Ransom.Linux.NOESCAPE.THFOEBC
Trojan-Ransom.Noescape (IKARUS)
Linux


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It encrypts files found in specific folders. It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- /{Shell Script File Path}/motd ← Ransom note in motd format
- /{Shell Script File Path}/index.html ← Ransom note in html format
Information Theft
This Ransomware accepts the following parameters:
- /{Specific path to encrypt}/
Other Details
This Ransomware does the following:
- It requires the following file to proceed to its routines:
- script_linux.sh <- Detected as Trojan.SH.NOESCAPE.THFOEBC
- It empties the trash/recycle bin by deleting the following folder recursively:
- /.local/share/Trash/info/
- /.local/share/Trash/files/
- It performs cleanup after execution by deleting the following files:
- Log files
- Backup files
- /{Malware File Path}/{Malware Filename}.elf
- /{Malware File Path}/index.html
- /{Malware File Path}/motd
- It replaces the /etc/motd with the ransom note
- It uses the following configuration setup:
- Local Configuration Key:
- Local ID: 164f8295-{Random Characters}
- IV Key: {Random Characters}
- MP Key: {Random Characters}
- Extensions:
- Ignore: [elf, exe, lib, bin, sys]
- Full: [sql]
- Settings:
- Build type: Linux
- Add to autorun: False
- Interval: 0
- Print note: False
- Set wallpaper: False
- Large file size: 1024 mb
- Spot size: 10 mb
- Local Configuration Key:
Ransomware Routine
This Ransomware encrypts files found in the following folders:
- Home directory ← Default
It appends the following extension to the file name of the encrypted files:
- .BJDGAIHFHB
It drops the following file(s) as ransom note:
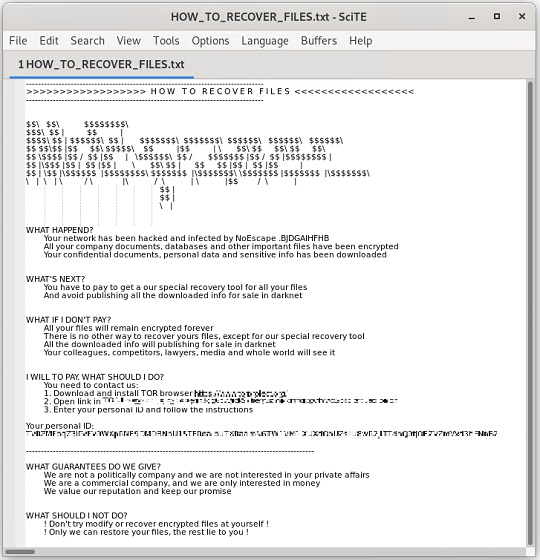
- {Encrypted Directory}\HOW_TO_RECOVER_FILES.txt
It avoids encrypting files with the following file extensions:
- .bin
- .elf
- .exe
- .lib
- .sys
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- Troj.ELF.TRX.XXELFC1DFF030
Step 2
Scan your computer with your Trend Micro product to delete files detected as Ransom.Linux.NOESCAPE.THFOEBC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 3
Restore encrypted files from backup.
Did this description help? Tell us how we did.