Microsoft: New IE Zero-Day Exploit Used in Targeted Attacks
May 26, 2014
Microsoft confirms that targeted attacks have started using a new zero-day vulnerability in Internet Explorer 6 to 11 to remotely execute arbitrary codes.
In their advisory, Microsoft warns of the remote code execution vulnerability CVE-2014-1776, which can be used to corrupt memory and allow attackers to execute whichever malicious codes they want on a vulnerable computer.
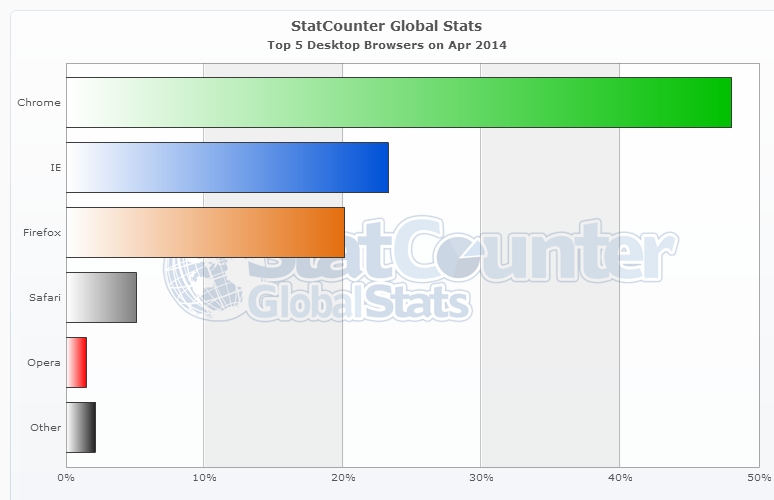
This impacts roughly 23% of all global desktop browser users who rely on varying versions of Internet Explorer for browsing.
How Attackers Can Use This
In case of a successful exploit attack, attackers are granted the same rights as the current computer user.
Microsoft further explains that attackers can host a webpages designed to exploit vulnerabilities. These pages let attackers stage web-based attacks. Attackers may then spread the word about the site using ad networks on compromised sites. They can also invite Internet users to go to these sites site via other social engineering tactics like phishing emails and instant messenger chats.
A Problem for XP Users
Microsoft is in the process of patching the vulnerability, however, for Microsoft XP users, support ended on April 8. As such, there will be no security update or technical support for the said operating system—including a patch for the new zero-day vulnerability.
Windows XP is still the second most popular desktop operating system, used on nearly a 17% of all desktop worldwide.
How Attackers Can Use This
In case of a successful exploit attack, attackers are granted the same rights as the current computer user.
Microsoft further explains that attackers can host a webpages designed to exploit vulnerabilities. These pages let attackers stage web-based attacks. Attackers may then spread the word about the site using ad networks on compromised sites. They can also invite Internet users to go to these sites site via other social engineering tactics like phishing emails and instant messenger chats.
A Problem for XP Users
Microsoft is in the process of patching the vulnerability, however, for Microsoft XP users, support ended on April 8. As such, there will be no security update or technical support for the said operating system—including a patch for the new zero-day vulnerability.
Windows XP is still the second most popular desktop operating system, used on nearly a 17% of all desktop worldwide.
HIDE
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Posted in Vulnerabilities & Exploits, Targeted Attacks
Recent Posts
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
- The Industrialization of Botnets: Automation and Scale as a New Threat Infrastructure
- From Holiday Snap to Custom Scam in 30 Minutes: How AI Turns Public Photos Into Targeted Attacks
- From LinkedIn to Tailored Attack in 30 Minutes: How AI Accelerates Target Profiling for Cybercrime

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report AI Security Starts Here: The Essentials for Every Organization
AI Security Starts Here: The Essentials for Every Organization The AI-fication of Cyberthreats: Trend Micro Security Predictions for 2026
The AI-fication of Cyberthreats: Trend Micro Security Predictions for 2026 Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One