PHP_WEBSHELL.XUU
Windows


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It executes when a user accesses certain websites where it is hosted. It may be downloaded from remote sites by other malware.
It executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes when a user accesses certain websites where it is hosted.
It may be downloaded from remote site(s) by the following malware:
Installation
This backdoor drops the following component file(s):
- {malware path}\.htaccess
- {malware path}\r00t.pl
- {malware path}\r00t.php
- {malware path}\serverLC.sh
- {malware path}\port.py
- {malware path}\ini.php
- {malware path}\php.ini
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- view/open directory/drives
- open/edit/rename/delete/upload arbitrary files
- execute shell command
- execute eval command
- manipulate sql database (requires login)
- Dump database (requries login)
- get php info
- download arbitrary file
- send email to arbitrary sender
- traceroute server
- execute ddos attack
- change index(Joomla, vBulletin)
- send exploit code(Python, CGI Telnet v.1,CGI Telnet v.13)
- change config (php,python,litespeed, .ini)
- Mass deface(Folders, Joomla, WordPress)
- Zone-H deface
- Reset Password (MySql,WHMCS,Joomla,Wordpress)
- Brute force login Wordpress
- Brute force login Joomla
- Brute force login Cpanel
- Compute for hash of the given string
- Hash Identification
- Query Whois
- Bypass cloudflare
- script encrypt/decrypt
- Joomla Server Scan
- Admin Finder
- Download Hacking Guides
- search google for info about system info
- search http://milw0rm.com/search.php?dong for system info
- portscan
- netsploit
- jumping
- Drop component files in {malware path}
Information Theft
This backdoor gathers the following data:
- server software
- username
- safemode status
- sql status
- curl status
- wget status
- oracle status
- mssql status
- perl status
- python status
- ruby status
- gcc status
- java status
- List of Drives
- IP
- server admin
- OS Version
- OS Name
- php version
- php sapi name
- traceroute
- Disk free space
- disk total space
- Current Directory
NOTES:
This malware is capable of appending arbitrary codes to its target file path.
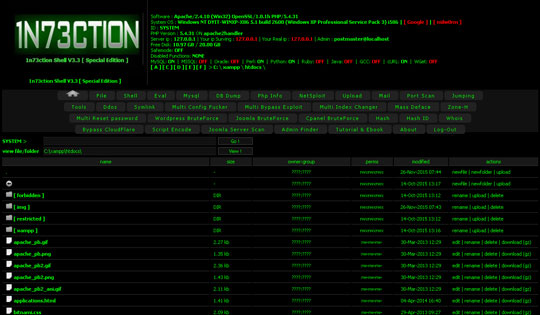
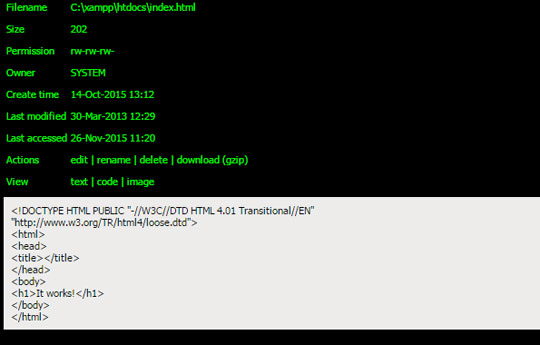
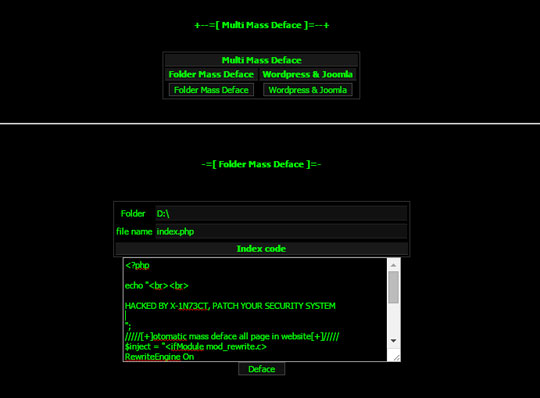
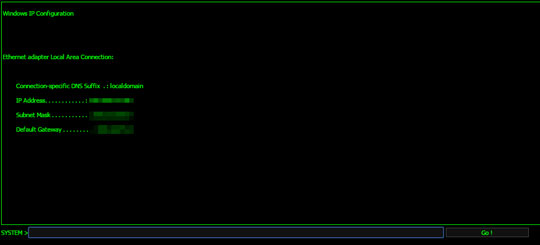
The following are some of the images when the file is accessed:
The homepage with the list of files and folders along with its stolen information:
The file content with options for file manipulation:
The following are the tools it can drop:

Below is a sample of customized code editing on its targeted file path:
This is the execution of shell code:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Remove the malware/grayware file that dropped/downloaded PHP_WEBSHELL.XUU. (Note: Please skip this step if the threat(s) listed below have already been removed.)
Step 3
Search and delete these files
- {malware path}\.htaccess
- {malware path}\r00t.pl
- {malware path}\r00t.php
- {malware path}\serverLC.sh
- {malware path}\port.py
- {malware path}\ini.php
- {malware path}\php.ini
Step 4
Scan your computer with your Trend Micro product to delete files detected as PHP_WEBSHELL.XUU. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


