HackTool.Win64.LAZAGNE.AE
HackTool:Win32/LaZagne (MICROSOFT); HackTool.Win32.LaZagne.cw (KASPERSKY)
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Hacking Tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Hacking Tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Information Theft
This Hacking Tool gathers the following data:
- Credentials from the following software:
- Browsers:
- 7Star
- Amigo
- BlackHawk
- Brave
- Centbrowser
- Chedot
- Chrome Canary
- Chromium
- Coccoc
- Comodo Dragon
- Comodo IceDragon
- Cyberfox
- Elements Browser
- Epic Privacy Browser
- Mozilla Firefox
- Google Chrome
- Icecat
- Internet Explorer
- K-Meleon
- Kometa
- Opera
- Orbitum
- Sputnik
- UCBrowser
- Torch
- Uran
- Vivaldi
- Chat Clients:
- Pidgin
- Psi
- Skype
- Databases:
- DBVisualizer
- Postgresql
- Robomongo
- Squirrel
- SQLdeveloper
- Games:
- GalconFusion
- Kalypsomedia
- RogueTale
- Turba
- Email Software:
- Outlook
- Thunderbird
- Memory:
- Keepass
- Mimikatz Method via Pypykatz
- Multimedia:
- EyeCON
- PHP:
- Composer
- System Administration Tools:
- Apache Directory Studio
- CoreFTP
- CyberDuck
- FileZilla
- FileZilla Server
- FTPNavigator
- OpenSSH
- OpenVPN
- PuttyCM
- RDPManager
- VNC
- WinSCP
- Windows Subsystem for Linux
- Windows Software:
- Autologon
- MSCache
- Credential Files
- Credman
- DPAPI Hash
- Hashdump (LM/NT)
- LSA secret
- Vault Files
- Git for Windows
- Maven Apache
- Wifi
- Browsers:
Other Details
This Hacking Tool does the following:
- It will gather credentials based on the parameter used upon execution of the application.
- It may create a txt of json file based on the parameter used upon execution of the application.
- This hacktool display the following screen for instructions:
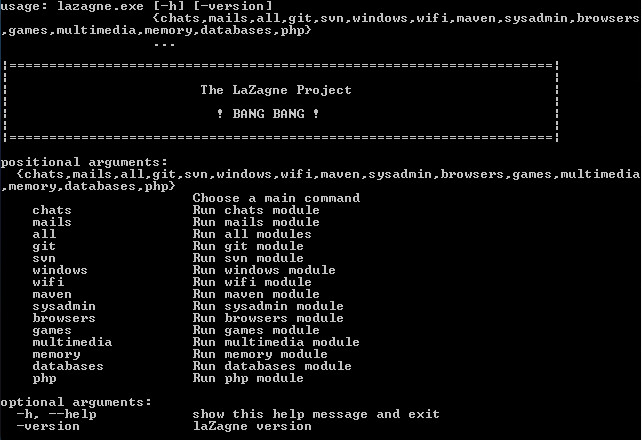
It accepts the following parameters:
- -h, --help → Show help message.
- -version → Show lazagne version.
- {module} → Specify module to run.
- all → Run all Modules.
- chats → Run chats module.
- mails → Run mails module.
- git → Run git module.
- svn → Run svn module.
- windows → Run windows module.
- wifi → Run wifi module.
- maven → Run maven module.
- sysadmin → Run sysadmin module.
- browsers → Run browsers module.
- games → Run games module.
- multimedia → Run multimedia module.
- memory → Run memory module.
- databases → Run database module.
- php → Run php module.
- -v{v...} → Modify verbosity of output with number of v.
- -quiet → Quiet Mode (No output will be shown in console).
- -{oN|oJ|oA} -output {Output Folder Path} → Write output to {Sample Folder} if no -output or specified {Output Folder Path}.
- -oN → Write Output in Normal format (as shown in console).
- -oJ → Write Output in JSON format.
- -oA → Write Output in both JSON and Normal format.
- -password {Password} → Specify known password for credential files.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Scan your computer with your Trend Micro product to delete files detected as HackTool.Win64.LAZAGNE.AE. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.

