WORM_TDSS.TX
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Trend Micro has flagged this worm as noteworthy due to the increased potential for damage, propagation, or both, that it possesses. Specifically, it has a complex structure that enables it to evolve its behavior.
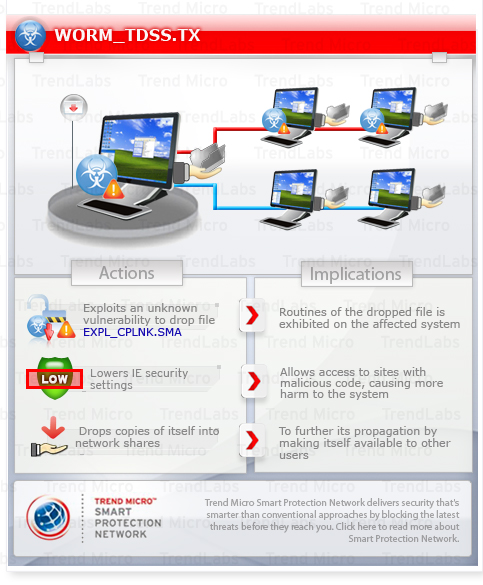
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
This worm may arrive via drive-by downloads.
When executed, it takes advantage of the following vulnerability as a zero-day exploit:
- (MS10-092) Vulnerability in Task Scheduler Could Allow Elevation of Privilege (2305420)
It also lowers Internet Explorer(IE) security settings, allowing access to sites with malicious code and causing more harm to the system.
To propagate, it drops copies of itself into network shares, thus, making itself available to other users.
This worm may be unknowingly downloaded by a user while visiting malicious websites.
It executes then deletes itself afterward.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It modifies the Internet Explorer Zone Settings.
TECHNICAL DETAILS
Arrival Details
This worm may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This worm executes then deletes itself afterward.
Other System Modifications
This worm adds the following registry entries:
HKEY_USERS\.DEFAULT\Software\
Microsoft\Internet Explorer\international
acceptlanguage = en-us
HKEY_USERS\.DEFAULT\Software\
Microsoft\Internet Explorer\Main\
featurecontrol\FEATURE_BROWSER_EMULATION
svchost.exe = 8888
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings
maxhttpredirects = 8888
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings
enablehttp1_1 = 1
It modifies the following registry entries:
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings\Zones\3
CurrentLevel = 0
(Note: The default value data of the said registry entry is 69632.)
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings\Zones\3
1601 = 0
(Note: The default value data of the said registry entry is 1.)
Propagation
This worm uses the following file names for the copies it drops into shared networks:
- setup{random number}.dll
- setup{random number}.dat
This worm drops the following component in shared networks:
- setup{random number}.lnk - detected as EXPL_CPLNK.SMA
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
Web Browser Home Page and Search Page Modification
This worm modifies the Internet Explorer Zone Settings.
Other Details
This worm is a zero-day exploit for the following vulnerability:
- Windows Task Scheduler Privilege Escalation
More information on this vulnerability can be found below:
- (MS10-092) Vulnerability in Task Scheduler Could Allow Elevation of Privilege (2305420)
It does the following:
- Creates a copy of itself named %User Temp%\{random file name}.TMP
- Changes its file characteristics to that of a .DLL file
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
SOLUTION
Step 1
For Windows ME and XP users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Scan your computer with your Trend Micro product and note files detected as WORM_TDSS.TX
Step 4
Restart in Safe Mode
Step 5
Search and delete the file detected as WORM_TDSS.TX
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Internet Explorer\international
- acceptlanguage = en-us
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Internet Explorer\Main\featurecontrol\FEATURE_BROWSER_EMULATION
- svchost.exe = 8888
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings
- maxhttpredirects = 8888
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings
- enablehttp1_1 = 1
Step 7
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3
- From: CurrentLevel = 0
To: CurrentLevel = 69632
- From: CurrentLevel = 0
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3
- From: 1601 = 0
To: 1601 = 1
- From: 1601 = 0
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_TDSS.TX If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 9
Download and apply this security patch Refrain from using these products until the appropriate patches have been installed. Trend Micro advises users to download critical patches upon release by vendors.
Did this description help? Tell us how we did.


