Ransom.Win32.STOP.YXDEZZ
Trojan-Ransom.Win32.Stop.gen (KASPERSKY)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to a website to send and receive information.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %User Temp%\delself.bat ← deletes the malware if it is found to be executing on a system that is located in particular countries
- %System%\Tasks\Time Trigger Task ← creates scheduled task for the malware
- %AppDataLocal%\bowsakkdestx.txt → contains the public key and system encryption identifier, deleted afterwards
- %System Root%\SystemID\PersonalID.txt ← unique identifier for the affected system
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.)
It drops the following copies of itself into the affected system:
- %AppDataLocal%\{UUID 1}\{Malware File Name}.exe
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- icacls "%AppDataLocal%\{UUID 1}" /deny *S-1-1-0:(OI)(CI)(DE,DC) ← protect this path/folder
- %AppDataLocal%\{UUID 1}\{Malware File Name} --Admin IsNotAutoStart IsNotTask
- %AppDataLocal%\{UUID 1}\{Malware File Name}
- %AppDataLocal%\{UUID 2}\build2.exe
- %AppDataLocal%\{UUID 2}\build3.exe
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It creates the following folders:
- %AppDataLocal%\{UUID 1}
- %AppDataLocal%\{UUID 2}
- %System Root%\SystemID
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- {1D6FC66E-D1F3-422C-8A53-C0BBCF3D900D}
- {FBB4BCC6-05C7-4ADD-B67B-A98A697323C1}
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
SysHelper = "%AppDataLocal%\{UUID 1}\{Malware File Name}" --AutoStart
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion
SysHelper = 1
Backdoor Routine
This Ransomware connects to the following websites to send and receive information:
- http://{BLOCKED}q.com/test1/get.php?pid={MAC ADDRESS HASH} ← used to receive public key and system encryption identifier for the affected system
Download Routine
This Ransomware connects to the following website(s) to download and execute a malicious file:
- http://{BLOCKED}my.com/dl/build2.exe
- %AppDataLocal%{UUID 2}\build2.exe ← detected as TrojanSpy.Win32.VIDAR.YXDE4Z
- http://{BLOCKED}q./files/1/build3.exe
- %AppDataLocal%{UUID 2}\build3.exe ← detected as Trojan.Win32.CLIPBANKER.R002C0DID22
Other Details
This Ransomware connects to the following URL(s) to get the affected system's IP address:
- https://{BLOCKED}i.2ip.ua/geo.json
It does the following:
- It terminates and deletes itself on the affected system if the affected system's location is any of the following:
- "RU" - Russia
- "BY" - Belarus
- "UA" - Ukraine
- "AZ" - Azerbaijan
- "AM" - Armenia
- "TJ" - Tajikistan
- "KZ" - Kazhakstan
- "KG" - Kyrgyzstan
- "UZ" - Uzbekistan
- "SY" - Syria
- I:\5d2860c89d774.jpg
It accepts the following parameters:
- --Admin → the malware is executed with admin privileges
- --AutoStart → the malware is executed using autorun registry key(s)
- --Task ← the malware is executed using the created scheduled task
- IsAutoStart/IsNotAutoStart → executes malware as an autostart or not
- IsTask/IsNotTask → executes malware as a scheduled task or not
It adds the following scheduled tasks:
- Task name: Time Trigger Task
Task to be run: %AppDataLocal%\{UUID 1}\{Malware File Name} --Task
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- ntuser.pol
- ntuser.dat.LOG1
- ntuser.dat.LOG2
- ntuser.dat
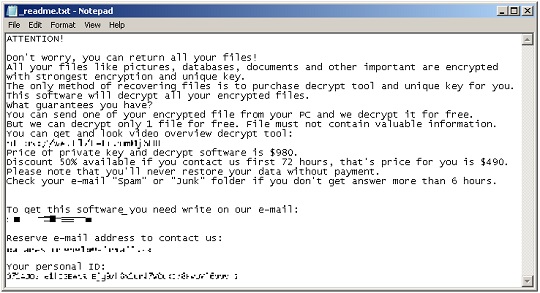
- _readme.txt
It appends the following extension to the file name of the encrypted files:
- .vaze
It drops the following file(s) as ransom note:
- {Encrypted Directory}\_readme.txt
It avoids encrypting files with the following file extensions:
- .regtrans-ms
- .lnk
- .bat
- .blf
- .dll/.DLL
- .ini
- .sys
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
-
Ransom.Win32.TRX.XXPE50FFF068
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Deleting Scheduled Tasks while in Safe Mode
- Still in safe mode, the following {Task Name}-{Task to be run} listed should be used in the steps identified below:
- Task name: Time Trigger Task
Task to be run: %AppDataLocal%\{UUID 1}\{Malware Filename}.exe --Task
- Task name: Time Trigger Task
- For Windows 7 and Server 2008 (R2) users, click Start>Computer.
- For Windows 8, 8.1, 10, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %System%\Tasks\{Task Name}
- Once located, select the file then press SHIFT+DELETE to delete it.
- Open Registry Editor. To do this:
- For Windows 7 and Server 2008 (R2) users, click the Start button, type regedit in the Search input field, and press Enter.
- For Windows 8, 8.1, 10, and Server 2012 (R2) users, right-click on the lower left corner of the screen, click Run, type regedit in the text box
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- Locate the created entry and take note of the registry value's data:
- ID={Task Data}
- After taking note of the data, delete the registry key:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tasks
- Still in the left panel, locate and delete the registry key with the same name as the located Task Data in step #6:
- ={Task Data}
- Close Registry Editor.
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
- SysHelper = 1
- SysHelper = 1
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- SysHelper = %AppDataLocal%\{UUID 1}\{Malware File Name}.exe --AutoStart
- SysHelper = %AppDataLocal%\{UUID 1}\{Malware File Name}.exe --AutoStart
Step 7
Search and delete this file
- %System Root%\SystemID\PersonalID.txt
- %AppDataLocal%\{UUID 1}\{Malware File Name}.exe
- %AppDataLocal%\{UUID 2}\build2.exe
- %AppDataLocal%\{UUID 2}\build3.exe
- %AppDataLocal%\bowsakkdestx.txt
- %User Temp%\delself.bat
- %System%\Tasks\Time Trigger Task
- {Encrypted Directory}\_readme.txt
Step 8
Search and delete these folders
- %System Root%\SystemID
- %AppDataLocal%\{UUID 1}
- %AppDataLocal%\{UUID 2}
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.STOP.YXDEZZ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
Restore encrypted files from backup.
Did this description help? Tell us how we did.


