JS_MALAGENT.PB
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This malware is noteworthy as this is used for the Facebook spam run. When executed, it performs several actions on the user's Facebook profile.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
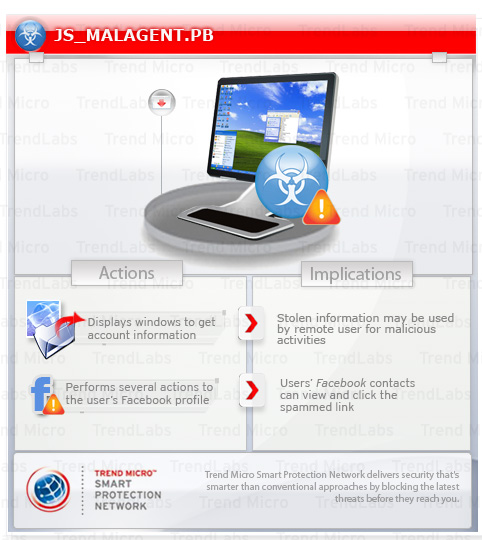
This JavaScript performs the following actions on the user's profile:
- Posts on Facebook wall and tags friends
- Likes its own post
- Comments on its own post
- Creates an event
- Creates a personalized Facebook chat message and supplies a link
This Trojan may arrive using one or multiple arrival methods.
It redirects browsers to certain sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives via the following means:
- It may be a posted message as part of clickjacking attacks on social sites such as Facebook.
Information Theft
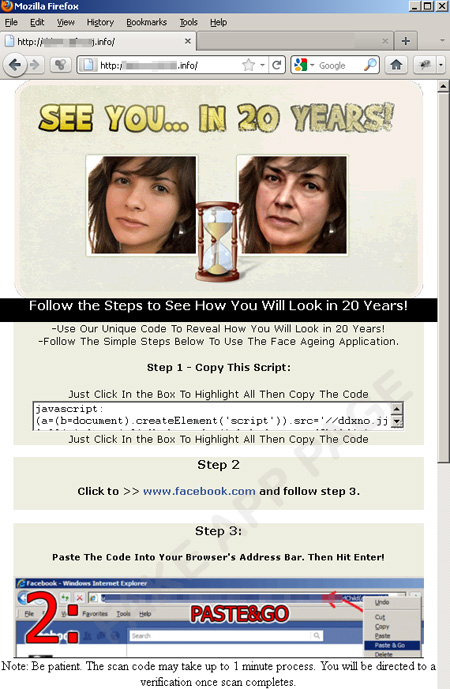
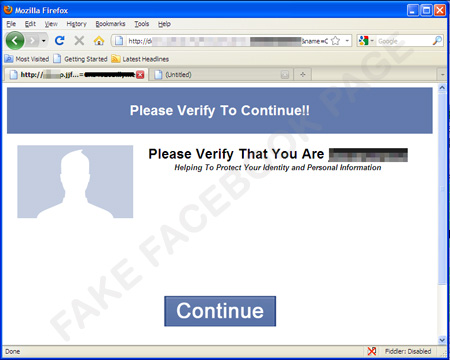
This Trojan presents the user with the following series of windows in order to obtain account information:
Other Details
This Trojan redirects browsers to the following sites:
- http://{BLOCKED}jq.{BLOCKED}vb.info//final.php
- http://{BLOCKED}no.{BLOCKED}3j.info
NOTES:
It also performs the following actions on the user's profile:
- Posts on Facebook wall and tags friends
- Likes its own post
- Comments on its own post
- Creates an event
- Creates a personalized Facebook chat message and supplies a link
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as JS_MALAGENT.PB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.