BKDR_FLAMER.SMA
Trojan:Win32/MiniFlame.A (Microsoft), Win32/MiniFlame.A trojan (Eset), Backdoor.Win32.MiniFlame (Ikarus)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Dubbed as "Mini Flame", this backdoor has similarities to popular malware families such as PLUGX and POISONIVY, which are linked to targeted attacks.
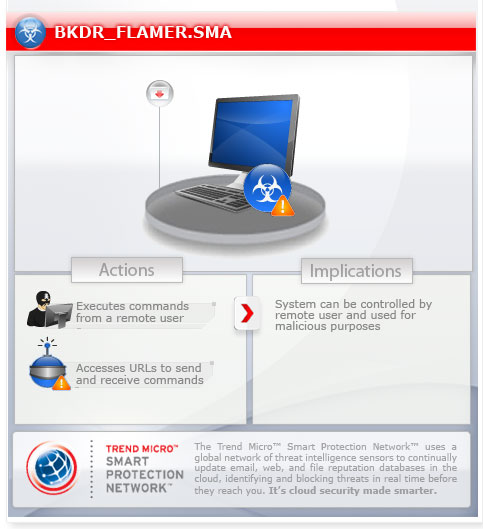
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system.
It creates an event.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This backdoor drops the following files:
- {All Users' Profiles}\datFE2B.da1
- {All Users' Profiles}\mstlis.log
- {All Users' Profiles}\Wnm.tmp
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Global\ShlZoneDataMutex
- Global\ShlZoneSynchMutex
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Download File
- Upload File
- Create process
- Load modules
- Manage Registry
- Invoke sleep command
It connects to the following URL(s) to send and receive commands from a remote malicious user:
- cache.{BLOCKED}s.info/cgi-bin/feed.cgi
- cache.{BLOCKED}s.info/cgi-bin/feed.cgi
- web.{BLOCKED}ycache.com/cgi-bin/feed.cgi
- web.{BLOCKED}lash.info/cgi-bin/feed.cgi
- webapp.{BLOCKED}tp.com/cgi-bin/feed.cgi
- webupdate.{BLOCKED}o.org/cgi-bin/feed.cgi
- {BLOCKED}.{BLOCKED}.49.203
- cache.{BLOCKED}s.info/cgi-bin/feed.cgi
- web.{BLOCKED}ycache.com/cgi-bin/feed.cgi
Other Details
This backdoor connects to the following URL(s) to check for an Internet connection:
- www.google.com
It creates the following event(s):
- Global\AdvTW32AutoDetect
- Global\AdvTW32Ready400WfEvent
- Global\AdvTW32SyncEvent
- Global\EPOAgentEvent
- Global\ShellTRPInitEvent
- Global\TRStepEvent
- Global\TUSEvent
NOTES:
This backdoor searches for a running process named OUTPOST.EXE and exits when found. It also renames the file icsvnt32a.ocx to icsvnt32.ocx.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Restart in Safe Mode
Step 3
Search and delete these files
- {All Users' Profiles}\Wnm.tmp
- {All Users' Profiles}\datFE2B.da1
- {All Users' Profiles}\mstlis.log
- icsvnt32.ocx
Step 4
Restart in normal mode and scan your computer with your Trend Micro product for files detected as BKDR_FLAMER.SMA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


