WORM_AGENT.VRX
Windows 2000, XP, Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm may be dropped by other malware.
TECHNICAL DETAILS
Arrival Details
This worm may be dropped by other malware.
Installation
This worm drops the following files:
- %Current%\ipz-db.bin
- %Current%\log.txt
Autostart Technique
This worm registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
Type = 10
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
Start = 2
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
ErrorControl = 0
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
ImagePath = {malware path and file name}
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
DisplayName = Intelligent P2P Zombie
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\IPZ
ObjectName = LocalSystem
Other System Modifications
This worm creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
{malware path and file name} = {malware path and file name}:*:Enabled:{malware filename}
Other Details
This worm does the following:
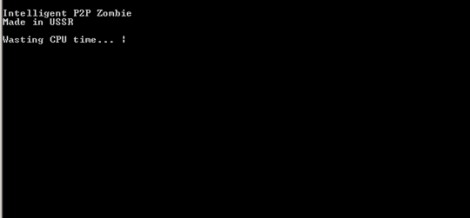
- Displays the following window upon execution:
- Sends ICMP PING requests to random IP addresses and scans for port 4899 (Radmin Port) to check if those IP addresses have RADMIN service running. Once successful, it uses the following hardcoded list of user names and passwords to gain access to password-protected systems:
- 0987654321
- 111111
- 11111111
- 121212
- 12121212
- 123123
- 12341234
- 123456
- 12345678
- 123456789
- 1234567890
- 1q2w3e
- 1q2w3e4r
- 1q2w3e4r5t
- 654321
- 87654321
- aaaaaa
- aaaaaaaa
- admin
- Admin
- administrator
- aerial
- aerodynamics
- aeroplane
- alien
- altera
- altitude
- america
- american
- anchorite
- annihilation
- archer
- asdfghjk
- asdfghjkl
- atmel
- atmosphere
- atomic
- backward
- battle
- bender
- billgates
- boeing
- brentcorrigan
- brutal
- bullshit
- burning
- callofduty
- cannon
- cdrom
- children
- computer
- coolface
- copyleft
- copyright
- creative
- creator
- darthvader
- deathcore
- deathstar
- debian
- deltaplane
- destroy
- disable
- display
- domination
- doomsday
- elephant
- elimination
- emoboy
- emokid
- emperor
- enable
- enigma
- europe
- evangellion
- fallout
- fighter
- folder
- forward
- freedom
- fuckyou
- godzilla
- gothic
- grinder
- guitar
- happiness
- happy
- hardcore
- harddisk
- helicopter
- hippie
- hitler
- horishima
- horizon
- ignore
- imageboard
- income
- incoming
- insane
- internet
- israel
- jesus
- jetpack
- kamikaze
- keyboard
- kremlin
- latitude
- lineage2
- login
- longtitude
- lucifer
- lurkmore
- machine
- memory
- metall
- microchip
- microsoft
- minigun
- missile
- monkey
- motorbike
- mouse
- mozilla
- music
- negative
- nekoboy
- nigger
- nuclear
- oracle
- overmind
- password
- people
- pilotage
- police
- positive
- predator
- pretty
- processor
- propeller
- prototype
- qazwsx
- qazwsxedc
- qqqqqq
- qqqqqqqq
- qweasd
- qweasdzxc
- qwerty
- qwertyui
- qwertyuiop
- radmin
- rastaman
- reactor
- receiver
- revolution
- rocketman
- router
- samael
- satan
- sattelite
- scientology
- secret
- secure
- shadow
- shcool
- skynet
- skywalker
- smoking
- solder
- speaker
- stalin
- starcraft
- stinger
- sunlight
- superman
- supply
- suxxxx
- terminator
- thieft
- thread
- thunderbird
- tolerance
- topsecret
- tranciever
- transmitter
- trollface
- ubuntu
- unknown
- username
- utorrent
- warcraft
- warhammer
- washington
- whitehouse
- windows
- wireless
- xlinx
- youandme
- youtube
- zeitgeist
NOTES:
This is a worm infected by PE_VIRUX.R. As such, the routines of WORM_BIZOME and PE_VIRUX. are exhibited in the affected system once executed.
May be executed using command-line and may have the following parameters:
- /l, --log - enable logging of activities
- /i, --install - install its own service
- /s, --service - restart its own service
- /r, --remove - remove its own service
- (peer_broadcast_link) broadcasting link to {IP}
- (peer_link_to_self) buddy {IP} kicked due to synchronization error
- (peer_link_to_self) synchronized link to {IP}
- (peer_new_buddy) {IP} - added new buddy
- (peer_new_buddy) {IP} - buddy already in list
- (peer_new_buddy) {IP} - connection closed
- (peer_new_buddy) {IP} - trying to connect
- (peer_process_link_message) linked to new buddy {IP}
- (peer_process_link_message) synchronized link with {IP}
- (peer_process_message) new message
- (peer_process_message) new message accepted
- (peer_process_poll_message) message delivered to {IP}
- (peer_process_poll_message) no messages to deliver to {IP}
- (peer_process_poll_message) {IP} polled his mailbox
- [{Date and Time}]#{ID} (ACT) connected to {IP}
- [{Date and Time}]#{ID} (ACT) disconnected from {IP}
- [{Date and Time}]#{ID} (ACT) failed to connect to {IP}
- [{Date and Time}]#{ID} (ACT) message delivered to {IP}
- [{Date and Time}]#{ID} (ACT) message received from {IP}
- [{Date and Time}]#{ID} (ACT) no messages on {IP}
- [{Date and Time}]#{ID} (ACT) polling mailbox on {IP}
- [{Date and Time}]#{ID} (ACT) sending messages to {IP}
- [{Date and Time}]#{ID} (ACT) trying to connect to {IP}
- [{Date and Time}]#{ID} (PASS) connection from {IP} closed
- [{Date and Time}]#{ID} (PASS) LINK from {IP}
- [{Date and Time}]#{ID} (PASS) message from {IP}
- [{Date and Time}]#{ID} (PASS) POLL from {IP}
- [{Date and Time}]#{ID} (PASS) received connection from {IP}
This malicious file builds a peer-to-peer network which may then receive and send commands from/to other infected machines/malicious networks to download and execute other malicious files.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Remove malware files dropped/downloaded by WORM_AGENT.VRX
Step 3
Scan your computer with your Trend Micro product and note files detected as WORM_AGENT.VRX
Step 4
Restart in Safe Mode
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- IPZ
- IPZ
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- {malware path and file name} = {malware path and file name}:*:Enabled:{malware filename}
- {malware path and file name} = {malware path and file name}:*:Enabled:{malware filename}
Step 7
Search and delete this file
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_AGENT.VRX. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


