Vulnerabilities serve as entry points for threats, and even relatively new ones have swarms of exploit campaigns that target them. In this research, we look into how malware campaigns target server vulnerabilities. In particular, we look into the Atlassian Confluence Server Webwork Object-Graph Navigation Language (OGNL) injection vulnerability, CVE-2021-26084, and three Oracle WebLogic Server vulnerabilities, CVE-2020-14882, CVE-2020-14750, and CVE-2020-14883. We also include recommendations on how security teams can safeguard their workloads.
To observe the following campaigns, we used detection data and set up honeypots, which we managed with Trend Micro Cloud One™ – Workload Security and Trend Micro Vision One™. With the help of these solutions, we were able to investigate attacks launched by adversaries as well as attempt some attack scenarios ourselves.
This entry shows Trend Micro Cloud One™ and Trend Micro Vision One at work in detecting and tracking these vulnerability exploits. The in-depth analysis of the campaign techniques observed in our research can be found in our technical brief.
Muhstik Campaign
Almost immediately after Atlassian released the patch for CVE-2021-26084, we saw many different types of attack campaigns seeking to exploit this vulnerability, most of which are cryptomining campaigns.
One notable attack traffic that we have seen so far on CVE-2021-26084 was by the Muhstik botnet campaign, which mostly has the purpose of cryptomining as well. Muhstik targeted vulnerable internet of things (IoT) devices, such as routers, to grow its malicious network and perform other tasks, such as mining for cryptocurrency or launching distributed denial-of-service (DDoS) attacks.
The operators behind Muhstik target vulnerabilities in public-facing web applications to increase the botnet's reach. Attackers behind the botnet fund their operation by mining cryptocurrency with the help of such tools as XMRig and cgmining, and also by providing DDoS-for-hire services.

A more detailed explanation of this chain and the specific techniques observed in this campaign can be found in our tech brief.
We used Cloud One and Trend Micro Vision One to help analyse this campaign. We discuss our detections in the following section.
Trend Micro Cloud One
Intrusion Prevention System (IPS) detection
For the Muhstik bot campaign, rule 1011117 - Atlassian Confluence Server RCE vulnerability CVE-2021-26084 was triggered in the IPS. This is due to the detected incoming malicious behaviour that seeks to exploit the said vulnerability.





Trend Micro Vision One
Trend Micro Vision One Workbench
Through the Trend Micro Vision One Workbench, we were able to track and detect malicious behaviour as seen in vulnerability exploitation, suspicious outbound connection, and the presence of.kswapd (detected by Trend Micro as Coinminer.Linux.MALXMR.SMDSL64) and pty86 (detected by Trend Micro as Backdoor.Linux.TSUNAMI.AMX).
Trend Micro Vision One Observed Attack Techniques (OAT) Triggers
Trend Micro Vision One OAT also showed the detected vulnerability exploitation, with the risk level marked as High.

Kinsing Campaign
Known for its comprehensive attack patterns and defence evasion schemes, the Kinsing malware is often wielded against misconfigured cloud-native environments. A misconfigured host or cluster could be exploited to run any container the attacker wants to deploy. This would cause outages on the target’s service. It can also be used to perform lateral movement to other services, compromising sensitive data.
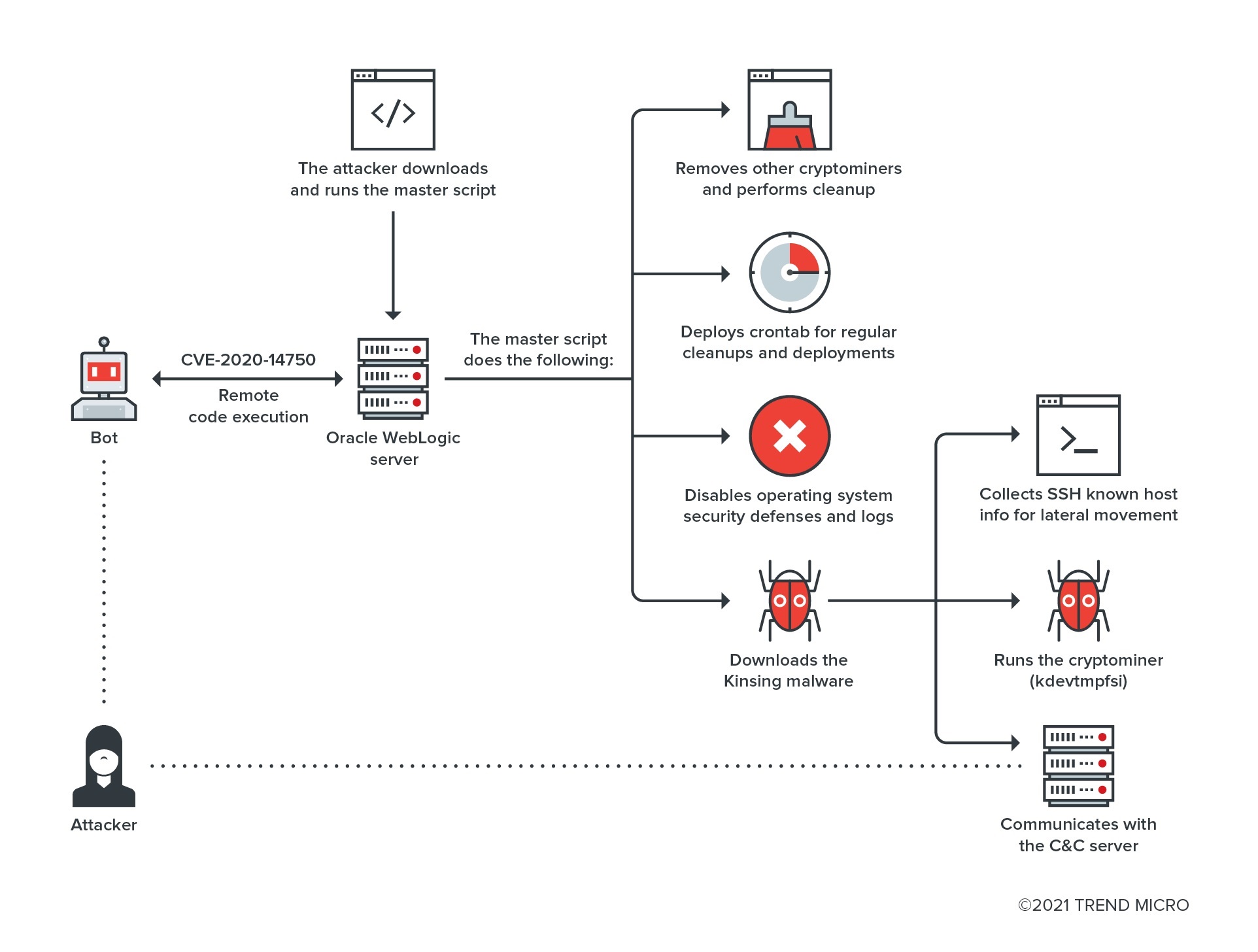
The Oracle WebLogic Server Admin Console RCE vulnerability CVE-2020-14750, which was publicised in November 2020, is still highly exploited by malware campaigns like the Kinsing malware, as we confirmed from our honeypots and customer trigger data.
The Kinsing campaign involves disabling other malware and security solutions, cleaning logs, and creating commands before loading the main cryptominer payload. The network can get infected by connecting to each device laterally, so malware can be activated in all the machines connected to the targeted network.
We took a deep dive into the Kinsing campaign techniques in our tech brief.
We used Cloud One and Trend Micro Vision One to help analyse this campaign. We discuss our detections in the following section.
Trend Micro Cloud One
IPS detection
Through IPS, we were able to detect an incoming malicious behaviour that exploits CVE-2020-14882. This was identified through rule 1010590 - Oracle WebLogic Server RCE vulnerabilities CVE-2020-14882, CVE-2020-14750, and CVE-2020-14883.


Antimalware Detections
We were then able to detect several malicious files: the master script (detected by Trend Micro as Trojan.SH.CVE20207961.SM), Kinsing (detected by Trend Micro as Coinminer.Linux.MALXMR.PUWEMA), and Kdevtmpfsi (detected by Trend Micro as Coinminer.Linux.MALXMR.SMDSL64).



Trend Micro Vision One
Trend Micro Vision One Workbench
Through Trend Micro Vision One, we were able to track the activities related to the Kinsing campaign. This includes vulnerability exploitation, suspicious outbound traffic, bash shell script execution, and the presence of a malicious component (kdevtmpfsi).



Root Cause Analysis
The root cause analysis shows more insight into the behaviour of the shell script, as well as how kdevtmpfsi emerged from Kinsing.


Trend Micro Vision One Observed Attack Techniques (OAT) Triggers
Trend Micro Vision One OAT shows the detection of the vulnerability exploitation. The risk level is marked as High.
How to Protect Systems Against Vulnerability Exploit Campaigns
Vulnerability exploits can heavily compromise user and enterprise systems. The following are some of the best practises to combat these threats.
It is highly recommended for administrators to apply all patches as soon as possible, especially if their deployed servers match the known affected versions. This recommendation is also a possible preventative measure. Both Atlassian and Oracle WebLogic servers have released security guidelines for the vulnerabilities discussed here.
In addition to the vendor patches, security solutions can also help in further securing the system.
Trend Micro Vision One helps security teams have an overall view of attempts in ongoing campaigns by providing them a correlated view of multiple layers such as email, endpoints, email, endpoints, servers, and cloud workloads. Security teams can gain a broader perspective and a better understanding of attack attempts and detect suspicious behaviour that would otherwise seem benign when viewed from a single layer alone.
Trend Micro Cloud One – Workload Security helps defend systems against vulnerability exploits, malware, and unauthorised change. It can protect a variety of environments such as virtual, physical, cloud, and containers. Using advanced techniques like machine learning (ML) and virtual patching, the solution can automatically secure new and existing workloads both against known and new threats.
Trend Micro™ Deep Security™ ensures malware prevention and network security and system security. Combined with Vulnerability Protection, it defends user systems from threats that target vulnerabilities. Both solutions protect users from exploits that target CVE-2021-26084 via the following rules:
- 1011117 - Atlassian Confluence Server RCE vulnerability CVE-2021-26084
This rule is shipped in prevent mode by default and is included in the recommendation scan
- 1005934 - Identified Suspicious Command Injection Attack
These solutions also protect users from exploits that target CVE-2020-14750, CVE-2020-14882, and CVE-2020-14883 through the following rules:
- 1010590 - Oracle WebLogic Server RCE vulnerabilities CVE-2020-14882, CVE-2020-14750, and CVE-2020-14883
This rule is shipped in prevent mode by default and is included in the recommendation scan.
- 1004090 - Identified Directory Traversal Sequence In Uri
Indicators of Compromise (IOCs)
Muhstik campaign
File Name |
SHA 256 |
Trend Micro Pattern Detection |
pty86 |
0e574fd30e806fae4298b3cbccb8d1089454f42f52892f87554325cb352646049 |
|
m8 |
3dbcd99edb3422b8fdc458b82aa7ecfe31296d32bb4d54450c9e9cac29fb6141 |
|
kswapd |
a254a26a27e36de4d96b6023f2dc8a82c4c4160a1d72b822f34ffdd5e9a0e0c9 |
IPs
hxxp://188[.]166[.]137[.]241/wp-content/themes/twentyseventeen/dk86
hxxp://153[.]121[.]58[.]102:80/wp-content/themes/zuki/m8
hxxp://3[.]10.224[.]87/[.]a/dk86
Kinsing campaign
File Name |
SHA 256 |
Trend Micro Pattern Detection |
wb.sh |
61879d5b2f083b69e8e6cc6afce00be6619176151b093de14f2778a87ea46565 |
|
kinsing |
|
|
kdevtmpfsi |
|
IPs
hxxp://194[.]38[.]20[.]199/wb.sh
hxxp://194[.]38[.]20[.]199/kinsing

