Ensure that all your IAM user access keys are rotated every month in order to decrease the likelihood of accidental exposures and protect your AWS resources against unauthorized access.
This rule can help you with the following compliance standards:
- HIPAA
- APRA
- MAS
- NIST4
For further details on compliance standards supported by Conformity, see here.
This rule can help you work with the AWS Well-Architected Framework.
This rule resolution is part of the Conformity Security & Compliance tool for AWS.
Rotating Identity and Access Management (IAM) credentials periodically will significantly reduce the chances that a compromised set of access keys can be used without your knowledge to access certain components within your AWS account.
Audit
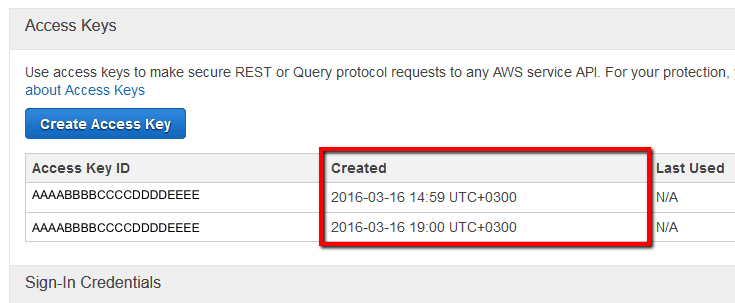
To determine if your AWS IAM users have any outdated (> 45 days) access keys currently in use, perform the following:
Remediation / Resolution
To rotate (change) your outdated IAM access keys, you need to perform the following:
References
- AWS Documentation
- AWS Identity and Access Management FAQs
- Best Practices for Managing AWS Access Keys
- IAM Best Practices
- Managing Access Keys for IAM Users
- AWS Command Line Interface (CLI) Documentation
- iam
- list-users
- list-access-keys
- create-access-key
- update-access-key
- get-access-key-last-used
- delete-access-key