TSPY_BEBLOH.MJM
Trojan.Win32.Bublik.adwm (Kaspersky), W32/Zbot.DHN!tr (Zbot
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Spyware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
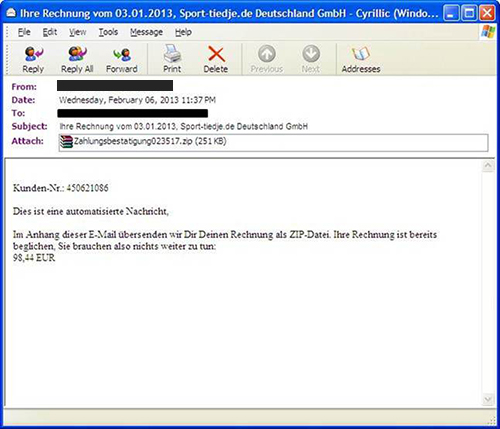
This spyware arrives onto users systems as a spoofed German invoice e-mail (payment confirmation for order).
This spyware may also use a purely random set of characters as its file name. It connects to certain servers to report system infection and send information such as OS version and IP address.
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It gathers target email addresses from the Windows Address Book (WAB).
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
Installation
This spyware drops the following copies of itself into the affected system:
- %System%\{random filename}.exe
(Note: %System% is the Windows system folder, which is usually C:\Windows\System32.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- ASWgf02
It injects itself into the following processes as part of its memory residency routine:
- csrss.exe
- thebat.exe
- msimn.exe
- iexplore.exe
- explorer.exe
- myie.exe
- firefox.exe
- mozilla.exe
- avant.exe
- maxthon.exe
- OUTLOOK.EXE
- ftpte.exe
- coreftp.exe
- filezilla.exe
- TOTALCMD.EXE
- cftp.exe
- FTPVoyager.exe
- SmartFTP.exe
- WinSCP.exe
Autostart Technique
This spyware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
userinit.exe
Debugger = "%System%\{random filename}.exe"
Other System Modifications
This spyware adds the following registry entries as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Internet Settings\
5.0\203E7401
Default = "{XOR encrypted configuration file URLs}"
It adds the following registry keys as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Internet Settings\
5.0\203E7401
Propagation
This spyware gathers target email addresses from the Windows Address Book (WAB).
Information Theft
This spyware gathers the following data:
- IP Address
- OS Version
- Socks Port
- UAC Configuration
- Hardware ID
Drop Points
Stolen information is uploaded to the following websites:
- {BLOCKED}x.com
Other Details
This spyware deletes the initially executed copy of itself
NOTES:
A screenshot of the spammed email can be found below:
The file names used for its dropped copy may contain the following strings combined with random characters:
- def
- dns
- exec
- hlp
- logon
- mem
- mixer
- mon
- pack
- play
- setup
- srv
- user
- video
- win
It may also use a purely random set of characters as filename.
It monitors URLs related to financial institutions indicated in its configuration file, as well as steal FTP credentials from the infected system. If the download is successful, it may steal login credentials and money from bank accounts and manipulate the account page to display no changes in the account balance. However, the URLs currently are not accessible.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Identify and terminate files detected as TSPY_BEBLOH.MJM
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\203E7401
- Default = "{XOR encrypted configuration file URLs}"
- Default = "{XOR encrypted configuration file URLs}"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\userinit.exe
- Debugger = "%System%\{random filename}.exe"
- Debugger = "%System%\{random filename}.exe"
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry. Before you could do this, you must restart in Safe Mode. For instructions on how to do this, you may refer to this page If the preceding step requires you to restart in safe mode, you may proceed to edit the system registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0
- 203E7401
- 203E7401
Step 5
Scan your computer with your Trend Micro product to delete files detected as TSPY_BEBLOH.MJM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


