HTML_RANSOM.PPS
Troj/Ransom-NY (Sophos)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
NOTES:
This Trojan checks if there is an installed Windows PowerShell on the system. If Windows Powershell is not installed, it downloads a copy from the following sites:
- https://{BLOCKED}.{BLOCKED}x.com/sh/wn8x35r9l9wsitn/XSwafOFh9E/powershell.exe?dl=1
The downloaded file is saved as follows:
- %User Temp%\powershell\powershell.exe
It drops the following file:
- {Malware Path}\READ_ME_NOW.TXT
The file, READ_ME_NOW.TXT contains the following message:
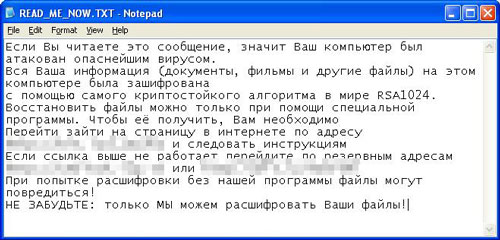
When translated in English:
If you are reading this message, it means that your computer has been attacked by viruses.
All of your information (documents, movies, and other files) on the computer was encrypted
with the most cryptographically world RSA1024.
Restore files only through a special program. To obtain it, you need to
Go to go to a page on the Internet at http://bit.ly/11Uql6s and follow the instructions
If the link above does not work, go to a backup to http://{BLOCKED}k.{BLOCKED}p.to or http://{BLOCKED}t.ly/VIertW
When you try to decrypt the files without our software can be damaged!
DO NOT FORGET: Only we can decode your files!
As of this writing, the sites in READ_ME_NOW.TXT are inaccessible.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Search and delete these files
- {Malware Path}\READ_ME_NOW.TXT
- %User Temp%\powershell\powershell.exe
Step 3
Scan your computer with your Trend Micro product to delete files detected as HTML_RANSOM.PPS. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.
