TROJ_DLOAD.BTN
Trojan.Win32.Jorik.Totem.vu (Kaspersky), PWS-Zbot.gen.ajf (McAfee)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Spammed via email
This Trojan uses London Olympics 2012 as lure to users. The email message it sends tells users of a video about a scandal. Users are redirected instead to a fake YouTube page.
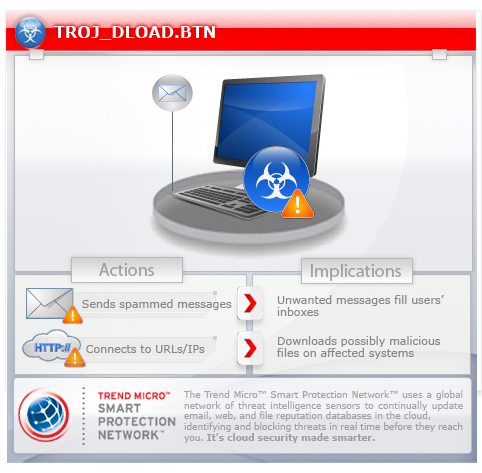
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
TECHNICAL DETAILS
66,048 bytes
EXE
Yes
04 Aug 2012
Connects to URLs/IPs, Sends messages
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
Installation
This Trojan adds the following processes:
- svchost.exe
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- "femokybhawam"
It injects itself into the following processes as part of its memory residency routine:
- previously created svchost.exe
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
femokybhawam = "%User Profile%\femokybhawam.exe"
Other System Modifications
This Trojan adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion
femokybhawam = "{malware code}"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion
AppManagement = "{hex values}"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSetServices\
Tcpip\Parameters
MaxUserPort = "dword:0000FFFE"
Other Details
This Trojan attempts to access the following websites to download files, which are possibly malicious:
- http://www.{BLOCKED}Xx.com/40E800105D592623DB4A9523B1FC5C244044B3256C00000012660000000076
00000007EB0005305CB7315B6E00000000
NOTES:
This Trojan may compose messages that can be part of its spamming routine. The messages it sends contain the following links:
- http://{BLOCKED}aard.nl/london.html
- http://{BLOCKED}es.ee/wp-content/videoaudio/temp/london.html
- http://{BLOCKED}ru.com/london.html
- http://wittdj.{BLOCKED}aradies.info/wp-content/videoaudio/temp/london.html
- http://www.{BLOCKED}use.com/wp-content/videoaudio/temp/london.html
- http://www.{BLOCKED}oevergast.nl/london.html
- http://www.{BLOCKED}on.com/temp/london.html
- http://www.{BLOCKED}o.se/london.html
It uses any of the following Simple Mail Transfer Protocol (SMTP) servers to send its messages:
- alt4.gmail-smtp-in.l.google.com
- gmail-smtp-in.l.google.com
- in1.smtp.messagingengine.com
- mail7.digitalwaves.co.nz
- mxs.mail.ru
It also attempts to connect to the following non-malicious sites:
- 0-balance-transfer.com
- 0-savings.com
- 0a3manacor.org
- 0avocat.ca
- 0c0m0y0k.de
- 0connor.com
- 0creativity.com
- 0ctober.com
- 0dayguru.com
- 0daymusic.biz
- 0daypatch.com
- 0degree.com
- 0direct.info
- 0distortion.net
- 0divide.com
- 0dollardomain.com
- 0dollarmerchantaccounts.com
- 0domainname.com
- 0downhomemortgage.com
- 0downhomemortgages.com
- 0downpmt.com
- 0downproperties.com
- 0downtime.com
- 0dutycigs.com
- 0factor.com
- 0handicap.at
- 0kommanix.de
- 0promotion.com
- 0ptical.net
- 0salvamont.ro
- 4-debt-elimination.com
- 4-elements.ch
- 4-elements.se
- 4-estateagent.com
- 4-everandaday.com
- 4-exports.gr
- 4darabians.nl
- 4dasoul.com
- 4daysinbq.com
- 4dbabamozi.hu
- 4dbenelux.be
- 4degreez.com
- 4dmobil.at
- 4dxgroup.com
- 4dzsocietiez.com
- 4e-energiezentrale.de
- 4e-ingenieria.com
- 4e-solutions.ch
- 4ebooksnow.com
- 4economics.com
- 4ecopromotions.com
- 4edgewater.com
- 4educationinformation.com
- 4eglass.com
- 4egolifestyle.de
- 4eigner.net
- 4einstitute.jp
- 4elation.com
- 4eldoradorealestate.com
- 4electrolysis.com
- 4elementdesign.com
- 4elementos.cl
- 4elementos.es
- 4elements.cz
- 4elements.de-webspace.de
- 4elements.gr
- 4elements.net
- 4elements.pl
- 4elements.us
- 4elementsaward.com
- 4elementsinaction.com
- 4eleven.com
- 4emails.de
- 4emergence.com
- 4emotion.pl
- 4emotions.de
- 4emultimedia.com
- 4enerchi.nl
- 4energia.ee
- 4engagementrings.com
- 4englishexams.com
- 4englishhotels.com
- 4equestrian.com
- 4ergindl.at
- 4esnokov.ru
- 4esport.de
- 4esports.eu
- 4esprit.com
- 4essence.eu
- 4estates.eu
- 4estatesales.com
- 4eternity.ch
- 4etverg.ru
- 4eurohouse.com
- 4euroweb.com
- 4evenmore.net
- 4events.at
- 4ever-friends.com
- 4ever-hosting.de
- 4everblessed.com
- 4evercleaning.com
- 4everdesign.com
- 4everdreams.nl
- 4everevents.nl
- 4everevolving.com
- 4everfamily.com
- 4everfloyd.com
- 4everfriends.net
- 4evergifts4u.com
- 4evergreenlawncare.com
- 4everhomes.org
- 4everkeepsakes.com
- 4everlogo.com
- 4everlost.com
- 4evermusic.pl
- 4evernew.com
- 4everone.net
- 4everphp.de
- 4everproductions.com
- 4everrose.com
- 4eversoft.hu
- 4everweb.nl
- 4everwedding.com
- 4every1.cc
- 4every1.cz
- 4everyman.com
- 4everyone.nl
- 4everyware.com
- 4everywhere.com
- 4ezdiet.com
- 4figures.info
- 6vrelay.com
- 6weekstosoccermagic.com
- 7addad-scripts.com
- 7adharat.com
- 8th1der.com
- 8toinfinity.com
- 8ung3st.de
- 8zaamarchitecten.nl
- 8zsmost.cz
- 8zstabor.taborak.cz
- 9.194.193.110.abbemae.com
- 9ktuning.com
- 9lupine.com
- 9medien.de
- 9monthproject.com
- 9nepasa.ro
- 9netweb.it
- 9neunzig.de
- 9ninehalf.com
- 9notguilty.com
- 9oakflooring.com
- 9online.fr
- 9records.com
- 9t6grafikdesign.de
- 9thstreetcharities.org
- 9vad4r95bfux.sy
- 9voltalkalinebatteries.com
- 9voltrecords.com
- 9volttaco.com
- 9wallpapers.com
- 9webhosting.net
- 9welten.de
- 9westjewelers.com
- 9wishes.com
- Running
- WinSock 2.0
- XNG74evernew.com
- accordindustries.com
- accords-bilateraux.ch
- accordtechnologies.com
- accountantskantoordekoning.nl
- accountantsvirtualservices.com
- accounting-consulting.de
- accounting-education.com
- accountingbusinessservice.com
- accountingchile.com
- accountingchum.com
- accountingcircle.com
- accountingformanagement.com
- accountingmarketing.net
- accountingsmallbusiness.net
- accountingtechs.biz
- hijsoft.ru
- shanisoft.kz
This Trojan appends 30 random characters to the aforementioned sites. This may be an indication that this Trojan might use the altered sites for other purposes.
SOLUTION
9.200
9.310.08
09 Aug 2012
9.311.00
09 Aug 2012
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product and note files detected as TROJ_DLOAD.BTN
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- femokybhawam = "%User Profile%\femokybhawam.exe"
- femokybhawam = "%User Profile%\femokybhawam.exe"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
- femokybhawam = "{malware code}"
- femokybhawam = "{malware code}"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
- AppManagement = "hex values"
- AppManagement = "hex values"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSetServices\Tcpip\Parameters
- MaxUserPort = "dword:0000FFFE"
- MaxUserPort = "dword:0000FFFE"
Step 5
Search and delete the file detected as TROJ_DLOAD.BTN
*Note: Some component files may be hidden. Please make sure you check the Search Hidden Files and Folders checkbox in the More advanced options option to include all hidden files and folders in the search result.
To manually delete a malware/grayware file from the affected system:
- Right-click Start then click Search....
- In the Named input box, type the name of the file that was detected earlier.
- In the Look In drop-down list, select My Computer then press Enter.
- Once located, select the file then press SHIFT+DELETE to delete it.
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_DLOAD.BTN. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

