RANSOM_SURVEYLOCK.B
W32/PCsurveyLocker.HK!tr (Fortinet); TR/LockScreen.oxguz (Avira); MSIL/LockScreen.QY (ESET-NOD32); Ransom.PCsurveyLocker (Symantec); Ransom.PClock (Malwarebytes)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
Shell = "{malware path and filename}"
Other System Modifications
This Trojan adds the following registry entries:
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoNavBar = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoSelectDownloadDir = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoBrowserSaveAs = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoFavorites = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoFindFiles = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoViewSource = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoToolBar = "1"
HKEY_LOCAL_MACHINE\Software\policies\
Microsoft\Internet Explorer\Toolbars\
Restrictions
NoLinksBar = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Control
WaitToKillServiceTimeout = "2000"
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows\System
AllowBlockingAppsAtShutdown = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
EnableSmartScreen = "0" (for Windows 8, 8.1, Server 2012 and Server 2012 R2)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
EnableLUA = "0" (for Windows Vista, 7, 8, 8.1, Server 2008, Server 2008 R2, Server 2012 and Server 2012 R2)
It deletes the following registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Runtest
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Runtest
Other Details
This Trojan does the following:
- It hides the taskmgr.exe window when the user tries to run it.
- It automatically restarts the system after the registry modifications.
NOTES:
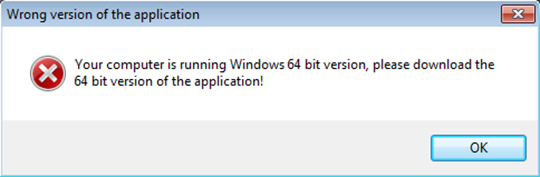
This ransomware does not support 64-bit systems, instead it will display an error when executed.
It also does not encrypt any of your files, instead the following lockscreen will be displayed:
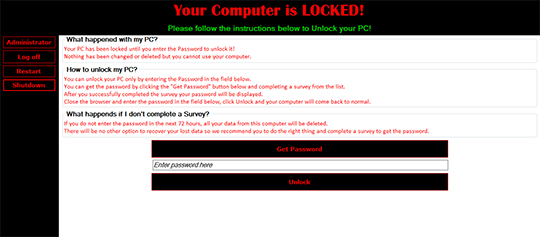
It will then ask you to answer a survey to get the password for unlocking the machine. Upon clicking on Get Password button, it will open the website "http://{BLOCKED}t-8-hack.com/start.html" with Firefox browser. However, the said website is no longer accessible.
It also displays the following message box if the user clicks the Unlock button and the password is incorrect:
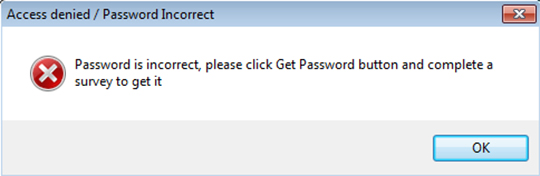
It requires the code "london1969paris" to unlock the screen. However, the registry modifications will not be restored to normal thus the screen will not continue to Desktop and will only be blank. A restart of the machine will only show the lock screen again.
Clicking on the Administrator button will show a login box:
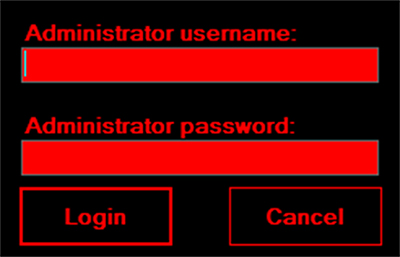
It requires the following account login:
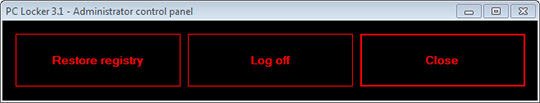
Upon successful login, it will show a control panel:
SOLUTION
Step 1
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 2
Restart in Safe Mode
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoNavBar = "1"
- NoNavBar = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoSelectDownloadDir = "1"
- NoSelectDownloadDir = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoBrowserSaveAs = "1"
- NoBrowserSaveAs = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoFavorites = "1"
- NoFavorites = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoFindFiles = "1"
- NoFindFiles = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoViewSource = "1"
- NoViewSource = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoToolBar = "1"
- NoToolBar = "1"
- In HKEY_LOCAL_MACHINE\Software\policies\Microsoft\Internet Explorer\Toolbars\Restrictions
- NoLinksBar = "1"
- NoLinksBar = "1"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control
- WaitToKillServiceTimeout = "2000"
- WaitToKillServiceTimeout = "2000"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System
- AllowBlockingAppsAtShutdown = "1"
- AllowBlockingAppsAtShutdown = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- EnableSmartScreen = "0" (for Windows 8, 8.1, Server 2012 and Server 2012 R2)
- EnableSmartScreen = "0" (for Windows 8, 8.1, Server 2012 and Server 2012 R2)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- EnableLUA = "0" (for Windows Vista, 7, 8, 8.1, Server 2008, Server 2008 R2, Server 2012 and Server 2012 R2)
- EnableLUA = "0" (for Windows Vista, 7, 8, 8.1, Server 2008, Server 2008 R2, Server 2012 and Server 2012 R2)
Step 4
Restore these deleted registry keys/values from backup
*Note: Only Microsoft-related keys/values will be restored. If the malware/grayware also deleted registry keys/values related to programs that are not from Microsoft, please reinstall those programs on your computer.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion
- Runtest
- Runtest
- In HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion
- Runtest
- Runtest
Step 5
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_SURVEYLOCK.B. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
Proceed with the following after Step 1:
This malware has characteristics that require the computer to be restarted in safe mode. Proceed with the instructions below but choose Safe Mode with Command Prompt instead of Safe Mode only.
After Step 3, do the following:
Removing Entries from the Registry using the Command Prompt
Did this description help? Tell us how we did.

