Backdoor.PHP.WEBSHELL.SBJKSV
Backdoor:PHP/Yorcirekrikseng.E (MICROSOFT)
Windows, Unix


Threat Type: Backdoor
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be hosted on a website and run when a user accesses the said website.
It executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
Arrival Details
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be hosted on a website and run when a user accesses the said website.
Backdoor Routine
This Backdoor executes the following commands from a remote malicious user:
- Execute arbitrary command
- List directory contents
- Rename a file or a directory
- Delete a file or a directory
- Change file or directory permissions
- Edit a file
- Mass deface
- Adminer login (SQL Manager)
- Reset password
- Retrieve domains and users
- Jump server
- Grab configurations
- Use CGI Telnet v1.3
- Back connect or bind port
- Bypass functions
- Delete log files
- View log file
- Download a file
- Upload a file
- Save a file
- Brute force login
Information Theft
This Backdoor gathers the following data:
- Safe mode status
- Disable functions status
- MySQL status
- Curl status
- Wget status
- Perl status
- Python status
- OS Information
- Current Directory
- Root Directory (under which the script is executing)
Other Details
This Backdoor does the following:
- It sends a 404 Not Found header if the user-agent contains any of the following strings:
- Googlebot
- Slurp
- MSNBot
- PycURL
- facebookexternalhit
- ia_archiver
- crawler
- Yandex
- Rambler
- Yahoo!
- Slurp
- YahooSeeker
- bingbot
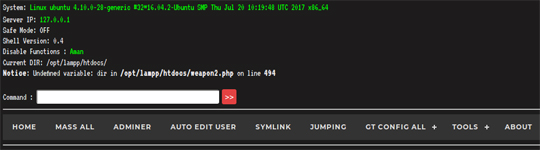
- Upon execution, it will display the following window with different tabs where the attacker can perform backdoor activities:
It requires being hosted on a web server in order to proceed with its intended routine.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as Backdoor.PHP.WEBSHELL.SBJKSV. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


