Ransom.Linux.LILOCKED.THIAOAIA
Linux (64-bit)


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Other Details
This Ransomware does the following:
- It is a decryptor tool for files encrypted by LILOCKED ransomware.
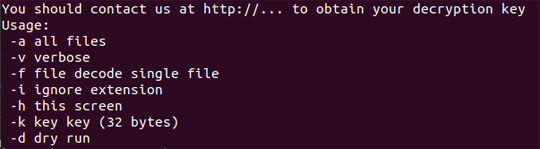
It requires a key (-k) to be used and file/s to be decrypted, together with any of the following arguments:- -a → option to decrypt all files
- -v → verbose
- -f → decrypt specified file
- -i → decrypts encrypted lilocked file, but does not restore original extension
- -k → key to be used in decrypting encrypted file, must consist of Hex values with length equal to 64 characters.
- Upon execution, it displays the following commands available which allows the user to decrypt files:
SOLUTION
Step 1
Scan your computer with your Trend Micro product to delete files detected as Ransom.Linux.LILOCKED.THIAOAIA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 2
Restore encrypted files from backup.
Did this description help? Tell us how we did.


