TSPY_FAREIT.SMC
a variant of Win32/Injector.XSI trojan (NOD32), Troj/Karag-K (Sophos)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This spyware arrives as a fake Adobe Flash Player update. It is spammed in email with subjects referring to WebEx and to PayPal.
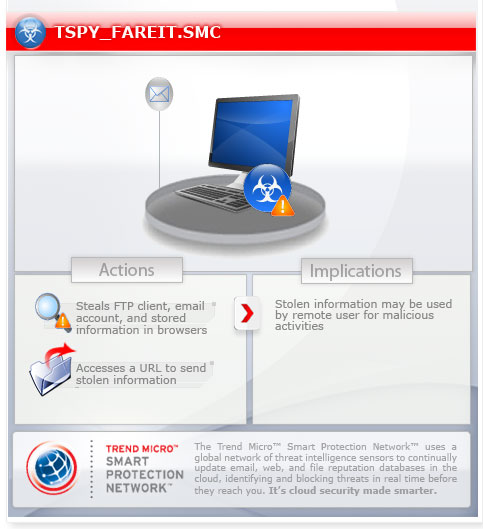
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This spyware may be unknowingly downloaded by a user while visiting malicious websites.
It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
TECHNICAL DETAILS
Arrival Details
This spyware may be unknowingly downloaded by a user while visiting malicious websites.
Download Routine
This spyware accesses the following websites to download files:
- http://{BLOCKED}up.biz/S2QsWCUk.exe - detected as TSPY_ZBOT.LAG
- http://www.{BLOCKED}yaoriente.com.co/pbe.exe - detected as TSPY_ZBOT.LAG
It saves the files it downloads using the following names:
- %User Temp%\{random number}.exe
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://{BLOCKED}.{BLOCKED}.25.255/forum/viewtopic.php
- http://{BLOCKED}.{BLOCKED}.53.38/forum/viewtopic.php
NOTES:
It attempts to steal stored account information of the following installed FTP clients or File Managers:
- LAceFTP
- 32BitFtp
- 3D-FTP
- BPFTP
- BlazeFtp
- BulletProof FTP Client
- DeluxeFTP
- EasyFTP
- Estsoft
- FFFTP (Sota)
- FTP CONTROL
- FTP Commander
- FTP Explorer
- FTP Navigator
- FTP Now
- FTP++
- FTPCON
- FTPClient
- FTPGetter
- FTPRush
- FTPShell
- FTPVoyager
- FTPWare
- Far Manager
- FileZilla
- FreshFTP
- Ghisler
- GlobalSCAPE CuteFTP 6 Home
- GlobalSCAPE CuteFTP 6 Professional
- GlobalSCAPE CuteFTP 7 Home
- GlobalSCAPE CuteFTP 7 Professional
- GlobalSCAPE CuteFTP 8 Home
- GlobalSCAPE CuteFTP 8 Professional
- GoFTP
- Ipswitch WS_FTP
- LeapWare LeapFTP
- LeechFTP
- LinasFTP
- MAS-Soft FTPInfo
- MS IE FTP Passwords
- NCH Software ClassicFTP
- NovaFTP
- Robo-FTP 3.7
- SmartFTP
- SoftX.org FTPClient
- Staff-FTP
- TurboFTP
- WS_FTP
- WinFTP
- Ftp Winzip (Nico Mak Computing)
- Coffee Cup Free FTP
- PuTTY
- salt-ftp
It gathers the following account information from any of the aforementioned FTP clients or File Managers:
- Password
- Port Number
- Server Name
- Server Type
- User Name
- Directory list
It also attempts to steal stored email credentials:
- Outlook
- Windows Live Mail
- Windows Mail
- Pocomail
- IncrediMail
- BatMail
- Thunderbird
This spyware attempts to retrieve stored information such as user names, passwords, and hostnames from the following browsers:
- Google Chrome
- Mozilla Firefox
- Internet Explorer
- Opera Browser
- Flock Browser
- RockMelt
- K-Meleon
- FastStone Browser
This spyware uses the following list of user names and passwords to access password-protected locations where the aforementioned information are stored:
- 123456
- password
- phpbb
- qwerty
- 12345
- jesus
- 12345678
- abc123
- letmein
- password1
- hello
- monkey
- dragon
- trustno1
- 111111
- iloveyou
- 1234567
- shadow
- 123456789
- christ
- sunshine
- master
- computer
- princess
- tigger
- football
- angel
- jesus1
- 123123
- whatever
- freedom
- killer
- soccer
- superman
- michael
- cheese
- internet
- joshua
- fuckyou
- blessed
- baseball
- starwars
- 000000
- purple
- jordan
- faith
- summer
- ashley
- buster
- heaven
- pepper
- 7777777
- hunter
- lovely
- andrew
- thomas
- angels
- charlie
- daniel
- jennifer
- single
- hannah
- qazwsx
- happy
- matrix
- aaaaaa
- 654321
- amanda
- nothing
- ginger
- mother
- snoopy
- jessica
- welcome
- pokemon
- iloveyou1
- 11111
- mustang
- helpme
- justin
- jasmine
- orange
- testing
- apple
- michelle
- peace
- secret
- grace
- william
- iloveyou2
- nicole
- 666666
- muffin
- gateway
- fuckyou1
- asshole
- hahaha
- blessing
- blahblah
- myspace1
- matthew
- canada
- silver
- robert
- forever
- asdfgh
- rachel
- rainbow
- guitar
- peanut
- batman
- cookie
- bailey
- soccer1
- mickey
- biteme
- hello1
- eminem
- dakota
- samantha
- compaq
- diamond
- taylor
- forum
- john316
- richard
- blink182
- peaches
- flower
- scooter
- banana
- james
- asdfasdf
- victory
- london
- 123qwe
- 123321
- startrek
- george
- winner
- maggie
- trinity
- online
- 123abc
- chicken
- junior
- chris
- passw0rd
- austin
- sparky
- admin
- merlin
- friends
- shalom
- nintendo
- looking
- harley
- smokey
- joseph
- lucky
- digital
- thunder
- spirit
- bandit
- enter
- anthony
- corvette
- hockey
- power
- benjamin
- iloveyou!
- 1q2w3e
- viper
- genesis
- knight
- qwerty1
- creative
- foobar
- adidas
- rotimi
- slayer
- wisdom
- praise
- zxcvbnm
- samuel
- dallas
- green
- testtest
- maverick
- onelove
- david
- mylove
- church
- friend
- destiny
- microsoft
- 222222
- bubbles
- 11111111
- cocacola
- jordan23
- ilovegod
- football1
- loving
- nathan
- emmanuel
- scooby
- fuckoff
- sammy
- maxwell
- jason
- 1q2w3e4r
- red123
- blabla prince
- qwert
- chelsea
- 55555
- angel1
- hardcore
- dexter
- saved
- 112233
- hallo
- jasper
- danielle
- kitten
- cassie
- stella
- prayer
- hotdog
- windows
- mustdie
- gates
- billgates
- ghbdtn
- gfhjkm
- 1234567890
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 3
Identify and terminate files detected as TSPY_FAREIT.SMC
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Scan your computer with your Trend Micro product to delete files detected as TSPY_FAREIT.SMC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

