WORM_DISTTRACK.A
Trojan:Win32/WipMBR.A (Microsoft), W32/DistTrack (McAfee)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm has components that overwrites the affected computer's Master Boot Record (MBR).
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
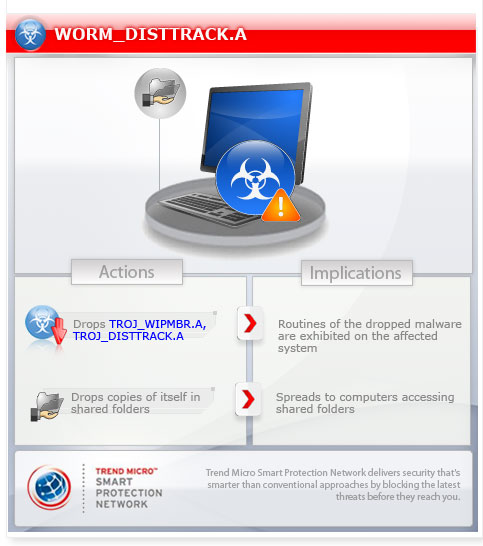
This worm executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
TECHNICAL DETAILS
Arrival Details
This worm may arrive via network shares.
Installation
This worm drops the following copies of itself into the affected system:
- %System%\trksvr.exe
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
Autostart Technique
This worm registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
Type = "10"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
Start = "2"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
ErrorControl = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
ImagePath = "%System\trksvr.exe"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
DisplayName = "Distributed Link Tracking Server"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
DependOnService = "RpcSs"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
DependOnGroup = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
ObjectName = "LocalSystem"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
Description = "Enables the Distributed Link Tracking Client service within the same domain to provide more reliable and efficient maintenance of links within the domain. If this service is disabled, any services that explicitly depend on it will fail to start."
It registers as a system service to ensure its automatic execution at every system startup by adding the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\TrkSvr
Other System Modifications
This worm adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\lanmanworkstation
DependOnService = "TrkSvr"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\lanmanworkstation
DependOnGroup = "0"
Propagation
This worm drops copies of itself in the following shared folders:
- \\{IP address}\ADMIN$\system32\{random file name}.exe
- \\{IP address}\C$\WINDOWS\system32\{random file name}.exe
- \\{IP address}\D$\WINDOWS\system32\{random file name}.exe
- \\{IP address}\E$\WINDOWS\system32\{random file name}.exe
Dropping Routine
This worm drops the following files:
- %System%\{random file name}.exe - detected by Trend Micro as TROJ_WIPMBR.A
- %System%\netinit.exe - detected by Trend Micro as TROJ_DISTTRACK.A
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
It executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
NOTES:
If command-line parameters are specified, this worm drops copies of itself to the following:
- \\{command-line parameter}\ADMIN$\system32\{random file name}.exe
- \\{command-line parameter}\C$\WINDOWS\system32\{random file name}.exe
- \\{command-line parameter}\D$\WINDOWS\system32\{random file name}.exe
- \\{command-line parameter}\E$\WINDOWS\system32\{random file name}.exe
{random file name} is randomly selected from the following:
- caclsrv
- certutl
- clean
- ctrl
- dfrag
- dnslookup
- dvdquery
- event
- extract
- findfile
- fsutl
- gpget
- iissrv
- ipsecure
- msinit
- netx
- ntdsutl
- ntfrsutil
- ntnw
- power
- rdsadmin
- regsys
- routeman
- rrasrv
- sacses
- sfmsc
- sigver
- smbinit
- wcscript
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Remove malware/grayware files dropped/downloaded by WORM_DISTTRACK.A
Step 3
Restart in Safe Mode
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- TrkSvr
- TrkSvr
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\lanmanworkstation
- DependOnService = "TrkSvr"
- DependOnService = "TrkSvr"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\lanmanworkstation
- DependOnGroup = "0"
- DependOnGroup = "0"
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_DISTTRACK.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


