Ransomware Recap: Is Redboot Really a Wiper?
 The ransomware known as Redboot (detected by Trend Micro as RANSOM_REDBOOT.A) leaves victims little hope of recovery as early analysis shows that, along with file encryption, it also alters the master boot record (MBR) and repartitions the hard drive. Because of its ability to cause irreversible damage, Redboot could be classified as a wiper rather than a ransomware. However, news sources say that the authors have confirmed the ransomware is still being developed and will be released in October.
The ransomware known as Redboot (detected by Trend Micro as RANSOM_REDBOOT.A) leaves victims little hope of recovery as early analysis shows that, along with file encryption, it also alters the master boot record (MBR) and repartitions the hard drive. Because of its ability to cause irreversible damage, Redboot could be classified as a wiper rather than a ransomware. However, news sources say that the authors have confirmed the ransomware is still being developed and will be released in October.
Redboot is a compiled AutoIT executable that will extract five files (assembler.exe, boot.asm, main.exe, overwrite.exe, and protect.exe) into the directory where the launcher was executed. Using these files, it will overwrite the computer’s current master boot record, scan and encrypt files, and also block system tools (like Task Manager) used to help analyze and stop infection. With no distinct way to restore the MBR or the partition, victims of this ransomware are likely to lose their data.
Locky campaigns ramped up
We observed Locky being pushed alongside FAKEGLOBE in a recent spam campaign, opening up the possibility of a victim being infected with two kinds of ransomware from one source. But a larger spam campaign was also detected targeting millions of users. The campaign uses different kinds of spam mail, some from companies sending invoices and others with more generic senders and unidentified attachments.
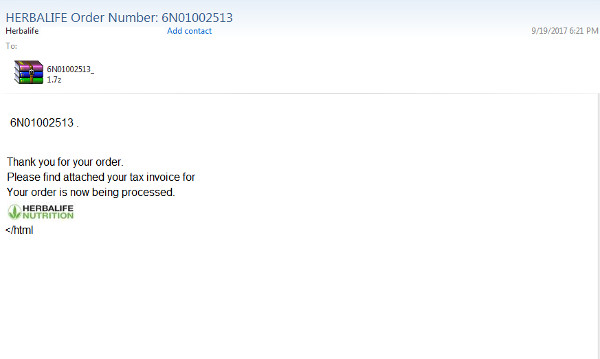
Figure 1. A spam email impersonating the Herbalife organization
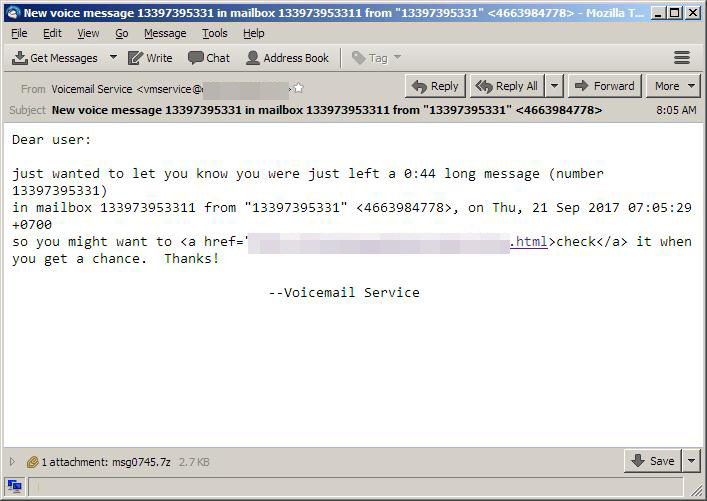
Figure 2. General spam mail supposedly from a voicemail service
The attacks were scattered across the globe, but according to the Trend Micro Smart Protection Network (SPN), the prime targets were India and Chile. On September 18, a variant of Locky started using .yckol ("locky" reversed) as an extension for encrypted files. Their ransom also went down to .25 Bitcoin (around US$1,000), possibly because of the rising value of BTC.
New ransomware still being developed and updated
Bad guys are updating existing ransomware variants and developing new families. SamSam, a crypto-ransomware that we last saw in July, has a new variant that now appends .myransext2017 to the files it encrypts. The CypherPy ransomware (detected by Trend Micro as RANSOM_CYPHERPY) and BlackMist (detected by Trend Micro as RANSOM_BLACKMIST) are two new families that have been recently spotted. InfinityLock (detected by Trend Micro as RANSOM_INFINITYLOCK) is a new family as well, with a gimmick that shows the hacker supposedly encrypting the victim’s files in “real time”.
Meanwhile, Sapnupuas (detected by Trend Micro as RANSOM_SAPNUPUAS and also called nRansom) is a particularly contentious ransomware that is not after ransom money but asks for nude photos instead. Recently the ransomware developers made even more outlandish demands, asking victims to murder ten people and send them a video.
Ransomware will continue to spread, and developers are expected to keep developing their tools and aim at new targets. To defend against the steady tide of evolving ransomware variants, enterprises and users should stay alert and invest in multilayered security solutions.
Trend Micro Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
End users and enterprises can also benefit from multilayered mobile security solutions such as Trend Micro™ Mobile Security for Android™ (available on Google Play), and Trend Micro™ Mobile Security for Apple devices (available on the App Store). Trend Micro™ Mobile Security for Enterprise provide device, compliance and application management, data protection, and configuration provisioning, as well as protect devices from attacks that leverage vulnerabilities, preventing unauthorized access to apps, as well as detecting and blocking malware and fraudulent websites.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One