WORM_PROLACO.JEE
Windows 2000, XP, Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This worm arrives as attachment to mass-mailed email messages. It may be dropped by other malware. It may be unknowingly downloaded by a user while visiting malicious websites.
It adds registry entries to enable its automatic execution at every system startup.
It drops copies of itself into all the removable drives connected to an affected system. It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It also has rootkit capabilities, which enables it to hide its processes and files from the user.
It executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
TECHNICAL DETAILS
Arrival Details
This worm arrives as attachment to mass-mailed email messages.
It may be dropped by other malware.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This worm drops the following copies of itself into the affected system:
- %System%\NvTaskbarInit.exe
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Nvidia Control Center = %System%\NvTaskbarInit.exe
Other System Modifications
This worm adds the following registry entries as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\policies\
system
EnableLUA = 0
It adds the following registry keys as part of its installation routine:
HKEY_CURRENT_USER\Software\Nvideo
It creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
%System%\\NvTaskbarInit.exe = %System%\NvTaskbarInit.exe:*:Enabled:Explorer
Propagation
This worm creates the following folders in all removable drives:
- RECYCLER
- RECYCLER\S-1-6-21-2434476521-1645641927-702000330-1542
It drops copies of itself into all the removable drives connected to an affected system.
It drops the following copy(ies) of itself in all removable drives:
- redmond.exe
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
[autorun]
open=RECYCLER\S-1-6-21-2434476521-1645641927-702000330-1542\redmond.exe
icon=%SystemRoot%\system32\SHELL32.dll,4
action=Open folder to view files
shell\open=Open
shell\open\command=RECYCLER\S-1-6-21-2434476521-1645641927-702000330-1542\redmond.exe
shell\open\default=1
It gathers target email addresses from files with the following extensions:
- txt
- htm
- xml
- php
- asp
- dbx
- log
- nfo
- lst
- rtf
- xml
- wpd
- wps
- xls
- doc
- wab
It avoids sending email messages to addresses containing the following strings:
- .mil
- abuse
- acd-group
- acdnet.com
- acdsystems.com
- acketst
- admin
- ahnlab
- alcatel-lucent.com
- anyone
- apache
- arin.
- avg-comsysinternals
- avira
- badware
- berkeley
- bitdefender
- bluewin.ch
- borlan
- bpsoft.com
- bsd
- bugs
- buyrar.com
- ca
- certific
- cisco
- clamav
- contact
- debian
- drweb
- eset.com
- example
- f-secure
- fido
- firefox
- fsf.
- ghisler.com
- gimp
- gnu
- gold-certs, gov.
- help
- honeynet
- honeypot
- iana
- ibm.com
- icrosoft
- idefense
- ietf
- ikarus
- immunityinc.com
- info
- inpris
- isc.o
- isi.e
- jgsoft
- kaspersky
- kernel
- lavasoft
- linux
- listserv
- mcafee
- messagelabs
- mit.e
- mozilla
- mydomai
- nobody
- nodomai
- noone
- nothing
- novirusthanks
- ntivi
- nullsoft.org
- page
- panda
- postmaster
- prevx
- privacy
- qualys
- quebecor.com
- rating
- redhat
- rfc-ed
- root
- rusils
- sales
- samba
- samples
- secur
- security
- sendmail
- service
- site
- slashdot
- soft
- somebody
- somoeone
- sopho
- sourceforge
- spam
- spm
- ssh.com
- submit
- sun.com
- support
- suse
- syman
- tanford.e
- the.bat
- unix
- usenet
- utgers.ed
- virus
- virusbuster
- webmaster
- websense
- winamp
- wincap
- wireshark
- www.ca.com
Rootkit Capabilities
This worm also has rootkit capabilities, which enables it to hide its processes and files from the user.
Process Termination
This worm terminates the following services if found on the affected system:
- APVXDWIN
- AVG8_TRAY
- AVP
- AVP
- AntiVirSchedulerService
- Arrakis3
- BDAgent
- CAVRID
- CSIScanner
- CaCCProvSP
- DrWebScheduler
- ERSvc
- Ehttpsrv
- Emproxy
- FPAVServer
- GWMSRV
- ISTray
- K7EmlPxy
- K7RTScan
- K7SystemTray
- K7TSMngr
- K7TSStart
- LIVESRV
- MBAMService
- MCNASVC
- MPFSERVICE
- MPS9
- McENUI
- MskAgentexe
- PAVFNSVR
- PAVPRSRV
- PAVSVR
- PSHOST
- PSIMSVC
- PSKSVCRETAIL
- RSCCenter
- RSRavMon
- RavTask
- SAVScan
- SBAMTray
- SCANINICIO
- SUM
- Savadminservice
- Savservice
- SpIDerMail
- SpamBlocker
- TPSRV
- ThreatFire
- VSSERV
- WerSvc
- WinDefend
- XCOMM
- antivirservice
- avast!
- avg8emc
- avg8wd
- bdss
- ccEvtMgr
- ccproxy
- ccpwdsvc
- ccsetmgr
- cctray
- egui
- ekrn
- liveupdate
- mcODS
- mcmisupdmgr
- mcmscsvc
- mcpromgr
- mcproxy
- mcredirector
- mcshield
- mcsysmon
- msk80service
- navapsvc
- npfmntor
- nscservice
- sbamsvc
- sbamui
- scan
- sdauxservice
- sdcodeservice
- sndsrvc
- spbbcsvc
- wscsvc
- OfficeScanNT Monitor
- Spam Blocker for Outlook Express
- F-PROT Antivirus Tray application
- Windows Defender
- aswupdsv
- avast! Antivirus
- avast! Mail Scanner
- avast! Web Scanner
- McAfee HackerWatch Service
- Norton AntiVirus
- LiveUpdate Notice Service
- Symantec Core LC
- Sophos Autoupdate Service
- Sophos Agent
- Sophos Certification Manager
- Sophos Management Service
- Sophos Message Router
- PANDA SOFTWARE CONTROLLER
It terminates the following processes if found running in the affected system's memory:
- ALSvc.exe
- APvxdwin.exe
- AVENGINE.exe
- AlMon.exe
- CCenter.exe
- FPAVServer.exe
- FPWin.exe
- FprotTray.exe
- HWAPI.exe
- K7EmlPxy.exe
- K7RTScan.exe
- K7SysTry.exe
- K7TSMngr.exe
- K7TSecurity.exe
- McNASvc.exe
- McProxy.exe
- Mcshield.exe
- MpfSrv.exe
- NTRtScan.exe
- PAVSRV51.exe
- PSCtrlS.exe
- PShost.exe
- PavFnSvr.exe
- PavPrSrv.exe
- Pavbckpt.exe
- PsIMSVC.exe
- Rav.exe
- RavMon.exe
- RavStub.exe
- RavTask.exe
- RavmonD.exe
- RedirSvc.exe
- SavAdminService.exe
- SavMain.exe
- SavService.exe
- SbeConsole.exe
- SrvLoad.exe
- TPSRV.exe
- TmListen.exe
- Webproxy.exe
- ashdisp.exe
- ashserv.exe
- avcenter.exe
- avciman.exe
- avgcsrvx.exe
- avgemc.exe
- avgnt.exe
- avgrsx.exe
- avgtray.exe
- avguard.exe
- avgui.exe
- avgwdsvc.exe
- avp.exe
- avp.exe
- bdagent.exe
- bdss.exe
- ccsvchst.exe
- drweb32w.exe
- drwebupw.exe
- egui.exe
- ekrn.exe
- emproxy.exe
- guardgui.exe
- iface.exe
- isafe.exe
- livesrv.exe
- mbam.exe
- mcagent.exe
- mcmscsvc.exe
- mcods.exe
- mcpromgr.exe
- mcsysmon.exe
- mcvsshld.exe
- mps.exe
- mskagent.exe
- msksrver.exe
- pccnt.exe
- prevx.exe
- psksvc.exe
- sbamtray.exe
- sbamui.exe
- seccenter.exe
- spidergui.exe
- vetmsg.exe
- vsserv.exe
- xcommsvr.exe
Dropping Routine
This worm drops the following files:
- %System%\NvMcTray.exe - detected as TROJ_HILOTI.IB
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
It executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
Other Details
This worm connects to the following URL(s) to get the affected system's IP address:
- www.{BLOCKED}myip.com/automation/{BLOCKED}945.asp
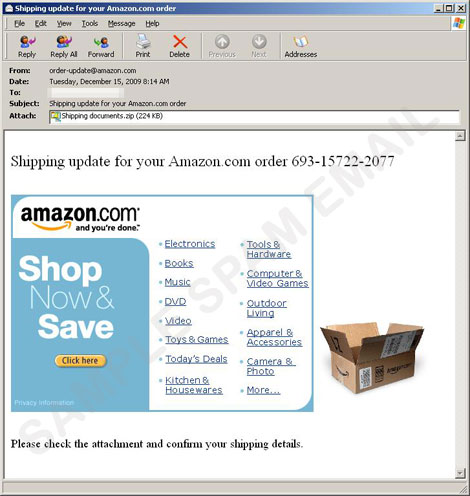
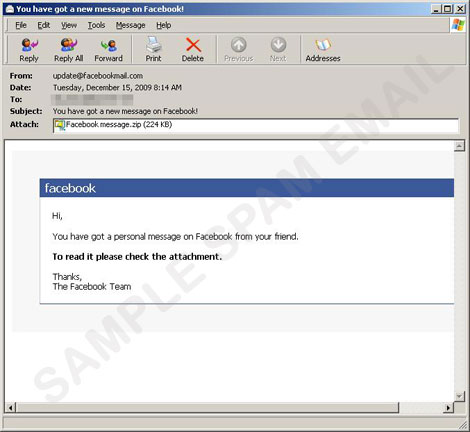
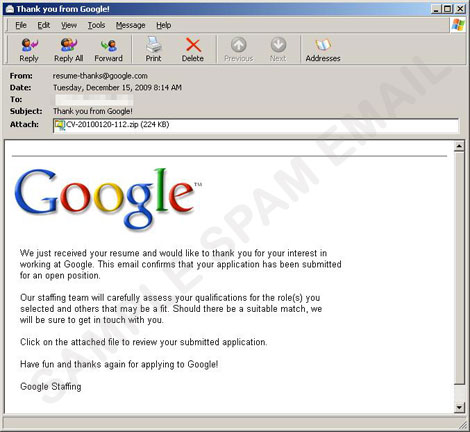
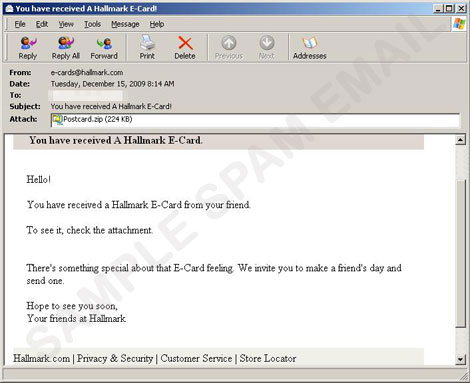
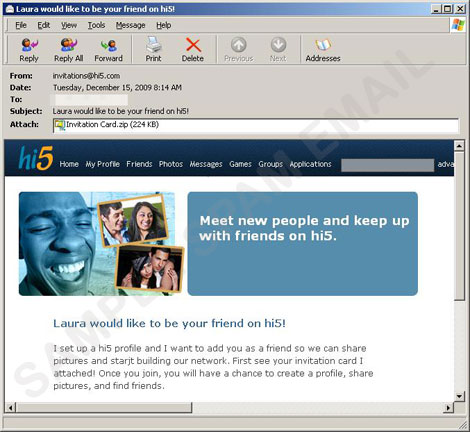
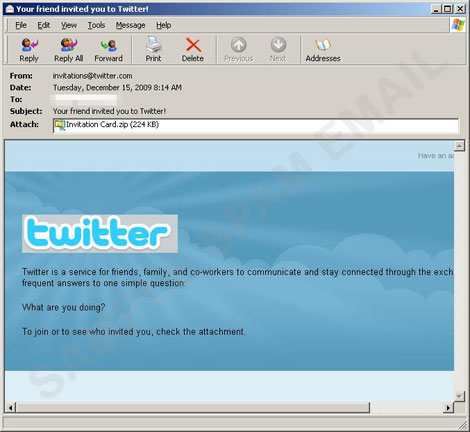
It displays the following images:
It does the following:
- It attempts to determine the SMTP Simple Mail Transfer Protocol (SMTP) server of the affected system by using the gathered domain name and the following prefixes:
- mx
- mx1
- mxs
- mail1
- relay
- ns
- gate
NOTES:
Based on analysis of the codes, it has the following capabilities:
- It uses its own Simple Mail Transfer Protocol (SMTP) engine to send email messages with a copy of itself as attachment.
- It searches for MSI files in network drives and repackages the said files with a copy of itself. The repackaged file when run, extracts and executes the original MSI file and the copy of this worm.
- It avoids sending email messages to addresses containing the following strings:
- ALSvc.exe
- APvxdwin.exe
- AVENGINE.exe
- AlMon.exe
- CCenter.exe
- FPAVServer.exe
- FPWin.exe
- FprotTray.exe
- HWAPI.exe
- K7EmlPxy.exe
- K7RTScan.exe
- K7SysTry.exe
- K7TSMngr.exe
- K7TSecurity.exe
- McNASvc.exe
- McProxy.exe
- Mcshield.exe
- MpfSrv.exe
- NTRtScan.exe
- PAVSRV51.exe
- PSCtrlS.exe
- PShost.exe
- PavFnSvr.exe
- PavPrSrv.exe
- Pavbckpt.exe
- PsIMSVC.exe
- Rav.exe
- RavMon.exe
- RavStub.exe
- RavTask.exe
- RavmonD.exe
- RedirSvc.exe
- SavAdminService.exe
- SavMain.exe
- SavService.exe
- SbeConsole.exe
- SrvLoad.exe
- TPSRV.exe
- TmListen.exe
- Webproxy.exe
- ashdisp.exe
- ashserv.exe
- avcenter.exe
- avciman.exe
- avgcsrvx.exe
- avgemc.exe
- avgnt.exe
- avgrsx.exe
- avgtray.exe
- avguard.exe
- avgui.exe
- avgwdsvc.exe
- avp.exe
- avp.exe
- bdagent.exe
- bdss.exe
- ccsvchst.exe
- drweb32w.exe
- drwebupw.exe
- egui.exe
- ekrn.exe
- emproxy.exe
- guardgui.exe
- iface.exe
- isafe.exe
- livesrv.exe
- mbam.exe
- mcagent.exe
- mcmscsvc.exe
- mcods.exe
- mcpromgr.exe
- mcsysmon.exe
- mcvsshld.exe
- mps.exe
- mskagent.exe
- msksrver.exe
- pccnt.exe
- prevx.exe
- psksvc.exe
- sbamtray.exe
- sbamui.exe
- seccenter.exe
- spidergui.exe
- vetmsg.exe
- vsserv.exe
- xcommsvr.exe
SOLUTION
Step 1
For Windows ME and XP users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Identify and delete files detected as WORM_PROLACO.JEE using either the Startup Disk or Recovery Console
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Nvidia Control Center = %System%\NvTaskbarInit.exe
- Nvidia Control Center = %System%\NvTaskbarInit.exe
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system
- EnableLUA = 0
- EnableLUA = 0
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- %System%\NvTaskbarInit.exe = %System%\NvTaskbarInit.exe:*:Enabled:Explorer
- %System%\NvTaskbarInit.exe = %System%\NvTaskbarInit.exe:*:Enabled:Explorer
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer"s registry. Before you could do this, you must restart in Safe Mode. For instructions on how to do this, you may refer to this page If the preceding step requires you to restart in safe mode, you may proceed to edit the system registry.
- In HKEY_CURRENT_USER\Software\
- Nvideo
- Nvideo
Step 6
Search and delete these folders
- {Removable Drive}:\RECYCLER
Step 7
Search and delete AUTORUN.INF files created by WORM_PROLACO.JEE that contain these strings
Step 8
Scan your computer with your Trend Micro product to delete files detected as WORM_PROLACO.JEE If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 9
Restore this file from backup Only Microsoft-related files will be restored. If this malware/grayware/spyware also deleted files related to programs that are not from Microsoft, please reinstall those programs on your computer again. Modified MSI files
Did this description help? Tell us how we did.