Ransom.MSIL.AGENDA.THJCOBD
Backdoor:MSIL/Androm.E!MTB (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
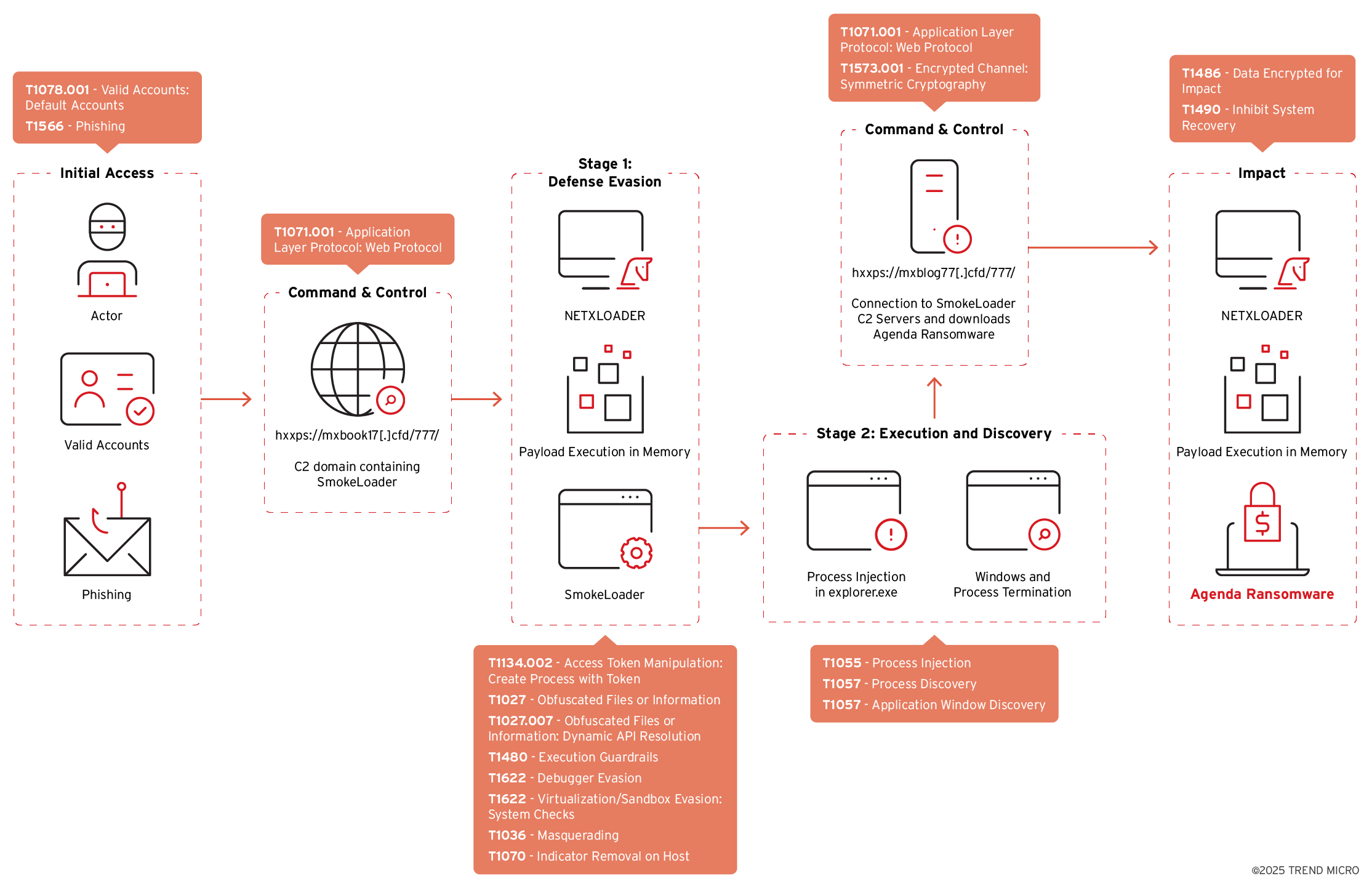
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes then deletes itself afterward.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following folders:
- %User Temp%\QLOG
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following files:
- %User Temp%\atx.bat → script to rename the first rh*.exe file it finds in the current folder to rh111.exe before executing it with specified arguments
- %User Temp%\QLOG\ThreadId({Number}).LOG → contains embedded configuration and execution logs
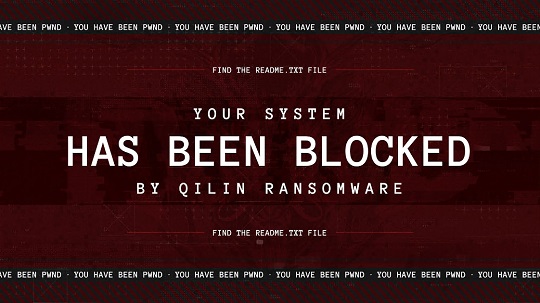
- %User Temp%\{Random Letters}.jpg → image used as desktop wallpaper
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- cmd /c ""%User Temp%\atx.bat" "
- "cmd" /C fsutil behavior set SymlinkEvaluation R2R:1
- "cmd" /C fsutil behavior set SymlinkEvaluation R2L:1
- "cmd" /C net use
- "cmd" /C wmic service where name='vss' call ChangeStartMode Manual
- "cmd" /C net start vss
- "cmd" /C vssadmin.exe delete shadows /all /quiet
- "cmd" /C net stop vss
- "cmd" /C wmic service where name='vss' call ChangeStartMode Disabled
- "powershell" $logs = Get-WinEvent -ListLog * | Where-Object {$_.RecordCount} | Select-Object -ExpandProperty LogName ; ForEach ( $l in $logs | Sort | Get-Unique ) {[System.Diagnostics.Eventing.Reader.EventLogSession]::GlobalSession.ClearLog($l)} - clears all event logs
- "powershell" -Command "Import-Module ActiveDirectory ; Get-ADComputer -Filter * | Select-Object -ExpandProperty DNSHostName"
- "powershell" -Command "ServerManagerCmd.exe -i RSAT-AD-PowerShell ; Install-WindowsFeature RSAT-AD-PowerShell ; Add-WindowsCapability -Online -Name 'RSAT.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0'"
- "reg.exe" QUERY "HKEY_USERS"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\.DEFAULT\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{USER SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{USER CLSID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{SYSTEM SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command " REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImagePath /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageUrl /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageStatus /t REG_DWORD /d 1 /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImagePath /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageUrl /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImagePath /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageUrl /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImagePath /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageUrl /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "cmd" /C timeout /T 10 & Del "{Malware Path}\{Malware Filename}"
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
It executes then deletes itself afterward.
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- 32bcf09497d3a5a77fcea9740d3bd2b2c70760cfe3aef8b4c819adb509434ead
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
*{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
Other System Modifications
This Ransomware modifies the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToLocalEvaluation = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToRemoteEvaluation = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnections = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\LanmanServer\Parameters
MaxMpxCt = 65535
(Note: The default value data of the said registry entry is {Default Value}.)
It changes the desktop wallpaper by modifying the following registry entries:
HKEY_CURRENT_USERS\Control Panel\Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image}.)
HKEY_USERS\.DEFAULT\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image}.)
HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image}.)
HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImagePath = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image Path}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image URL}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImageStatus = 1
(Note: The default value data of the said registry entry is {Default Value}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImagePath = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image Path}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
(Note: The default value data of the said registry entry is {Default Image URL}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImageStatus = 1
(Note: The default value data of the said registry entry is {Default Value}.)
It sets the system's desktop wallpaper to the following image:
Process Termination
This Ransomware terminates the following services if found on the affected system:
- (.*?)sql(.*?)
- acronisagent
- acrsch2svc
- backup
- backupexecagentaccelerator
- backupexecagentbrowser
- backupexecdivecimediaservice
- backupexecjobengine
- backupexecmanagementservice
- backupexecrpcservice
- backupexecvssprovider
- gxblr
- gxcimgr
- gxclmgrs
- gxcvd
- gxfwd
- gxmmm
- gxvss
- gxvsshwprov
- memtas
- mepocs
- msexchange
- msexchange\$
- mvarmor
- mvarmor64
- pdvfsservice
- qbcfmonitorservice
- qbdbmgrn
- qbidpservice
- sap
- sap\$
- sapd\$
- saphostcontrol
- saphostexec
- sapservice
- sophos
- sql
- veeam
- veeamdeploymentservice
- veeamnfssvc
- veeamtransportsvc
- vsnapvss
- vss
- wsbexchange
It terminates the following processes if found running in the affected system's memory:
- agntsvc
- avagent
- avscc
- bedbh
- benetns
- bengien
- beserver
- cagservice
- cvd
- cvfwd
- cvmountd
- cvods
- dbeng50
- dbsnmp
- dellsystemdetect
- encsvc
- enterpriseclient
- excel
- firefox
- infopath
- isqlplussvc
- msaccess
- mspub
- mvdesktopservice
- mydesktopqos
- mydesktopservice
- notepad
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- powerpnt
- pvlsvr
- qbcfmonitorservice
- qbdbmgrn
- qbidpservice
- raw_agent_svc
- sap
- saphostexec
- saposcol
- sapstartsrv
- sqbcoreservice
- sql
- steam
- synctime
- tbirdconfig
- teamviewer
- teamviewer_service
- thebat
- thunderbird
- tv_w32
- tv_x64
- veeamdeploymentsvc
- veeamnfssvc
- veeamtransportsvc
- visio
- vmcompute
- vmwp
- vsnapvss
- vxmon
- winword
- wordpad
- xfssvccon
Other Details
This Ransomware does the following:
- It enables the following privileges to allow access to restricted actions in the system:
- SeDebugPrivilege
- SeImpersonatePrivilege
- SeIncreaseBasePriorityPrivilege
- It creates the following named pipe:
- \.\pipe\__rust_anonymous_pipe1__.3860.{Number Count}
- It repeatedly clears all event logs in the system.
- It retrieves the DNS hostnames of all computers in an Active Directory domain before encrypting them.
- It deletes all shadow copies and disables automatic startup of Volume Shadow Copy Service
It accepts the following parameters:
- --debug → enables debugging mode
- --dry-run → tests file encryption then restores files back to original
- --escalated → run with elevated privileges
- --exclude {Host to Exclude} → excludes specified hosts when self-propagating
- --fde
- --force
- --impersonate {Account} → uses the specified account for impersonation
- --ips {IP Addresses} → encrypts hosts with specified IP addresses
- --kill-cluster → disables VM clusters
- --logs → compresses the logs into a ZIP file and saves as {Malware Path}\QLOGS.zip
- --no-admin → disables running as admin
- --no-autostart → disables creating autostart
- --no-delete → disables deleting folders
- --no-destruct → disables self-destruct
- --no-df → disables using the directory name filter
- --no-domain → disables encrypting files on domain hosts
- --no-ef → disables using the file extension filter
- --no-escalate → disables privilege escalation
- --no-extension → disables appending extension to the encrypted files
- --no-ff → disables using a filename filter
- --no-local → disables encrypting files on the local system
- --no-logs → disables logging
- --no-mounted → disables mounting drives for encryption
- --no-network → disables encrypting files on network shares
- --no-note → disables dropping ransom note
- --no-priority → disables prioritization during encryption
- --no-proc → disables process termination
- --no-sandbox → disables the detection of running in a virtual machine
- --no-services → disables stopping system services
- --no-vm → disables stopping virtual machines
- --no-wallpaper → disables setting the desktop wallpaper
- --no-zero → disables free space cleanup of host disks
- --parent-sid {SID} → passes the SID of the user of the parent process to the program
- --password {Password} → specifies a password to run the ransomware
- --paths {Directories} → encrypts files at specified paths
- --print-delay {Seconds} → delay before printing
- --print-image → enables printing the image
- --safe → reboots into safe mode before encrypting files
- --spread → enables self-propagation
- --spread-process → indicates the program that it is running in self-propagation
- --spread-vcenter → self-propagate using vCenter
- --timer {Seconds} → sets the waiting time in seconds before encryption and other actions are performed
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- #recycle
- autorun.inf
- autorun.ini
- boot.ini
- bootfont.bin
- bootmgfw.efi
- bootmgr
- bootmgr.efi
- bootsect.bak
- desktop.ini
- iconcache.db
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- thumbs.db
It avoids encrypting files found in the following folders:
- .
- ..
- $recycle.bin
- $windows.~bt
- $windows.~ws
- admin$
- appdata
- application data
- boot
- config.msi
- intel
- ipc$
- mozilla
- msocache
- netlogon
- perflogs
- program files
- program files (x86)
- programdata
- system volume information
- sysvol
- tor browser
- windows
- windows.old
It appends the following extension to the file name of the encrypted files:
- .FFzjdLtZ4C
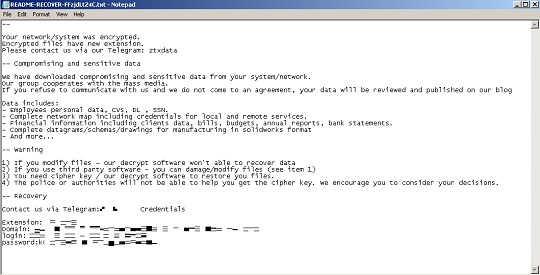
It drops the following file(s) as ransom note:
- {Encrypted Path}\README-RECOVER-FFzjdLtZ4C.txt
It avoids encrypting files with the following file extensions:
- .386
- .adv
- .ani
- .bat
- .bin
- .cmd
- .com
- .cpl
- .cur
- .deskthemepack
- .diagcab
- .diagcfg
- .diapkg
- .dll
- .drv
- .exe
- .hlp
- .hta
- .icl
- .icns
- .ico
- .ics
- .idx
- .key
- .lnk
- .lock
- .mod
- .mpa
- .msc
- .msi
- .msp
- .msstyles
- .msu
- .nls
- .nomedia
- .ocx
- .pdb
- .prf
- .ps1
- .rom
- .rtp
- .scr
- .shs
- .spl
- .sys
- .theme
- .themepack
- .wpx
- .FFzjdLtZ4C
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF086
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- *{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
- *{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
Step 6
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToLocalEvaluation = 1
- SymlinkRemoteToLocalEvaluation = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToRemoteEvaluation = 1
- SymlinkRemoteToRemoteEvaluation = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLinkedConnections = 1
- EnableLinkedConnections = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\LanmanServer\Parameters
- MaxMpxCt = 65535
- MaxMpxCt = 65535
- In HKEY_CURRENT_USERS\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\.DEFAULT\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImageStatus = 1
- LockScreenImageStatus = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImageStatus = 1
- LockScreenImageStatus = 1
Step 7
Search and delete these files
- %User Temp%\atx.bat
- %User Temp%\QLOG\ThreadId({Number}).LOG
- %User Temp%\{Random Letters}.jpg
- {Encrypted Path}\README-RECOVER-FFzjdLtZ4C.txt
Step 8
Search and delete this folder
- %User Temp%\QLOG
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.MSIL.AGENDA.THJCOBD. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
Restore encrypted files from backup.
Step 11
Reset your Desktop properties
Step 12
Scan your computer with your Trend Micro product to delete files detected as Ransom.MSIL.AGENDA.THJCOBD. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.