HKTL_BUILDSTEAL.GB
HackTool.Builder (Malwarebytes), SPR/Zayoh.B (Avira)
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
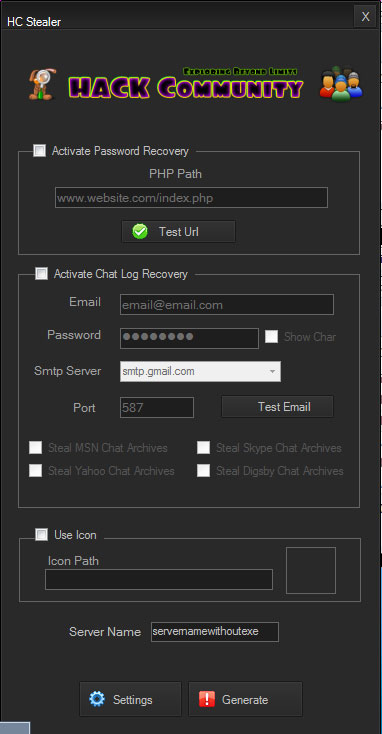
It uses a user interface (UI).
TECHNICAL DETAILS
Arrival Details
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
Other Details
This hacking tool uses the following user interfaces (UIs):
It does the following:
- Generate a password stealing executable file with the interaction of a user
NOTES:
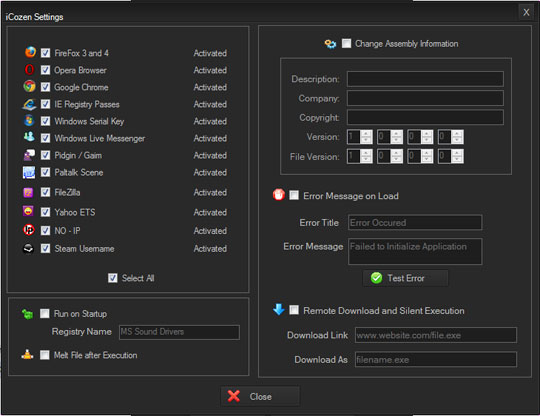
The user is able to customize the following:
- URL where the stole information will be sent
- E-mail address where the stolen information will be sent
- Icon to be use by the generated file
- Whether or not the generated file can download other files specified by the user
- Whether or not the generated file runs at startup
- What registry name to use
- Whether or not the generated file deletes itselft after execution
- What kind of information to steal based on the given choices
- Change the assembly information of the generated file (like Description, Company etc)
- Error message to be displayed by the generated file
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as HKTL_BUILDSTEAL.GB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.