HKTL_KJWORM
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This mew malware is related to the release of the Njw0rm malware source code found in early January 2015.
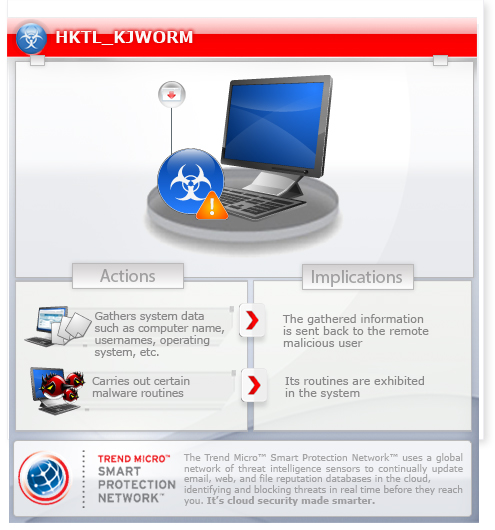
To get a one-glance comprehensive view of the behavior of this Hacking Tool, refer to the Threat Diagram shown below.
This hacking tool may be manually installed by a user.
TECHNICAL DETAILS
Arrival Details
This hacking tool may be manually installed by a user.
Information Theft
This hacking tool gathers the following data:
- IP
- Computer name
- Username
- Operating system
- Service pack major version
- Country code
Other Details
This hacking tool does the following:
- Checks for Microsoft .NET version
- Checks if script is being ran under a virtual machine
- Checks for removable drives and drops a copy of .VBS in every folder
- Creates a folder
- Drops installer (.VBS file) in any the following directories:
- %User Temp%
- %Application Data%
- %User Profile%
- %ProgramData%
(Note: %ProgramData% is the Program Data folder, where it usually is C:\Program Files in Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\ProgramData in Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
NOTES:
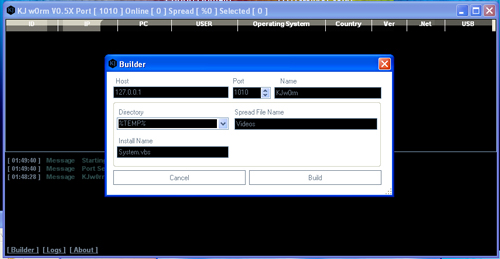
This malware has the following user interface:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as HKTL_KJWORM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

