe
- spybotsd.exe
- ccuac.exe
- avcenter.exe
- avguard.exe
- avgnt.exe
- avgui.exe
- avgcsrvx.exe
- avgidsagent.exe
- avgrsx.exe
- avgwdsvc.exe
- egui.exe
- zlclient.exe
- bdagent.exe
- keyscrambler.exe
- avp.exe
- wireshark.exe
- ComboFix.exe
- MSASCui.exe
- MpCmdRun.exe
- msseces.exe
- MsMpEng.exe
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\{AV related file}
It gathers the following information and reports it to its servers:
- User Name
- OS Version
- Language
- .NET framework Installed
- System Privilege
- Default Browser
- List of installed AV products
- List of installed Firewall
- Internal IP
- External IP
- Current Data and Time
NOTES:
It does not have rootkit capabilities.
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Search and delete this folder
Step 5
Search and delete this file
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options
- {AV related file}
Where {AV related file} can be any of the following:- rstrui.exe
- AvastSvc.exe
- avconfig.exe
- AvastUI.exe
- avscan.exe
- instup.exe
- mbam.exe
- mbamgui.exe
- mbampt.exe
- mbamscheduler.exe
- mbamservice.exe
- hijackthis.exe
- spybotsd.exe
- ccuac.exe
- avcenter.exe
- avguard.exe
- avgnt.exe
- avgui.exe
- avgcsrvx.exe
- avgidsagent.exe
- avgrsx.exe
- avgwdsvc.exe
- egui.exe
- zlclient.exe
- bdagent.exe
- keyscrambler.exe
- avp.exe
- wireshark.exe
- ComboFix.exe
- MSASCui.exe
- MpCmdRun.exe
- msseces.exe
- MsMpEng.exe
- {AV related file}
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TSPY_ISPY.QAM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 8
Restore a file/s that has/have been corrupted/modified by this malware/grayware
To restore system files:
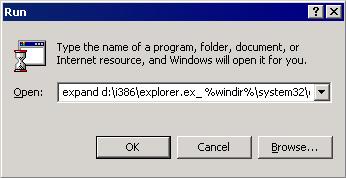
• For Windows 2000:
- Insert your Windows 2000 Installation CD in your CD-ROM drive.
- Click Start>Run.
- In the Open text box, type the following then click OK:
expand D:\i386\{file to restore}.ex_ %windir%\system32\{file to restore}.exe
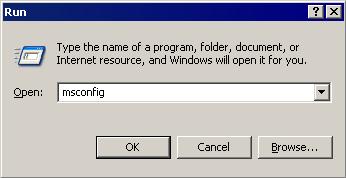
• For Windows XP and Windows Server 2003:
- Click Start>Run.
- In the Open text box, type the following then click OK:
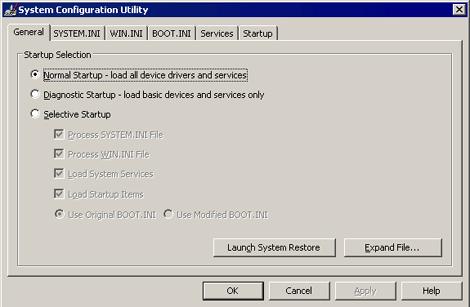
MSCONFIG - Make sure that the option Normal startup - load all device drivers and services option is selected.
- Click the Expand button.
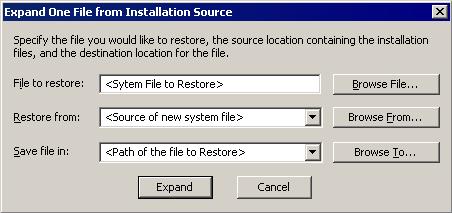
- In the dialog box that appears, type the following:
- File to restore contains the path and file name of the file you wish to restore.
- Restore from contains the path to the Windows CAB files. This path may vary from machine to machine. It may be in a local drive, in a network drive, or in a CD-ROM. In the local drive, it is usually in C:\WINDOWS\OPTIONS\INSTALL.
- Save file in contains the path of the file you wish to restore (Do not include the file name).
- Click the Expand button.
Step 9
Scan your computer with your Trend Micro product to delete files detected as TSPY_ISPY.QAM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



