REMCOS
Windows


Threat Type: Backdoor
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
Remcos or Remote Control and Surveillance, marketed as a legitimate software by a Germany-based firm Breaking Security for remotely managing Windows systems, is now widely used in multiple malicious campaigns by threat actors. Remcos is a sophisticated remote access Trojan (RAT) that can be used to fully control and monitor machines running on Windows XP and later.
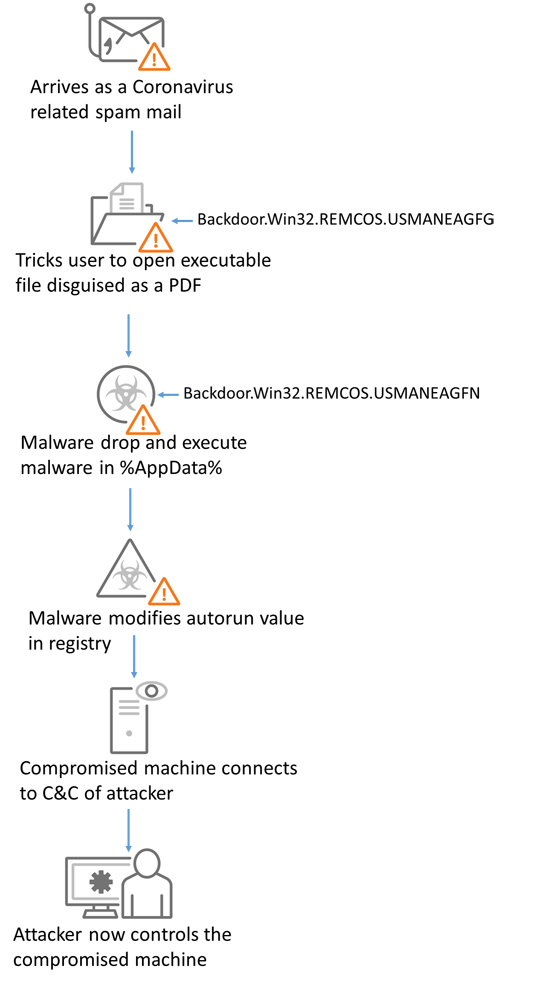
Attackers use a social engineering technique in which fake emails that appeared to be from legitimate companies . These emails contain invoices or urgent order attachments which are actually archives containing Remcos. The attachment is an archive with an executable disguised as a PDF or other document file. It attempts to connect with the attacker's command and control (C&C) server.
This backdoor gathers the following information and sends it to its servers:
- Computer information (OS version, computer name, system type, product name, primary adapter)
- User information (user access, user profile, user name, user domain)
- Processor information (processor revision number, processor level, processor identifier, processor architecture)
Its routines include:
- Bypasses anti-virus products
- Maintains persistence on the targeted machine
- Runs as legitimate process by injecting to Windows process
- Gains admin privileges and disables user account control (UAC)
It is capable of the following:
- Information Theft
- Backdoor commands
- Exploits
Remcos typically follows the infection chain below: