Ransom.MSIL.TARGETCOMP.YXCCUTT
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following folders:
- %Application Data%\Aabza
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops and executes the following files:
- %User Temp%\Dwghpjxmueqxokshkill$.bat - contains commands to delete services and terminate processes
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following copies of itself into the affected system:
- %Application Data%\Aabza\Qawjvy.exe
- %Windows%\avast.exe
- {IP Address}\admin$\avast.exe
- {IP Address}\c$\avast.exe
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.)
It adds the following processes:
- %Windows%\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe
- %System%\cmd.exe /c timeout 10
- reg delete HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Command Processor /v AutoRun /f
- takeown /f %SystemRoot%\{system32|SysWOW64}\{String} /a
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /g Administrators:f
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /g Users:r
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /g Administrators:r
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /d SERVICE
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /d mssqlserver
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /d network service
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /g system:r
- cacls %SystemRoot%\{system32|SysWOW64}\{String} /e /d mssql$sqlexpress
where {String}:- cmd.exe
- net.exe
- net1.exe
- mshta.exe
- FTP.exe
- wscript.exe
- cscript.exe
- WindowsPowerShell\v1.0\powershell.exe
- takeown /f C:\ProgramData /a
- takeown /f C:\Users\Public /a
- cacls C:\ProgramData /g Administrators:f
- cacls C:\ProgramData /e /g Users:r
- cacls C:\ProgramData /e /g Administrators:r
- cacls C:\ProgramData /e /d SERVICE
- cacls C:\ProgramData /e /d mssqlserver
- cacls C:\ProgramData /e /d network service
- cacls C:\ProgramData /e /d system
- cacls C:\ProgramData /e /d mssql$sqlexpress
- cacls C:\Users\Public /g Administrators:f
- cacls C:\Users\Public /e /g Users:r
- cacls C:\Users\Public /e /g Administrators:r
- cacls C:\Users\Public /e /d SERVICE
- cacls C:\Users\Public /e /d mssqlserver
- cacls C:\Users\Public /e /d network service
- cacls C:\Users\Public /e /d system
- cacls C:\Users\Public /e /d mssql$sqlexpress
- vssadmin delete shadows /all /quiet
- cmd.exe /c bcdedit /set {current} bootstatuspolicy ignoreallfailures
- cmd.exe /c bcdedit /set {current} recoveryenabled no
- sc delete {Services deleted}
- net stop {Services stopped}
- taskkill /IM {Process List} /F /T
(Note: %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
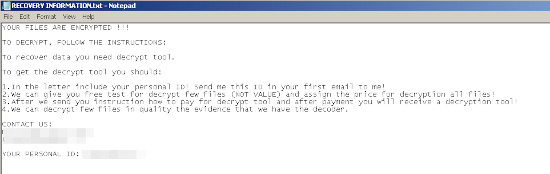
It leaves text files that serve as ransom notes containing the following:
- C:\HOW TO RECOVER !!.TXT
- {Encrypted Directory}\RECOVERY INFORMATION.txt
It injects codes into the following process(es):
- %Windows%\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe
(Note: %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.)
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Qawjvy = %Application Data%\Aabza\Qawjvy.exe
Other System Modifications
This Ransomware deletes the following registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Raccine
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\EventLog\Application\
Raccine
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
vssadmin.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
wmic.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
wbadmin.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
bcdedit.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
powershell.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
diskshadow.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
net.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
taskkill.exe
Process Termination
This Ransomware terminates the following processes if found running in the affected system's memory:
- where {Process List}:
- sqlservr.exe
- httpd.exe
- java.exe
- fdhost.exe
- fdlauncher.exe
- reportingservicesservice.exe
- softmgrlite.exe
- sqlbrowser.exe
- ssms.exe
- vmtoolsd.exe
- baidunetdisk.exe
- yundetectservice.exe
- ssclient.exe
- GNAupdaemon.exe
- RAVCp164.exe
- igfxEM.exe
- igfxHK.exe
- igfxTray.exe
- 360bdoctor.exe
- GNCEFExternal.exe
- PrivacyIconClient.exe
- UIODetect.exe
- AutoDealService.exe
- IDDAService.exe
- EnergyDataService.exe
- MPService.exe
- TransMain.exe
- DAService.exe
- GoogleCrashHandler.exe
- GoogleCrashHandler64.exe
- GoogleUpdate.exe
- cohernece.exe
- vmware-tray.exe
- MsDtsSrvr.exe
- msmdsrv.exe
- FileZilla server.exe
- UpdateData.exe
- WebApi.Host.exe
- VGAuthService.exe
- omtsreco.exe
- TNSLSNR.exe
- oracle.exe
- msdtc.exe
- mmc.exe
- emagent.exe
- SoftMgrLite.exe
- Admin.exe
- EnterprisePortal.exe
- tomcat7.exe
- Kingdee.K3.CRM.MMC.MMCService.exe
- Kingdee.k3.Weixin.ClientService.exe
- Kingdee.K3.PUBLIC.BkgSvcHost.exe
- Kingdee.K3.HR.Server.exe
- Kingdee.K3.PUBLIC.KDSvrMgrHost.exe
- tomcat5.exe
- Kingdee.DeskTool.exe
- UserClient.exe
- mysqld.exe
- ImtsEventSvr.exe
- mysqld-nt.exe
- 360EnterpriseDiskUI.exe
- tomcat8.exe
- QQprotect.exe
- isqlplussvc.exe
- nmesrvc.exe
- jusched.exe
- MtxHotPlugService.exe
- jucheck.exe
- wordpad.exe
- SecureCRT.exe
- chrome.exe
- Thunder.exe
- ThunderPlatform.exe
- iexplore.exe
- vm-agent.exe
- vm-agent-daemon.exe
- eSightService.exe
- cygrunsrv.exe
- wrapper.exe
- nginx.exe
- node.exe
- sshd.exe
- vm-tray.exe
- iempwatchdog.exe
- sqlwriter.exe
- php.exe
- notepad++.exe
- phpStudy.exe
- OPCClient.exe
- navicat.exe
- SupportAssistAgent.exe
- SunloginClient.exe
- SOUNDMAN.exe
- WeChat.exe
- TXPlatform.exe
- Tencentdll.exe
- jenkins.exe
- QQ.exe
- HaoZip.exe
- HaoZipScan.exe
- TSVNCache.exe
- RAVCpl64.exe
- secbizsrv.exe
- aliwssv.exe
- Helper_Haozip.exe
- acrotray.exe
- FileZilla Server Interface.exe
- YoudaoNote.exe
- YNoteCefRender.exe
- idea.exe
- fsnotifier.exe
- picpick.exe
- lantern.exe
- sysproxy-cmd.exe
- service.exe
- pcas.exe
- PresentationFontCache.exe
- RtWlan.exe
- monitor.exe
- Correspond.exe
- ChatServer.exe
- InetMgr.exe
- LogonServer.exe
- GameServer.exe
- ServUAdmin.exe
- ServUDaemon.exe
- update0.exe
- server.exe
- w3wp.exe
- notepad.exe
- PalmInputService.exe
- PalmInputGuard.exe
- UpdateServer.exe
- UpdateGate.exe
- DBServer.exe
- LoginGate.exe
- SelGate.exe
- RunGate.exe
- M2Server.exe
- LogDataServer.exe
- LoginSrv.exe
- sqlceip.exe
- mqsvc.exe
- RefundOrder.exe
- ClamTray.exe
- AdobeARM.exe
- veeam.backup.shell.exe
- VpxClient.exe
- vmware-vmrc.exe
- DSCPatchService.exe
- scktsrvr.exe
- ServerManager.exe
- Dispatcher.exe
- EFDispatcher.exe
- ClamWin.exe
- srvany.exe
- JT_AG-8332.exe
- XXTClient.exe
- clean.exe
- Net.Service.exe
- plsqldev.exe
- splwow64.exe
- Oobe.exe
- QQYService.exe
- SGTool.exe
- postgres.exe
- AppVShNotify.exe
- OfficeClickToRun.exe
- EntDT.exe
- EntPublish.exe
- pg_ctl.exe
- rcrelay.exe
- SogouImeBroker.exe
- CCenter.exe
- ScanFrm.exe
- d_manage.exe
- RsTray.exe
- wampmanager.exe
- RavTray.exe
- mssearch.exe
- sqlmangr.exe
- msftesql.exe
- SyncBaseSvr.exe
- SyncBaseConsole.exe
- aspnet_state.exe
- AutoBackUpEx.exe
- redis-server.exe
- MySQLNotifier.exe
- oravssw.exe
- fppdis5.exe
- His6Service.exe
- dinotify.exe
- JhTask.exe
- Executer.exe
- AllPassCBHost.exe
- ap_nginx.exe
- AndroidServer.exe
- XT.exe
- XTService.exe
- AllPassMCService.exe
- IMEDICTUPDATE.exe
- FlashHelperService.exe
- ap_redis-server.exe
- UtilDev.WebServer.Monitor.exe
- UWS.AppHost.Clr2.x86.exe
- FoxitProtect.exe
- ftnlses.exe
- ftusbrdwks.exe
- ftusbrdsrv.exe
- ftnlsv.exe
- Syslogd_Service.exe
- UWS.HighPrivilegeUtilities.exe
- ftusbsrv.exe
- UWS.LowPrivilegeUtilities.exe
- UWS.AppHost.Clr2.AnyCpu.exe
- winguard_x64.exe
- vmconnect.exe
- firefox.exe
- usbrdsrv.exe
- usbserver.exe
- Foxmail.exe
- qemu-ga.exe
- wwbizsrv.exe
- ZTEFileTranS.exe
- ZTEUsbIpc.exe
- ZTEUsbIpcGuard.exe
- AlibabaProtect.exe
- kbasesrv.exe
- ZTEVdservice.exe
- MMRHookService.exe
- extjob.exe
- IpOverUsbSvc.exe
- VMwareTray.exe
- devenv.exe
- PerfWatson2.exe
- ServiceHub.Host.Node.x86.exe
- ServiceHub.IdentityHost.exe
- ServiceHub.VSDetouredHost.exe
- ServiceHub.SettingsHost.exe
- ServiceHub.Host.CLR.x86.exe
- ServiceHub.RoslynCodeAnalysisService32.exe
- ServiceHub.DataWarehouseHost.exe
- Microsoft.VisualStudio.Web.Host.exe
- SQLEXPRWT.exe
- setup.exe
- remote.exe
- setup100.exe
- landingpage.exe
- WINWORD.exe
- KuaiYun.exe
- HwsHostPanel.exe
- NovelSpider.exe
- Service_KMS.exe
- WebServer.exe
- ChsIME.exe
- btPanel.exe
- Protect_2345Explorer.exe
- Pic_2345Svc.exe
- vmware-converter-a.exe
- vmware-converter.exe
- vmware.exe
- vmware-unity-helper.exe
- vmware-vmx.exe
- usysdiag.exe
- PopBlock.exe
- gsinterface.exe
- Gemstar.Group.CRS.Client.exe
- TenpayServer.exe
- RemoteExecService.exe
- VS_TrueCorsManager.exe
- ntpsvr-2019-01-22-wgs84.exe
- rtkjob-ion.exe
- ntpsvr-2019-01-22-no-usrcheck.exe
- NtripCaster-2019-01-08.exe
- BACSTray.exe
- protect.exe
- hfs.exe
- jzmis.exe
- NewFileTime_x64.exe
- 2345MiniPage.exe
- JMJ_server.exe
- cacls.exe
- gpsdaemon.exe
- gpsusersvr.exe
- gpsdownsvr.exe
- gpsstoragesvr.exe
- gpsdataprocsvr.exe
- gpsftpd.exe
- gpsmysqld.exe
- gpstomcat6.exe
- gpsloginsvr.exe
- gpsmediasvr.exe
- gpsgatewaysvr.exe
- gpssvrctrl.exe
- zabbix_agentd.exe
- BackupExec.exe
- Att.exe
- mdm.exe
- BackupExecManagementService.exe
- bengine.exe
- benetns.exe
- beserver.exe
- pvlsvr.exe
- bedbg.exe
- beremote.exe
- RemoteAssistProcess.exe
- BarMoniService.exe
- GoodGameSrv.exe
- BarCMService.exe
- TsService.exe
- GoodGame.exe
- BarServerView.exe
- IcafeServicesTray.exe
- BsAgent_0.exe
- ControlServer.exe
- DisklessServer.exe
- DumpServer.exe
- NetDiskServer.exe
- PersonUDisk.exe
- service_agent.exe
- SoftMemory.exe
- BarServer.exe
- RtkNGUI64.exe
- Serv-U-Tray.exe
- QQPCSoftTrayTips.exe
- SohuNews.exe
- Serv-U.exe
- QQPCRTP.exe
- EasyFZS.exe
- HaoYiShi.exe
- HysMySQL.exe
- wtautoreg.exe
- ispiritPro.exe
- CAService.exe
- XAssistant.exe
- TrustCA.exe
- GEUU20003.exe
- CertMgr.exe
- eSafe_monitor.exe
- MainExecute.exe
- FastInvoice.exe
- sesvc.exe
- ScanFileServer.exe
- Nuoadehgcgcd.exe
- OpenFastAssist.exe
- FastInvoiceAssist.exe
- Nuoadfaggcje.exe
- OfficeUpdate.exe
- atkexComSvc.exe
- FileTransferAgent.exe
- MasterReplicatorAgent.exe
- CrmAsyncService.exe
- CrmUnzipService.exe
- NscAuthService.exe
- ReplicaReplicatorAgent.exe
- ASMCUSvc.exe
- OcsAppServerHost.exe
- RtcCdr.exe
- IMMCUSvc.exe
- DataMCUSvc.exe
- MeetingMCUSvc.exe
- QmsSvc.exe
- RTCSrv.exe
- pnopagw.exe
- NscAuth.exe
- Microsoft.ActiveDirectory.WebServices.exe
- DistributedCacheService.exe
- c2wtshost.exe
- Microsoft.Office.Project.Server.Calculation.exe
- schedengine.exe
- Microsoft.Office.Project.Server.Eventing.exe
- Microsoft.Office.Project.Server.Queuing.exe
- WSSADMIN.EXE
- hostcontrollerservice.exe
- noderunner.exe
- OWSTIMER.EXE
- wsstracing.exe
- MySQLInstallerConsole.exe
- EXCEL.EXE
- consent.exe
- RtkAudioService64.exe
- RAVBg64.exe
- FNPLicensingService64.exe
- VisualSVNServer.exe
- MotionBoard57.exe
- MotionBoardRCService57.exe
- LPManService.exe
- RaRegistry.exe
- RaAutoInstSrv.exe
- RtHDVCpl.exe
- DefenderDaemon.exe
- BestSyncApp.exe
- ApUI.exe
- AutoUpdate.exe
- LPManNotifier.exe
- FieldAnalyst.exe
- TimingGenerate.exe
- Detector.exe
- Estimator.exe
- FA_Logwriter.exe
- TrackingSrv.exe
- cbInterface.exe
- ccbService.exe
- U8DispatchService.exe
- dbsrv16.exe
- KICManager.exe
- KICMain.exe
- ServerManagerLauncher.exe
- TbossGate.exe
- iusb3mon.exe
- MgrEnvSvc.exe
- Mysoft.Config.WindowsService.exe
- Mysoft.UpgradeService.UpdateService.exe
- hasplms.exe
- Mysoft.Setup.InstallService.exe
- Mysoft.UpgradeService.Dispatcher.exe
- Mysoft.DataCenterService.WindowsHost.exe
- Mysoft.DataCenterService.DataCleaning.exe
- Mysoft.DataCenterService.DataTracking.exe
- Mysoft.SchedulingService.WindowsHost.exe
- ServiceMonitor.exe
- Mysoft.SchedulingService.ExecuteEngine.exe
- AgentX.exe
- host.exe
- vsjitdebugger.exe
- VBoxSDS.exe
- TeamViewer_Service.exe
- TeamViewer.exe
- CasLicenceServer.exe
- tv_w32.exe
- tv_x64.exe
- rdm.exe
- SecureCRTPortable.exe
- VirtualBox.exe
- VBoxSVC.exe
- VirtualBoxVM.exe
- abs_deployer.exe
- edr_monitor.exe
- sfupdatemgr.exe
- ipc_proxy.exe
- edr_agent.exe
- edr_sec_plan.exe
- sfavsvc.exe
- DataShareBox.ShareBoxMonitorService.exe
- DataShareBox.ShareBoxService.exe
- Jointsky.CloudExchangeService.exe
- Jointsky.CloudExchange.NodeService.ein
- perl.exe
- TsServer.exe
- AppMain.exe
- easservice.exe
- Kingdee6.1.exe
- QyKernel.exe
- QyFragment.exe
- ComputerZTray.exe
- ComputerZService.exe
- ClearCache.exe
- ProLiantMonitor.exe
- bugreport.exe
- GNWebServer.exe
- UI0Detect.exe
- GNCore.exe
- gnwayDDNS.exe
- GNWebHelper.exe
- php-cgi.exe
- ESLUSBService.exe
- CQA.exe
- Kekcoek.pif
- Tinuknx.exe
- servers.exe
- ping.exe
- TianHeng.exe
- K3MobileService.exe
- VSSVC.exe
- Xshell.exe
- XshellCore.exe
- FNPLicensingService.exe
- XYNTService.exe
- EISService.exe
- UFSoft.U8.Framework.EncryptManager.exe
- yonyou.u8.gc.taskmanager.servicebus.exe
- U8KeyManagePool.exe
- U8MPool.exe
- U8SCMPool.exe
- UFIDA.U8.Report.SLReportService.exe
- U8TaskService.exe
- U8TaskWorker.exe
- U8WebPool.exe
- U8AllAuthServer.exe
- UFIDA.U8.UAP.ReportService.exe
- UFIDA.U8.ECE.UTU.Services.exe
- U8WorkerService.exe
- UFIDA.U8.ECE.UTU.exe
- ShellStub.exe
- U8UpLoadTask.exe
- UfSysHostingService.exe
- UFIDA.UBF.SystemManage.ApplicationService.exe
- UFIDA.U9.CS.Collaboration.MailService.exe
- NotificationService.exe
- UBFdevenv.exe
- UFIDA.U9.SystemManage.SystemManagerClient.exe
- mongod.exe
- SpusCss.exe
- UUDesktop.exe
- KDHRServices.exe
- Kingdee.K3.Mobile.Servics.exe
- KDSvrMgrService.exe
- pdfServer.exe
- pdfspeedup.exe
- SufAppServer.exe
- Kingdee.K3.Mobile.LightPushService.exe
- iMTSSvcMgr.exe
- kdmain.exe
- KDActMGr.exe
- K3ServiceUpdater.exe
- Aua.exe
- iNethinkSQLBackup.exe
- auaJW.exe
- Scheduler.exe
- bschJW.exe
- SystemTray64.exe
- OfficeDaemon.exe
- OfficeIndex.exe
- OfficeIm.exe
- iNethinkSQLBackupConsole.exe
- OfficeMail.exe
- OfficeTask.exe
- OfficePOP3.exe
- apache.exe
- GnHostService.exe
- HwUVPUpgrade.exe
- Kingdee.KIS.UESystemSer.exe
- uvpmonitor.exe
- UVPUpgradeService.exe
- KDdataUpdate.exe
- Portal.exe
- U8SMSSrv.exe
- Ufida.T.SM.PublishService.exe
- lta8.exe
- UfSvrMgr.exe
- AutoUpdateService.exe
- MOM.exe
- sqlserv.exe
- oracle.exe
- ntdbsmgr.exe
- sqlservr.exe
- sqlwriter.exe
- MsDtsSrvr.exe
- msmdsrv.exe
- ReportingServecesService.exe
- fdhost.exe
- fdlauncher.exe
- mysql.exe
Other Details
This Ransomware adds and runs the following services:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\avast
ImagePath = %Windows%\avast.exe
It does the following:
- It encrypts fixed drives, removable drives, network drives and shared folders
- It DOES NOT continue to routine if User Default Language ID of the system is any of the following:
- Russian (0x419)
- Kazakh (0x43F)
- Belarusian (0x423)
- Ukrainian (0x422)
- Tatar (0x444)
- It attempts to delete itself through the following process:
- cmd.exe /c ping {BLOCKED}.{BLOCKED}.0.1 && del "{malware path and name}" >> NUL
- It deletes the following services {Services deleted}:
- XT800Service_Personal
- SQLSERVERAGENT
- SQLWriter
- SQLBrowser
- MSSQLFDLauncher
- MSSQLSERVER
- QcSoftService
- MSSQLServerOLAPService
- VMTools
- VGAuthService
- MSDTC
- TeamViewer
- ReportServer
- RabbitMQ
- AHS SERVICE
- Sense Shield Service
- SSMonitorService
- SSSyncService
- TPlusStdAppService1300
- MSSQL$SQL2008
- SQLAgent$SQL2008
- TPlusStdTaskService1300
- TPlusStdUpgradeService1300
- VirboxWebServer
- jhi_service
- LMS
- FontCache3.0.0.0
- OSP Service
- DAService_TCP
- eCard-TTransServer
- eCardMPService
- EnergyDataService
- UI0Detect
- K3MobileService
- TCPIDDAService
- WebAttendServer
- UIODetect
- wanxiao-monitor
- VMAuthdService
- VMUSBArbService
- VMwareHostd
- vm-agent
- VmAgentDaemon
- OpenSSHd
- eSightService
- apachezt
- Jenkins
- secbizsrv
- SQLTELEMETRY
- MSMQ
- smtpsvrJT
- zyb_sync
- 360EntHttpServer
- 360EntSvc
- 360EntClientSvc
- NFWebServer
- wampapache
- MSSEARCH
- msftesql
- SyncBASE Service
- OracleDBConcoleorcl
- OracleJobSchedulerORCL
- OracleMTSRecoveryService
- OracleOraDb11g_home1ClrAgent
- OracleOraDb11g_home1TNSListener
- OracleVssWriterORCL
- OracleServiceORCL
- aspnet_state
- Redis
- JhTask
- ImeDictUpdateService
- MCService
- allpass_redisservice_port21160
- Flash Helper Service
- Kiwi Syslog Server
- UWS HiPriv Services
- UWS LoPriv Services
- ftnlsv3
- ftnlses3
- FxService
- UtilDev Web Server Pro
- ftusbrdwks
- ftusbrdsrv
- ZTE USBIP Client Guard
- ZTE USBIP Client
- ZTE FileTranS
- wwbizsrv
- qemu-ga
- AlibabaProtect
- ZTEVdservice
- kbasesrv
- MMRHookService
- IpOverUsbSvc
- MsDtsServer100
- KuaiYunTools
- KMSELDI
- btPanel
- Protect_2345Explorer
- 2345PicSvc
- vmware-converter-agent
- vmware-converter-server
- vmware-converter-worker
- QQCertificateService
- OracleRemExecService
- GPSDaemon
- GPSUserSvr
- GPSDownSvr
- GPSStorageSvr
- GPSDataProcSvr
- GPSGatewaySvr
- GPSMediaSvr
- GPSLoginSvr
- GPSTomcat6
- GPSMysqld
- GPSFtpd
- Zabbix Agent
- BackupExecAgentAccelerator
- bedbg
- BackupExecDeviceMediaService
- BackupExecRPCService
- BackupExecAgentBrowser
- BackupExecJobEngine
- BackupExecManagementService
- MDM
- TxQBService
- Gailun_Downloader
- RemoteAssistService
- YunService
- Serv-U
- EasyFZS Server
- Rpc Monitor
- OpenFastAssist
- Nuo Update Monitor
- Daemon Service
- asComSvc
- OfficeUpdateService
- RtcSrv
- RTCASMCU
- FTA
- MASTER
- NscAuthService
- MSCRMUnzipService
- MSCRMAsyncService$maintenance
- MSCRMAsyncService
- REPLICA
- RTCATS
- RTCAVMCU
- RtcQms
- RTCMEETINGMCU
- RTCIMMCU
- RTCDATAMCU
- RTCCDR
- ProjectEventService16
- ProjectQueueService16
- SPAdminV4
- SPSearchHostController
- SPTimerV4
- SPTraceV4
- OSearch16
- ProjectCalcService16
- c2wts
- AppFabricCachingService
- ADWS
- MotionBoard57
- MotionBoardRCService57
- vsvnjobsvc
- VisualSVNServer
- FlexNet Licensing Service 64
- BestSyncSvc
- LPManager
- MediatekRegistryWriter
- RaAutoInstSrv_RT2870
- CobianBackup10
- SQLANYs_sem5
- CASLicenceServer
- SQLService
- semwebsrv
- TbossSystem
- ErpEnvSvc
- Mysoft.Autoupgrade.DispatchService
- Mysoft.Autoupgrade.UpdateService
- Mysoft.Config.WindowsService
- Mysoft.DataCenterService
- Mysoft.SchedulingService
- Mysoft.Setup.InstallService
- MysoftUpdate
- edr_monitor
- abs_deployer
- savsvc
- ShareBoxMonitorService
- ShareBoxService
- CloudExchangeService
- U8WorkerService2
- CIS
- EASService
- KICkSvr
- OSP Service
- U8SmsSrv
- OfficeClearCache
- TurboCRM70
- U8DispatchService
- U8EISService
- U8EncryptService
- U8GCService
- U8KeyManagePool
- U8MPool
- U8SCMPool
- U8SLReportService
- U8TaskService
- U8WebPool
- UFAllNet
- UFReportService
- UTUService
- U8WorkerService1
- It stops the following services {Services stopped}:
- U8WorkerService1
- U8WorkerService2
- memcached Server
- Apache2.4
- UFIDAWebService
- MSComplianceAudit
- MSExchangeADTopology
- MSExchangeAntispamUpdate
- MSExchangeCompliance
- MSExchangeDagMgmt
- MSExchangeDelivery
- MSExchangeDiagnostics
- MSExchangeEdgeSync
- MSExchangeFastSearch
- MSExchangeFrontEndTransport
- MSExchangeHM
- MSSQL$SQL2008
- MSExchangeHMRecovery
- MSExchangeImap4
- MSExchangeIMAP4BE
- MSExchangeIS
- MSExchangeMailboxAssistants
- MSExchangeMailboxReplication
- MSExchangeNotificationsBroker
- MSExchangePop3
- MSExchangePOP3BE
- MSExchangeRepl
- MSExchangeRPC
- MSExchangeServiceHost
- MSExchangeSubmission
- MSExchangeThrottling
- MSExchangeTransport
- MSExchangeTransportLogSearch
- MSExchangeUM
- MSExchangeUMCR
- MySQL5_OA
- HaoZipSvc
- igfxCUIService2.0.0.0
- Realtek11nSU
- xenlite
- XenSvc
- Apache2.2
- Synology Drive VSS Service x64
- DellDRLogSvc
- FirebirdGuardianDeafaultInstance
- JWEM3DBAUTORun
- JWRinfoClientService
- JWService
- Service2
- RapidRecoveryAgent
- FirebirdServerDefaultInstance
- AdobeARMservice
- VeeamCatalogSvc
- VeeanBackupSvc
- VeeamTransportSvc
- TPlusStdAppService1300
- TPlusStdTaskService1300
- TPlusStdUpgradeService1300
- TPlusStdWebService1300
- VeeamNFSSvc
- VeeamDeploySvc
- VeeamCloudSvc
- VeeamMountSvc
- VeeamBrokerSvc
- VeeamDistributionSvc
- tmlisten
- ServiceMid
- 360EntPGSvc
- ClickToRunSvc
- RavTask
- AngelOfDeath
- d_safe
- NFLicenceServer
- NetVault Process Manager
- RavService
- DFServ
- IngressMgr
- EvtSys
- K3ClouManager
- NFVPrintServer
- RTCAVMCU
- CobianBackup10
- GNWebService
- Mysoft.SchedulingService
- AgentX
- SentinelKeysServer
- DGPNPSEV
- TurboCRM70
- NFSysService
- U8DispatchService
- NFOTPService
- U8EISService
- U8EncryptService
- U8GCService
- U8KeyManagePool
- U8MPool
- U8SCMPool
- U8SLReportService
- U8TaskService
- U8WebPool
- UFAllNet
- UFReportService
- UTUService
- UIODetect
- VMwareHostd
- TeamViewer8
- VMUSBArbService
- VMAuthdService
- wanxiao-monitor
- WebAttendServer
- mysqltransport
- VMnetDHCP
- VMware NAT Service
- Tomcat8
- TeamViewer
- QPCore
- CASLicenceServer
- CASWebServer
- AutoUpdateService
- Alibaba Security Aegis Detect Service
- Alibaba Security Aegis Update Service
- AliyunService
- CASXMLService
- AGSService
- RapService
- DDNSService
- iNethinkSQLBackupSvc
- CASVirtualDiskService
- CASMsgSrv
- OracleOraDb10g_homeliSQL*Plus
- OracleDBConsoleilas
- MySQL
- TPlusStdAppService1220
- TPlusStdTaskService1220
- TPlusStdUpgradeService1220
- K3MobileServiceManage
- FileZilla Server
- DDVRulesProcessor
- ImtsEventSvr
- AutoUpdatePatchService
- OMAILREPORT
- Dell Hardware Support
- SupportAssistAgent
- K3MMainSuspendService
- KpService
- ceng_web_svc_d
- KugouService
- pcas
- U8SendMailAdmin
- Bonjour Service
- Apple Mobile Device Service
- ABBYY.Licensing.FineReader.Professional.12.
- It connects to the following website to download and execute malicious module in memory:
- http://{BLOCKED}.{BLOCKED}.44.142/arx-Kbcmvm_Rrkpioky.jpg
It accepts the following parameters:
- -l -d -p {random string}: only encrypts shared files
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- desktop.ini
- ntuser.dat
- thumbs.db
- iconcache.db
- ntuser.ini
- ntldr
- bootfont.bin
- ntuser.dat.log
- bootsect.bak
- boot.ini
- autorun.inf
- debugLog.txt
It avoids encrypting files with the following strings in their file path:
- msocache
- $windows.~ws
- system volume information
- intel
- appdata
- perflogs
- programdata
- application data
- tor browser
- boot
- $windows.~bt
- mozilla
- boot
- windows.old
- Windows Microsoft.NET
- WindowsPowerShell
- Windows NT
- Windows
- Common Files
- Microsoft Security Client
- Internet Explorer
- Reference
- Assemblies
- Windows Defender
- Microsoft ASP.NET
- Core Runtime
- Package
- Store
- Microsoft Help Viewer
- Microsoft MPI
- Windows Kits
- Microsoft.NET
- Windows Mail
- Microsoft Security Client
- Package Store
- Microsoft Analysis Services
- Windows Portable Devices
- Windows Photo Viewer
- Windows Sidebar
It appends the following extension to the file name of the encrypted files:
- .avast
It avoids encrypting files with the following file extensions:
- .msstyles
- .icl
- .idx
- .rtp
- .mallox
- .sys
- .nomedia
- .dll
- .hta
- .cur
- .lock
- .cpl
- .Globeimposter-Alpha865qqz
- .ics
- .hlp
- .com
- .spl
- .msi
- .key
- .mpa
- .rom
- .drv
- .bat
- .386
- .adv
- .diangcab
- .mod
- .scr
- .theme
- .ocx
- .prf
- .cab
- .diagcfg
- .msu
- .cmd
- .ico
- .msc
- .ani
- .icns
- .diagpkg
- .deskthemepack
- .wpx
- .msp
- .bin
- .themepack
- .shs
- .nls
- .exe
- .lnk
- .ps1
- .avast
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF055
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Qawjvy = %Application Data%\Aabza\Qawjvy.exe
- Qawjvy = %Application Data%\Aabza\Qawjvy.exe
Step 6
Delete this registry key
=Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator’s help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\avast
Step 7
Search and delete this file
- %User Temp%\Dwghpjxmueqxokshkill$.bat
- C:\HOW TO RECOVER !!.TXT
- {Encrypted Directory}\RECOVERY INFORMATION.txt
Step 8
Search and delete this folder
- %Application Data%\Aabza
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.MSIL.TARGETCOMP.YXCCUTT. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
Restore this file from backup only Microsoft-related files will be restored. If this malware/grayware also deleted files related to programs that are not from Microsoft, please reinstall those programs on you computer again.
Did this description help? Tell us how we did.


