TROJ_ZBOT.BXW
Windows 2000, XP, Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Trend Micro has flagged this Trojan as noteworthy due to the increased potential for damage, propagation, or both, that it possesses. It also uses social engineering methods to lure users into performing certain actions that may, directly or indirectly, cause malicious routines to be performed
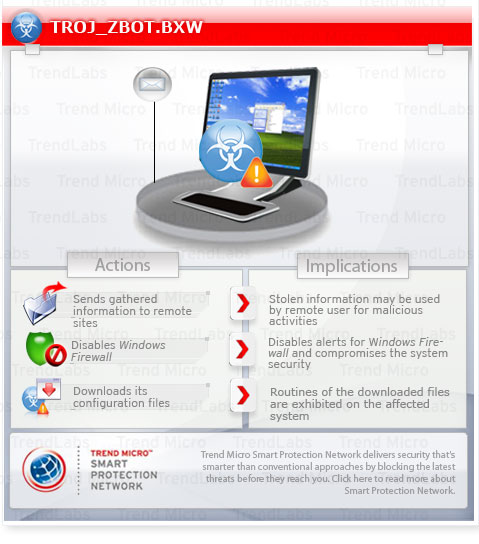
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan adds registry entries to enable its automatic execution at every system startup.
It opens random ports. It runs certain commands that it receives remotely from a malicious user. Doing this puts the affected computer and information found on the coomputer at greater risk.
It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
It attempts to steal sensitive online banking information, such as user names and passwords. This routine risks the exposure of the user's account information, which may then lead to the unauthorized use of the stolen data.
TECHNICAL DETAILS
Installation
This Trojan creates the following folders:
- %Application Data%\{random1}
- %Application Data%\{random2}
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.)
It is injected into the following processes running in memory:
- ctfmon.exe
- dwm.exe
- explorer.exe
- rdpclip.exe
- taskeng.exe
- taskhost.exe
- wscntfy.exe
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{GUID} = {malware path and file name}
Other System Modifications
This Trojan creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
%Windows%\\Explorer.exe = "%Windows%\Explorer.exe:*:Enabled:Windows Explorer"
Backdoor Routine
This Trojan opens a random port to allow a remote user to connect to the affected system. Once a successful connection is established, the remote user executes commands on the affected system.
It executes the following command(s) from a remote malicious user:
- Gets the Flash player data
- Steals passwords from FlashFXP, total_commander, ws_ftp, fileZilla, FAR2, winscp, ftp_commander, coreFTP, and smartftp
- Set the browser’s home page
- Disable and enable access to certain URLs
- Remove certificate
- Steal digital certificates
- Delete browser cookies
- Upload cookies
- Download and execute a file
- Removes a back door connection
- Download and update bot configuration
- Uninstall bot
- Restart the system
- Shutdown the system
- Disable and enable web injection
- Search local drives
Dropping Routine
This Trojan drops the following files:
- %Application Data%\{random1}\{random}.exe - copy of itself
- %Application Data%\{random2}\{random}.{3 random alpha character extension name} - encrypted file
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.)
Download Routine
This Trojan saves the files it downloads using the following names:
- %User Temp%\kjfhgjdsfgsd.exe - also detected as TROJ_ZBOT.BXW
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Information Theft
This Trojan attempts to steal sensitive online banking information, such as user names and passwords. This routine risks the exposure of the user's account information, which may then lead to the unauthorized use of the stolen data.
It accesses the following site to download its configuration file:
- http://{BLOCKED}et.cn/zeka/cfg9sksl.jpg
Other Details
Based on analysis of the codes, it has the following capabilities:
- Saves its encrypted configuration file in a random key created under the registry, HKEY_CURRENT_USER\Software\Microsoft
- Injects codes to online banking Web sites included in its configuration file. However, as of this moment the downloaded configuration file only contains the links to its updated copy and drop zone, http://{BLOCKED}et.cn/zeka/getbotdata930sdla.php
- Takes screenshots and log keystrokes
- Exploits the vulnerability, Microsoft Security Advisory (2286198) which is detected as LNK_STUXNET.SM
SOLUTION
Step 1
Remove malware files dropped/downloaded by TROJ_ZBOT.BXW
- LNK_STUXNET.SM
Step 2
Scan your computer with your Trend Micro product and note files detected as TROJ_ZBOT.BXW
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {GUID} = {malware path and file name}
- {GUID} = {malware path and file name}
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- %Windows%\Explorer.exe = %Windows%\Explorer.exe:*:Enabled:Windows Explorer
- %Windows%\Explorer.exe = %Windows%\Explorer.exe:*:Enabled:Windows Explorer
Step 5
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_ZBOT.BXW If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


