TROJ_PIDIEF.SMZX
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This .PDF file poses as a harmless document that bore the titles "25th Annual Huntsville Post SAME Golf Tournament" and "Tibetan New Year". It specifically targets nuclear and energy sector companies.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
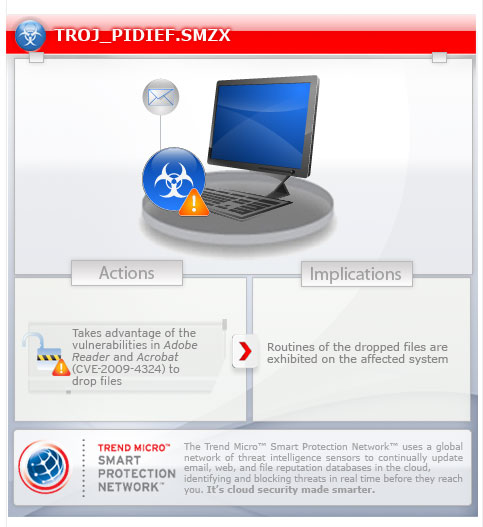
This Trojan takes advantage of the following software vulnerabilities to drop malicious files:
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users. It may be unknowingly downloaded by a user while visiting malicious websites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This Trojan drops and executes the following files:
- %User Temp%\svchost.exe - detected by Trend Micro as BKDR_PROXY.ARX
- %User Temp%\ctfmon.exe - detected by Trend Micro as TROJ_MECIV.A
Dropping Routine
This Trojan takes advantage of the following software vulnerabilities to drop malicious files:
Other Details
More information on this vulnerability can be found below:
NOTES:
The .PDF file disguises as a harmless document with the following titles:
- 25th Annual Huntsville Post SAME Golf Tournament
- Tibetan New Year
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Scan your computer with your Trend Micro product to delete files detected as TROJ_PIDIEF.SMZX. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 4
Download and apply these security patches Refrain from using these products until the appropriate patches have been installed. Trend Micro advises users to download critical patches upon release by vendors.
Did this description help? Tell us how we did.


