TROJ_CRYPCTB.PE
Troj/Ransom-ARD (Sophos); Luhe.Fiha.A (AVG); UDS:DangerousObject.Multi.Generic (Kaspersky); Trojan.ZBAgent.NS (Malwarebytes); Trojan.Win32.Generic.pak!cobra (VIPRE)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following copies of itself into the affected system and executes them:
- %User Temp%\{random filename}.exe
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It drops the following files:
- %Application Data%\AAMC-10-KeyBio.pdf
- %ProgramData%\{randomly selected folder}\{random filename} (for Windows Vista and above) - private key
- %All Users Profile%\Application Data\{randomly selected folder}\{random filename} (for Windows XP and below) - private key
- %All Users profile%\{random filename}.html (for Windows Vista and above) - contains ransom note and list of encrypted files
- %ProgramData%\{random filename}.html (for Windows Vista and above) - contains ransom note and list of encrypted files
- %All Users Profile%\Application Data\{random filename}.html (for Windows XP and below) - contains ransom note and list of encrypted files
- %User Profile%\Documents\!Decrypt-All-Files-{random letters}.bmp (for Windows Vista and above) - wallpaper
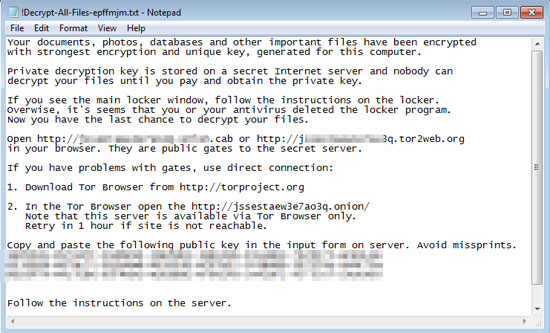
- %User Profile%\Documents\!Decrypt-All-Files-{random letters}.txt (for Windows Vista and above) - ransom note in .txt file
- %User Profile%\My Documents\!Decrypt-All-Files-{random letters}.bmp (for Windows XP and below) - wallpaper
- %User Profile%\My Documents\!Decrypt-All-Files-{random letters}.txt (for Windows XP and below) - ransom note in .txt file
(Note: %Application Data% is the Application Data folder, where it usually is C:\Documents and Settings\{user name}\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Roaming on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %ProgramData% is the Program Data folder, where it usually is C:\Program Files in Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\ProgramData in Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %All Users Profile% is the All Users folder, where it usually is C:\Documents and Settings\All Users on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\ProgramData on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
Autostart Technique
This Trojan drops the following files:
- %System%\Tasks\{random filename} (for Windows Vista and above)
- %Windows%\Tasks\{random filename}.job (for Windows XP and below)
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.)
Other System Modifications
This Trojan changes the desktop wallpaper by modifying the following registry entries:
HKEY_CURRENT_USER\Control Panel\Desktop
WallpaperStyle = "0"
(Note: The default value data of the said registry entry is {user-defined}.)
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = "%User Profile%\{Documents or My Documents}\!Decrypt-All-Files-{random letters}.bmp"
(Note: The default value data of the said registry entry is {user-defined}.)
Other Details
This Trojan connects to the following possibly malicious URL:
- {BLOCKED}vfnw4wp4.tor2web.blutmagie.de
- {BLOCKED}bmvfnw4wp4.onion.gq
- {BLOCKED}mvfnw4wp4.onion.lt
- {BLOCKED}mvfnw4wp4.tor2web.org
- {BLOCKED}aew3e7ao3q.tor2web.org
- {BLOCKED}w3e7ao3q.onion.cab
NOTES:
The dropped !Decrypt-All-Files-{random letters}.txt contains the following ransom message:
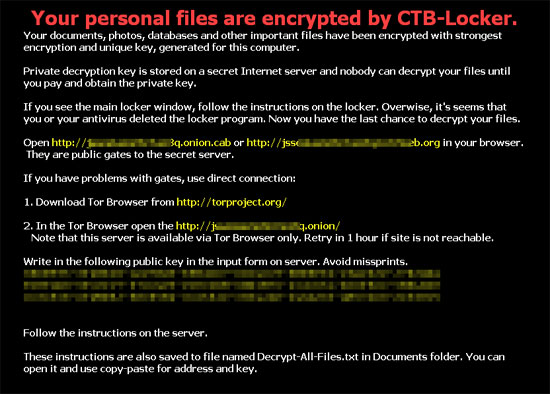
It sets the system's desktop wallpaper to the following image: