Ransom.Win32.MEDUSA.SM
Win32:RansomX-gen [Ransom] (AVAST)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
637,440 bytes
EXE
No
23 Sep 2023
Disables AV, Encrypts files, Terminates processes, Deletes files
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following processes:
- net stop "{Service name}" /y
- taskkill /F /im {Process name} /T
- vssadmin Delete Shadows /all /quiet
- vssadmin resize shadowstorage /for={Drive letter} /on={Drive letter} /maxsize={Size in MB}
- vssadmin resize shadowstorage /for={Drive letter} /on={Drive letter} /maxsize=unbounded
- cmd /c ping localhost -n 3 > nul; & del {Malware Name}
- powershell -executionpolicy bypass -File {Powershell script path}
- powershell -Command "& {{Powershell script path}}"
Process Termination
This Ransomware terminates the following services if found on the affected system:
- via net stop:
- Acronis VSS Provider
- Enterprise Client Service
- Sophos Agent
- Sophos AutoUpdate Service
- Sophos Clean Service
- Sophos Device Control Service
- Sophos File Scanner Service
- Sophos Health Service
- Sophos MCS Agent
- Sophos MCS Client
- Sophos Message Router
- Sophos Safestore Service
- Sophos System Protection Service
- Sophos Web Control Service
- SQLsafe Backup Service
- SQLsafe Filter Service
- Symantec System Recovery
- Veeam Backup Catalog Data Service
- AcronisAgent
- AcrSch2Svc
- Antivirus
- ARSM
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExecDeviceMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- BackupExecVSSProvider
- bedbg
- fDCAgent
- EPSecurityService
- EPUpdateService
- EraserSvc11710
- EsgShKernel
- FA_Scheduler
- IISAdmin
- IMAP4Svc
- macmnsvc
- masvc
- MBAMService
- MBEndpointAgent
- McAfeeEngineService
- McAfeeFramework
- McAfeeFrameworkMcAfeeFramework
- McShield
- McTaskManager
- mfemms
- mfevtp
- MMS
- mozyprobackup
- MsDtsServer
- MsDtsServer100
- MsDtsServer110
- MSExchangeES
- MSExchangeIS
- MSExchangeMGMT
- MSExchangeMTA
- MSExchangeSA
- MSExchangeSRS
- MSOLAP$SQL_2008
- MSOLAP$SYSTEM_BGC
- MSOLAP$TPS
- MSOLAP$TPSAMA
- MSSQL$BKUPEXEC
- MSSQL$ECWDB2
- MSSQL$PRACTICEMGT
- MSSQL$PRACTTICEBGC
- MSSQL$PROFXENGAGEMENT
- MSSQL$SBSMONITORING
- MSSQL$SHAREPOINT
- MSSQL$SQL_2008
- MSSQL$SYSTEM_BGC
- MSSQL$TPS
- MSSQL$TPSAMA
- MSSQL$VEEAMSQL2008R2
- MSSQL$VEEAMSQL2012
- MSSQLFDLauncher
- MSSQLFDLauncher$PROFXENGAGEMENT
- MSSQLFDLauncher$SBSMONITORING
- MSSQLFDLauncher$SHAREPOINT
- MSSQLFDLauncher$SQL_2008
- MSSQLFDLauncher$SYSTEM_BGC
- MSSQLFDLauncher$TPS
- MSSQLFDLauncher$TPSAMA
- MSSQLSERVER
- MSSQLServerADHelper100
- MSSQLServerOLAPService
- MySQL80
- MySQL57
- ntrtscan
- OracleClientCache80
- PDVFSService
- POP3Svc
- ReportServer
- ReportServer$SQL_2008
- ReportServer$SYSTEM_BGC
- ReportServer$TPS
- ReportServer$TPSAMA
- RESvc
- sacsvr
- SamSs
- SAVAdminService
- SAVService
- SDRSVC
- SepMasterService
- ShMonitor
- Smcinst
- SmcService
- SMTPSvc
- SNAC
- SntpService
- sophossps
- SQLAgent$BKUPEXEC
- SQLAgent$ECWDB2
- SQLAgent$PRACTTICEBGC
- SQLAgent$PRACTTICEMGT
- SQLAgent$PROFXENGAGEMENT
- SQLAgent$SBSMONITORING
- SQLAgent$SHAREPOINT
- SQLAgent$SQL_2008
- SQLAgent$SYSTEM_BGC
- SQLAgent$TPS
- SQLAgent$TPSAMA
- SQLAgent$VEEAMSQL2008R2
- SQLAgent$VEEAMSQL2012
- SQLBrowser
- SQLSafeOLRService
- SQLSERVERAGENT
- SQLTELEMETRY
- SQLTELEMETRY$ECWDB2
- SQLWriter
- SstpSvc
- svcGenericHost
- swi_filter
- swi_service
- swi_update_64
- TmCCSF
- tmlisten
- TrueKey
- TrueKeyScheduler
- TrueKeyServiceHelper
- UI0Detect
- VeeamBackupSvc
- VeeamBrokerSvc
- VeeamCatalogSvc
- VeeamCloudSvc
- VeeamDeploymentService
- VeeamDeploySvc
- VeeamEnterpriseManagerSvc
- VeeamMountSvc
- VeeamNFSSvc
- VeeamRESTSvc
- VeeamTransportSvc
- W3Svc
- wbengine
- WRSVC
- MSSQL$VEEAMSQL2008R2
- SQLAgent$VEEAMSQL2008R2
- VeeamHvIntegrationSvc
- swi_update
- SQLAgent$CXDB
- SQLAgent$CITRIX_METAFRAME
- SQL Backups
- MSSQL$PROD
- Zoolz 2 Service
- MSSQLServerADHelper
- SQLAgent$PROD
- msftesql$PROD
- NetMsmqActivator
- EhttpSrv
- ekrn
- ESHASRV
- MSSQL$SOPHOS
- SQLAgent$SOPHOS
- AVP
- klnagent
- MSSQL$SQLEXPRESS
- SQLAgent$SQLEXPRESS
- wbengine
- kavfsslp
- KAVFSGT
- KAVFS
- mfefire
It terminates the following processes if found running in the affected system's memory:
- via taskkill /F /im:
- zoolz.exe
- agntsvc.exe
- dbeng50.exe
- dbsnmp.exe
- encsvc.exe
- excel.exe
- firefoxconfig.exe
- infopath.exe
- isqlplussvc.exe
- msaccess.exe
- msftesql.exe
- mspub.exe
- mydesktopqos.exe
- mydesktopservice.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- ocautoupds.exe
- ocomm.exe
- ocssd.exe
- onenote.exe
- oracle.exe
- outlook.exe
- powerpnt.exe
- sqbcoreservice.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlservr.exe
- sqlwriter.exe
- steam.exe
- synctime.exe
- tbirdconfig.exe
- thebat.exe
- thebat64.exe
- thunderbird.exe
- visio.exe
- winword.exe
- wordpad.exe
- xfssvccon.exe
- tmlisten.exe
- PccNTMon.exe
- CNTAoSMgr.exe
- Ntrtscan.exe
- mbamtray.exe
Other Details
This Ransomware does the following:
- Creates an anonymous pipe.
- It shows its logs within the command prompt:
- It deletes itself after execution.
- It encrypts fixed, removable and network drives.
It accepts the following parameters:
- -V → Displays the Medusa ransomware version
- -d → Will not delete itslef after execution
- -f → Exclude system folder from encryption
- -i {File path} → Encrypts specified folder
- -k {File path} → Loads key from the mentioned file
- -n → Uses network drives
- -p → Skips preprocess routine(preprocess: termination of processes and services, and deletion of shadow copy)
- -s → Excludes system drive from encryption
- -t {File path} → Changes the content of the ransom note stated in the file path
- -v → Show console window
- -w {File path} → Executes the powershell command
- -x {File path} → Avoid strings mentioned in the file path
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file path:
- \Windows\
- \Windows.old\
- \PerfLogs\
- \MSOCache\
- Program Files
- Program Files (x86)
- ProgramData
It appends the following extension to the file name of the encrypted files:
- .MEDUSA
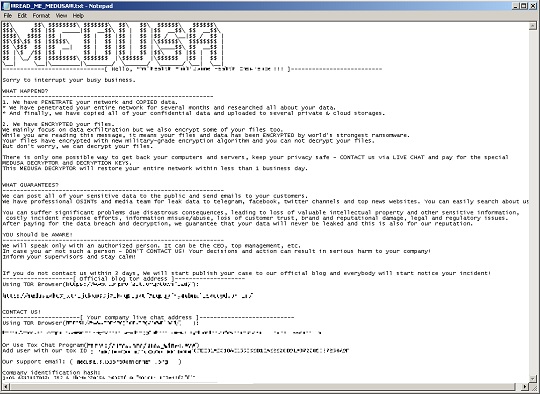
It drops the following file(s) as ransom note:
- {Encrypted directory}\!!READ_ME_MEDUSA!!.txt
- %Desktop%\!!READ_ME_MEDUSA!!.txt
It avoids encrypting files with the following file extensions:
- .dll
- .exe
- .lnk
- .MEDUSA
SOLUTION
9.800
18.314.08
15 Mar 2023
18.315.00
16 Mar 2023
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF073
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Search and delete these files
- {Encrypted directory}\!!READ_ME_MEDUSA!!.txt
- %Desktop%\!!READ_ME_MEDUSA!!.txt
Step 5
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win32.MEDUSA.SM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 6
Restore encrypted files from backup.
Did this description help? Tell us how we did.

