PHP_MADSHELL.A
PHP/WebShell.NAW (ESET), PHP.RSTBackdoor (Symantec)
Windows, Linux


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This backdoor executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
Arrival Details
This malware arrives via the following means:
- May be uploaded and installed on a web server by a remote malicious user after gaining access to the server.
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Manipulate files and directories (download, execute, create, change permissions)
- List running processes
- Perform UDP DDOS
- Execute SQL commands
- Perl and PHP back connect
- Generate hashes
- Remove shell
- Deface the site and report to Zone-H
NOTES:
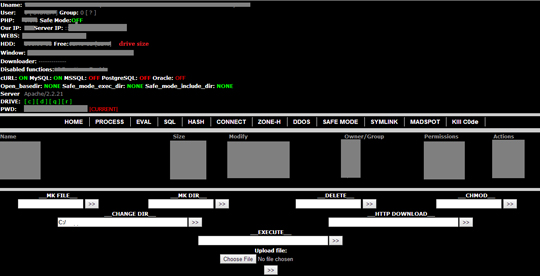
Once this PHP script is installed, the remote user may then launch a backdoor on the affected system. Opening the page, the malicious user is shown the following user interface:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as PHP_MADSHELL.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


