RANSOM_AIRACROP.F
Ransom:Win32/Haknata.A!rsm (Microsoft) ; Trojan.Win32.Deshacop.gik (Kaspersky)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
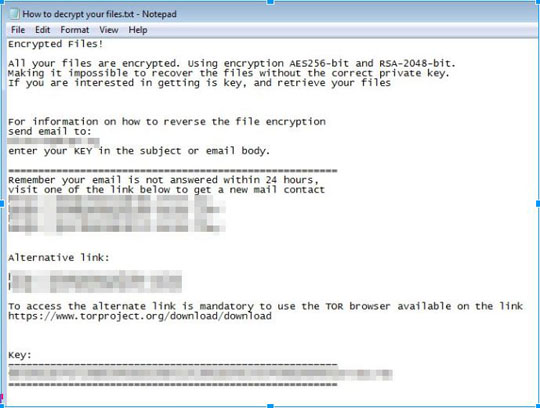
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
NMoreira service = {malware directory}\{malware filename}.exe eusoudejesus
Other Details
This Ransomware does the following:
- It encrypts files in the following locations:
- Fixed Drives
- Network Drives
- Removable Drives
- Shared Folders
- it stops or disables certain services and Windows components by executing the following commands:
- Cmd.exe /c WMIC SERVICE WHERE 'caption LIKE '%Firebird%' OR caption LIKE '%MSSQL%' OR caption LIKE '%SQL%' OR caption LIKE '%Exchange%' OR caption LIKE '%wsbex%' OR caption LIKE '%postgresql%' OR caption LIKE '%BACKP%' OR caption LIKE '%tomcat%'' CALL STOPSERVICE
- Cmd.exe /c WMIC SERVICE WHERE 'caption LIKE '%Firebird%' OR caption LIKE '%MSSQL%' OR caption LIKE '%SQL%' OR caption LIKE '%Exchange%' OR caption LIKE '%wsbex%' OR caption LIKE '%postgresql%' OR caption LIKE '%BACKP%' OR caption LIKE '%tomcat%'' CALL ChangeStartMode 'Disabled'
- Cmd.exe /c sc config FirebirdServerDefaultInstance start= disabled
- Cmd.exe /c taskkill /IM fb_inet_server.exe /F
- Cmd.exe /c net stop FirebirdServerDefaultInstance
- Cmd.exe /c taskkill /IM sqlservr.exe /F
- Cmd.exe /c sc config MSSQLSERVER start= disabled
- Cmd.exe /c sc config MSSQL$SQLEXPRESS start= disabled
- Cmd.exe /c net stop MSSQLSERVER
- Cmd.exe /c net stop MSSQL$SQLEXPRESS
- Cmd.exe /c taskkill /IM pg_ctl.exe /F
- Cmd.exe /c sc config postgresql-9.0 start= disabled
- Cmd.exe /c net stop postgresql-9.0
- Cmd.exe /c sc config MSExchangeAB start= disabled
- Cmd.exe /c sc config MSExchangeAntispamUpdate start= disabled
- Cmd.exe /c sc config MSExchangeEdgeSync start= disabled
- Cmd.exe /c sc config MSExchangeFDS start= disabled
- Cmd.exe /c sc config MSExchangeFBA start= disabled
- Cmd.exe /c sc config MSExchangeImap4 start= disabled
- Cmd.exe /c sc config MSExchangeIS start= disabled
- Cmd.exe /c sc config MSExchangeMailSubmission start= disabled
- Cmd.exe /c sc config MSExchangeMailboxAssistants start= disabled
- Cmd.exe /c sc config MSExchangeMailboxReplication start= disabled
- Cmd.exe /c sc config MSExchangeMonitoring start= disabled
- Cmd.exe /c sc config MSExchangePop3 start= disabled
- Cmd.exe /c sc config MSExchangeProtectedServiceHost start= disabled
- Cmd.exe /c sc config MSExchangeRepl start= disabled
- Cmd.exe /c sc config MSExchangeRPC start= disabled
- Cmd.exe /c sc config MSExchangeSearch start= disabled
- Cmd.exe /c sc config wsbexchange start= disabled
- Cmd.exe /c sc config MSExchangeServiceHost start= disabled
- Cmd.exe /c sc config MSExchangeSA start= disabled
- Cmd.exe /c sc config MSExchangeThrottling start= disabled
- Cmd.exe /c sc config MSExchangeTransport start= disabled
- Cmd.exe /c sc config MSExchangeTransportLogSearch start= disabled
- Cmd.exe /c sc config MSExchangeADTopology start= disabled
- Cmd.exe /c net stop MSExchangeAB
- Cmd.exe /c net stop MSExchangeAntispamUpdate
- Cmd.exe /c net stop MSExchangeEdgeSync
- Cmd.exe /c net stop MSExchangeFDS
- Cmd.exe /c net stop MSExchangeFBA
- Cmd.exe /c net stop MSExchangeImap4
- Cmd.exe /c net stop MSExchangeIS
- Cmd.exe /c net stop MSExchangeMailSubmission
- Cmd.exe /c net stop MSExchangeMailboxAssistants
- Cmd.exe /c net stop MSExchangeMailboxReplication
- Cmd.exe /c net stop MSExchangeMonitoring
- Cmd.exe /c net stop MSExchangePop3
- Cmd.exe /c net stop MSExchangeProtectedServiceHost
- Cmd.exe /c net stop MSExchangeRepl
- Cmd.exe /c net stop MSExchangeRPC
- Cmd.exe /c net stop MSExchangeSearch
- Cmd.exe /c net stop wsbexchange
- Cmd.exe /c net stop MSExchangeServiceHost
- Cmd.exe /c net stop MSExchangeSA
- Cmd.exe /c net stop MSExchangeThrottling
- Cmd.exe /c net stop MSExchangeTransport
- Cmd.exe /c net stop MSExchangeTransportLogSearch
- Cmd.exe /c net stop MSExchangeADTopology
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- ntldr
- .exe
- .dll
- .lnk
- .bat
- .ini
- .msi
- .scf
- NTUSER.DAT
- CONFIG.SYS
- IO.SYS
- MSDOS.SYS
- NTDETECT.COM
- pagefile.sys
It avoids encrypting files with the following strings in their file path:
- Windows Sidebar
- AVG
- DVD Maker
- Microsoft Games
- Windows NT
- Reference Assemblies
- Windows Defender
- Windows Journal
- PerfLogs
- Windows Photo Viewer
- Microsoft.NET
- $Recycle.Bin
- Windows Mail
- Windows Media Player
- java
- Internet Explorer
- TeamViewer
- windows
- Windows
- ESET
- Common Files
- AVIRA
- intel
- AVAST Software
- FileZilla
- Atheros
- Cobian
- Backup
- K-Lite Codec Pack
- ProgramData
- AppData
- winrar
- firebird
- Microsoft SDKs
- Notepad++
- Microsoft Silverlight
- Realtek
- Microsoft SQL Server Compact Edition
- Microsoft Visual Studio
- bootmgr
- boot
It appends the following extension to the file name of the encrypted files:
- .__AiraCropEncrypted!
It drops the following file(s) as ransom note:
- {Encrypted directory}\How to decrypt your files.txt
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Identify and terminate files detected as RANSOM_AIRACROP.F
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- NMoreira service = "{Malicious directory}\{malicious filename}.exe eusoudejesus"
- NMoreira service = "{Malicious directory}\{malicious filename}.exe eusoudejesus"
Step 5
Search and delete these files
- {Encrypted directory}\How to decrypt your files.txt
Step 6
Scan your computer with your Trend Micro product to delete files detected as RANSOM_AIRACROP.F. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 7
Restore encrypted files from backup.
NOTES:
Before doing the last step, do the following:
Restoring Affected Services to Enable Automatic Execution During Startup
- Run the command prompt (cmd.exe) as administrator.
- Change startup type of service to automatic by typing the following commands:
sc config {service} start= auto
Note: Refer to the disabled services above (sc config {service} start= disabled)
And
WMIC SERVICE WHERE "caption LIKE '%Firebird%' OR caption LIKE '%MSSQL%' OR caption LIKE '%SQL%' OR caption LIKE '%Exchange%' OR caption LIKE '%wsbex%' OR caption LIKE '%postgresql%' OR caption LIKE '%BACKP%' OR caption LIKE '%tomcat%''' CALL ChangeStartMode 'Automatic'
Enabling Volume Shadow Service
- Run the command prompt (cmd.exe) as administrator.
- Enable Volume Shadow Service by typing the following command: net start vss
After following these instructions, please restart in normal mode in order to resume normal operations for the affected services.
Did this description help? Tell us how we did.


