ADW_DOWNWARE.GA
AdWare.Win32.OutBrowse.g (Kaspersky)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Adware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This adware may be downloaded by other malware/grayware/spyware from remote sites. It may be manually installed by a user.
It does not have any propagation routine.
It does not have any backdoor routine.
TECHNICAL DETAILS
Arrival Details
This adware may be downloaded by other malware/grayware/spyware from remote sites.
It may be manually installed by a user.
Installation
This adware drops the following component file(s):
- %User Temp%\f.exe - also detected as ADW_DOWNWARE.GA
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It drops the following non-malicious files:
- %User Temp%\instructionsBv3.dat - deleted afterwards
- %User Temp%\{random}.tmp\Convert.dll - deleted afterwards
- %User Temp%\obhhelper.txt - deleted afterwards
- %User Temp%\{random}.tmp - deleted afterwards
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
Other System Modifications
This adware adds the following registry entries as part of its installation routine:
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}
(Default) = "CBrowserExternal Class"
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
LocalServer32
(Default) = "%User Temp%\f.exe"
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
LocalServer32
ServerExecutable = "%User Temp%\f.exe"
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
TypeLib
(Default) = "{03771AEF-400D-4A13-B712-25878EC4A3F5}"
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
Version
(Default) = "1.0"
It adds the following registry keys as part of its installation routine:
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
LocalServer32
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
Programmable
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
TypeLib
HKEY_CLASSES_ROOT\CLSID\{6D4506CE-F855-4657-AA38-DB6B1F733982}\
Version
Propagation
This adware does not have any propagation routine.
Backdoor Routine
This adware does not have any backdoor routine.
NOTES:
It executes the dropped file %User Temp%\f.exe (also detected as ADW_DOWNWARE.GA) using the following commands and parameters:
- %User Temp%\f.exe /PID={value} /SUBPID={value} /DISTID={value} /NETWORKID={value} /CID={value} /PRODUCT_ID={value} /SERVER_URL=http://installer.apps-track.com /CLICKID={value} /D1={value} /D2={value} /D3={value}/D4={value} /D5={value} /PRODUCT_NAME={value} /PRODUCT_EULA={value} /PRODUCT_PRIVACY={value} /EXE_URL={value} /EXE_CMDLINE={value} /HOST_BROWSER={value} /IS_RUNTIME={value} /THANKYOU_URL={value} /RETURNING_USER_DAYS={value} /VM={value}
It gathers the following information that will be used for survey and advertising purposes:
- Operating system
- Internet Explorer version
- Google Chrome version
- MAC address
- CPU bit count
- Computer's GUID
- Bios serial number
- Bios version
It connects to the following URL to send and receive information:
- http://{BLOCKED}ller.{BLOCKED}-track.com/Installer/Flow?pubid={value}&distid={value}&productid={value}&subpubid={value}&campaignid={value}&networkid={value}&dfb={value}&os={value}&iev={value}&ffv={value}&chromev={value}&macaddress={value}&netv={value}&d1={value}&d2={value}&d3={value}&d4={value}&d5={value}&ds1={value}&hb={value}&systembit={value}&vm={value}&machineguid={value}&diskserial={value}&version={value}
The information it receives are the following:
- Source URL where to download the contents of the installer interface
- Source URL of main and optional software installers
- Data that will be used for advertising routine
Here is a sample of URL where it will download the main software installer:
Here are samples of URLs where it will download the optional software installers:
- http://{BLOCKED}n.{BLOCKED}ad4desktop.com/Installer/Focusbase/focusbaseSetup.exe
- http://{BLOCKED}l.{BLOCKED}demoserv.com/ob23/all/hds/row/setup.exe
- http://{BLOCKED}l.{BLOCKED}emoserv.com/outil/fuully/styi2/savepass.exe
It saves the software installers using the following names:
- %User Temp%\{number}_Offer_{number}.exe
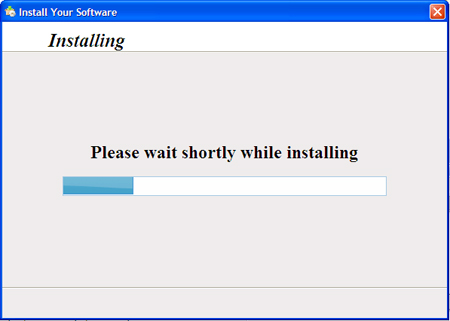
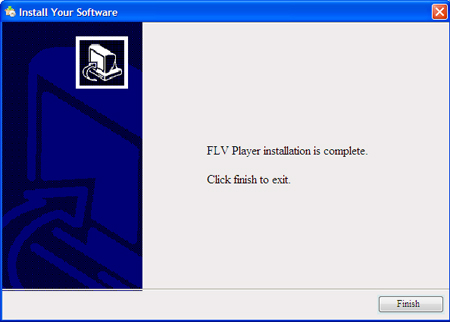
It executes the downloaded files and installs them silently in the background.
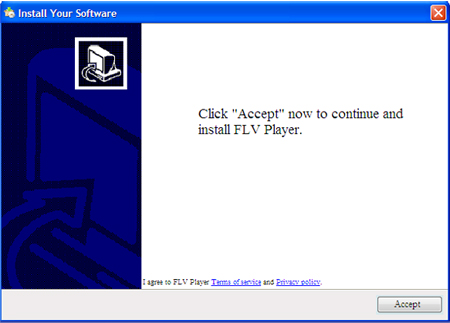
It displays the following samples of installation interface or windows:
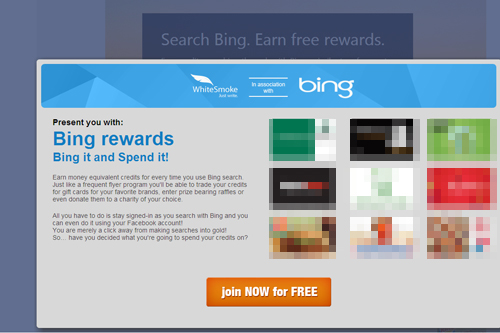
After installation, it opens a "Thank you" web page that contains advertisements:
- http://{BLOCKED}r.{BLOCKED}-track.com/installer/thankyou?productid={value}&pubid={value}&distid={value}&countryid={value}&reqid={value}&sysbit={value}&d1={value}&dfb={value}&hb={value}
It does not have rootkit capabilities.
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry. Before you could do this, you must restart in Safe Mode. For instructions on how to do this, you may refer to this page If the preceding step requires you to restart in safe mode, you may proceed to edit the system registry.
- In HKEY_CLASSES_ROOT\CLSID
- {6D4506CE-F855-4657-AA38-DB6B1F733982}
- {6D4506CE-F855-4657-AA38-DB6B1F733982}
Step 3
Search and delete these files
- %User Temp%\{number}_Offer_{number}.exe
Step 4
Scan your computer with your Trend Micro product to delete files detected as ADW_DOWNWARE.GA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
Remove the main and/or optional software using its own Uninstall option by following these steps:
- Click Start > Control Panel.
- Double-click on Programs and Features (Windows Vista and higher versions) or Add/Remove Programs (Versions lower than Windows Vista).
- In the displayed list, choose the software you installed.
- Click on Change/Remove.
- Follow the instructions on the dialog box that appears.
- Repeat step 3 for the remaining software you installed.
- Close the Programs and Features or Add/Remove Programs window, and the Control Panel window.
Did this description help? Tell us how we did.

