RANSOM_ARTTEC.DJB
Linux.Trojan(Norton);a variant of Linux/Filecoder.F(Eset-NOD32);ELF:Filecoder-K [Trj](Avast)
Linux


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information.
It encrypts files with specific file extensions. It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- {encrypted file}.{original file extension}.PRM.AESKEY
Other System Modifications
This Ransomware deletes the following files:
- .bash_history
Information Theft
This Ransomware gathers the following data:
- etc/shadow
- etc/hosts
- .ssh/id_rsa
- .ssh/id_dsa
- .ssh/id_ecdsa
- .ssh/id_ed25519
- .ssh/known_hosts
Other Details
This Ransomware connects to the following website to send and receive information:
- http://www.{BLOCKED}europe.net/evl/grab/xx/get.php
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- .doc
- .xls
- .ppt
- .docx
- .xlsx
- .pptx
It appends the following extension to the file name of the encrypted files:
- .PRM.TMPFILE
It drops the following file(s) as ransom note:
- {encrypted file}.{original file extension}.info
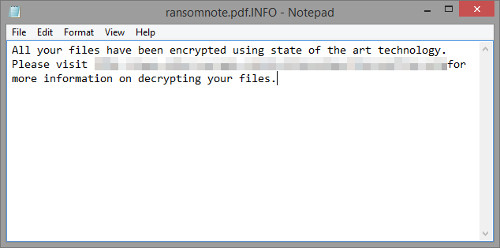
It leaves text files that serve as ransom notes containing the following text:
SOLUTION
Step 1
Scan your computer with your Trend Micro product to delete files detected as RANSOM_ARTTEC.DJB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 2
Restore encrypted files from backup.
Did this description help? Tell us how we did.