TSPY_BANCO.M
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This spyware may be dropped by other malware.
It attempts to steal information, such as user names and passwords, used when logging into certain banking or finance-related websites.
TECHNICAL DETAILS
Arrival Details
This spyware may be dropped by other malware.
Information Theft
This spyware attempts to steal information from the following banks and/or other financial institutions:
- Bradesco Net Empresa
Stolen Information
This spyware sends the data it gathers to the following email addresses via SMTP:
- {BLOCKED}1x01@uol.com.br
Drop Points
This spyware uses its own SMTP engine to send the stolen data using the following domain server:
- smtp.{BLOCKED}ol.com.br
Other Details
This spyware does the following:
- Executes the following command to unload security applications of banking software:
regsvr32 /u -s "c:\arquivos de programas\scpad\scpLIB.dll"
regsvr32 /u -s "c:\arquivos de programas\scpad\scpMIB.dll"
regsvr32 /u -s "c:\arquivos de programas\scpad\scpsssh2.dll"
regsvr32 /u -s "c:\arquivos de programas\scpad\sshib.dll"
- Intercepts dialog boxes with a title of Certificado to display the following fake message box:
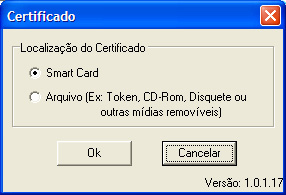
It then gathers inputs from the fake message box and sends them to a remote user via SMTP. - Connects to the following URL to possibly inform the remote user of an infection or to receive more information:
- http://bravox0005.{BLOCKED}pg.com.br/vtoken.html
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Identify and terminate files detected as TSPY_BANCO.M
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 3
Scan your computer with your Trend Micro product to delete files detected as TSPY_BANCO.M. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


